The Great Firewall of China (GFW) has started selectively blocking QUIC protocol connections based on the Server Name Indication (SNI) in April 2024 by decrypting and inspecting QUIC Initial packets, revealing a unique and resource-intensive censorship mechanism. Researchers identified a vulnerability allowing attackers to exploit this censorship system to block UDP traffic between arbitrary hosts in China and the outside world and collaborated with various communities to implement circumvention techniques. #GreatFirewallOfChina #QUIC #QUICSNI #DNSblocklist
Keypoints
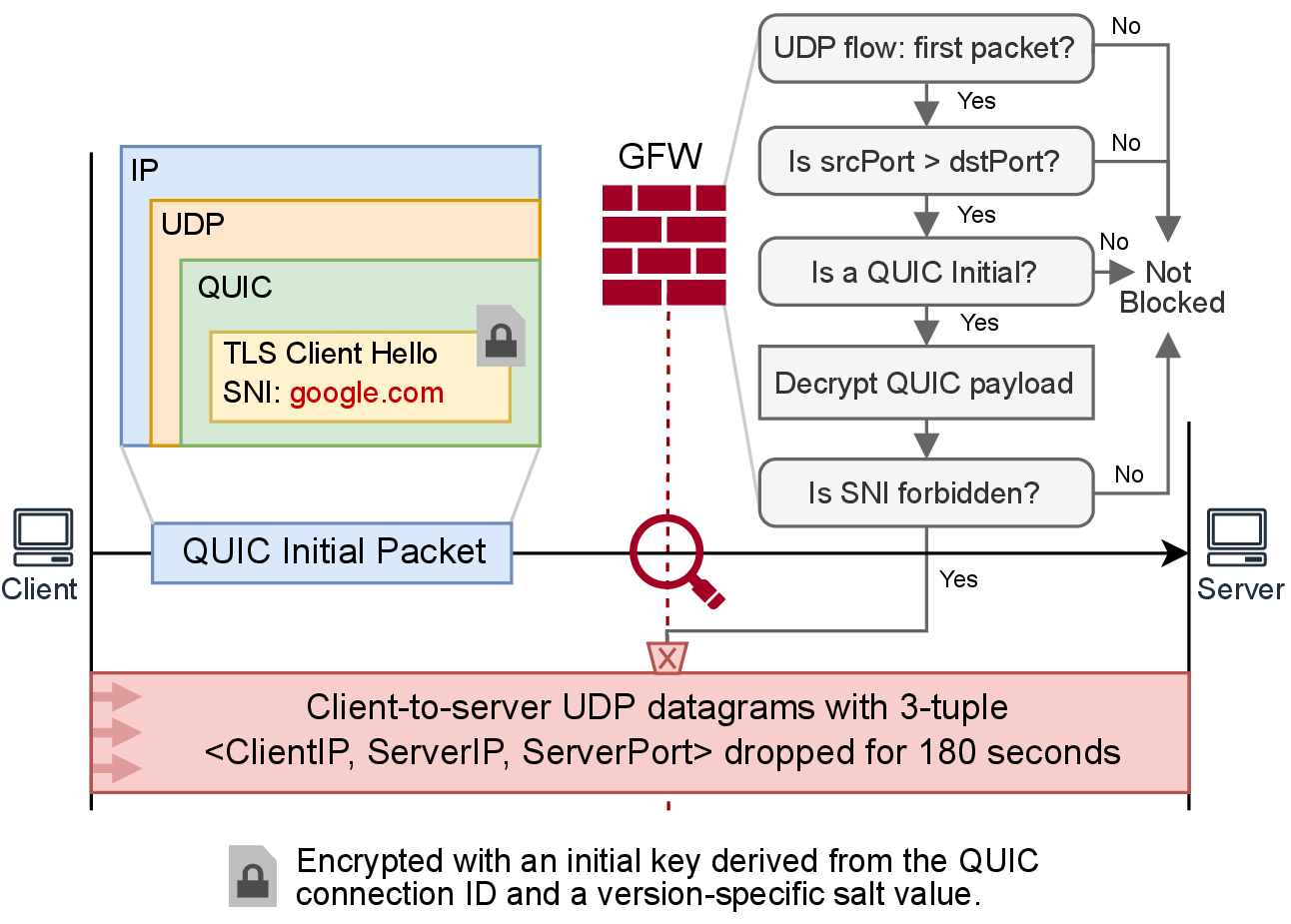
- The GFW decrypts QUIC Initial packets to access and block connections based on forbidden SNI values, marking a first nation-wide targeted censorship of QUIC.
- The censorship applies packet-dropping for 3 minutes on UDP flows matching blocked SNI and is triggered by a single QUIC Initial packet.
- The GFW uses heuristic filtering, including ignoring packets where source port is less than or equal to destination port, to reduce computational overhead.
- Blocking effectiveness shows a diurnal pattern, being less effective during high network usage due to resource constraints in decrypting QUIC traffic.
- The QUIC censorship device is co-located with existing GFW infrastructure but uses a distinct blocklist from TLS, HTTP, and DNS censorship.
- The GFW’s QUIC censor does not reassemble fragmented QUIC Initial packets, enabling circumvention techniques such as SNI slicing and connection migration.
- A vulnerability allows attackers capable of IP spoofing to induce residual blocking that can be weaponized to disrupt UDP communication at scale, including DNS traffic.
MITRE Techniques
- [T1040] Network Sniffing – The GFW decrypts QUIC Initial packets to inspect encrypted SNI fields (‘GFW decrypts QUIC Initial packets at scale, applies heuristic filtering rules’).
- [T1071] Application Layer Protocol – The censor inspects the QUIC handshake’s Client Initial packet to identify destinations (‘block QUIC connections based on client Initial SNI’).
- [T1189] Drive-by Compromise – Implicit blocking through packet dropping triggered by single packets with blocked SNI (‘a single QUIC client Initial packet containing a forbidden SNI triggers residual blocking’).
- [T1499] Endpoint Denial of Service – Residual blocking leads to denial of UDP communication between hosts due to spoofed packets (‘weaponized to block UDP traffic between arbitrary hosts inside China and the rest of the world’).
- [T1573] Encrypted Channel – The censor’s challenge arises from QUIC encrypting handshake packets (‘QUIC encrypts all packets, making censorship challenging’).
Indicators of Compromise
- [Blocked Domains] QUIC-specific SNI blocklist includes google.com, googlevideo.com subdomains, hrw.org, youtube.com, tiktok.com, and approximately 58,207 FQDNs identified from the Tranco list.
- [Blocked Ports] Blocking is effective only when source port > destination port; commonly destination port 443 is targeted while source ports are ephemeral and higher.
- [Attack IP Addresses] Examples include spoofed IPs from 32 AWS EC2 global regions such as Sydney, Singapore, Hong Kong (unaffected), and others heavily affected (e.g., Hyderabad, Calgary, London).
Read more: https://gfw.report/publications/usenixsecurity25/en/