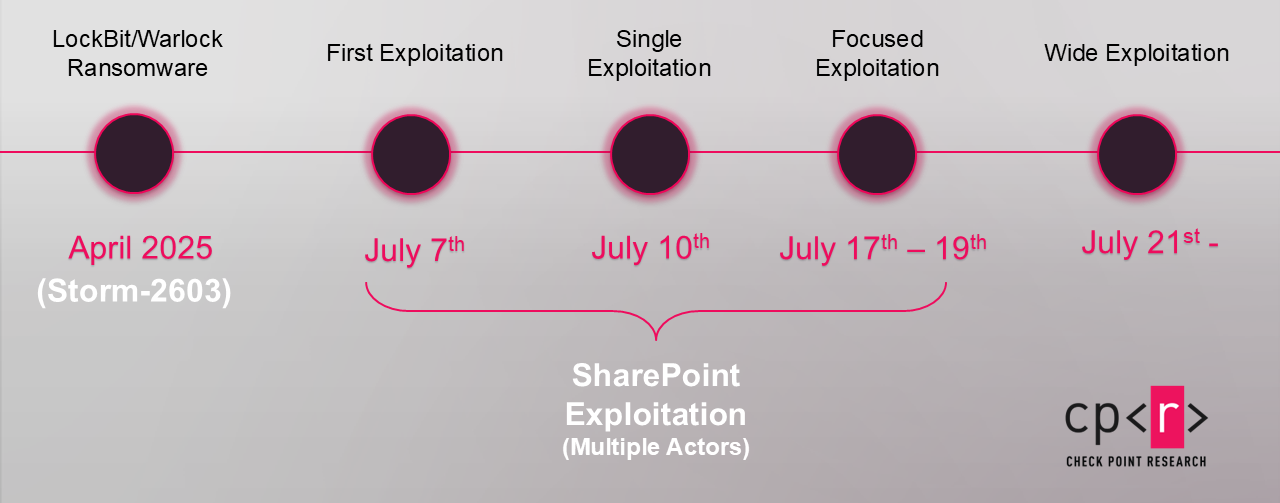
Storm-2603 is a newly identified Chinese-affiliated threat actor leveraging the ToolShell SharePoint vulnerabilities using a custom malware framework called ak47c2 to deploy multiple ransomware variants including LockBit Black and Warlock/x2anylock. The actor employs sophisticated techniques such as DNS and HTTP-based backdoors, BYOVD for disabling endpoint protections, and DLL hijacking for ransomware deployment. #Storm2603 #ak47c2 #ToolShell #LockBitBlack #WarlockRansomware
Keypoints
- Storm-2603 is a newly observed Chinese-affiliated threat actor involved in exploiting Microsoft SharePoint Server vulnerabilities under the ToolShell campaign.
- The group uses a custom Command and Control framework named ak47c2 with both DNS-based (ak47dns) and HTTP-based (ak47http) backdoors.
- Storm-2603 has deployed multiple ransomware families simultaneously, including LockBit Black and Warlock/x2anylock, often via DLL hijacking.
- The attackers leverage open-source tools like PsExec, masscan, WinPcap, and use BYOVD techniques to disable endpoint protections through a custom antivirus terminator tool.
- The group reuses infrastructure, including C2 domains such as update.updatemicfosoft[.]com, dating back to campaigns from March 2025 in Latin America and APAC regions.
- The antivirus terminator tool abuses a signed legitimate driver (ServiceMouse.sys) from Antiy Labs to kill antivirus processes on infected hosts.
- Storm-2603’s ransomware notes have consistent naming conventions and contact methods, signaling organized ransom demands across infections.
MITRE Techniques
- [T1210] Exploitation of Remote Services – Using Microsoft SharePoint Server vulnerabilities CVE-2025-49704, CVE-2025-49706, CVE-2025-53770, and CVE-2025-53771 for initial compromise (‘ongoing exploitation of a group of Microsoft SharePoint Server vulnerabilities’).
- [T1105] Ingress Tool Transfer – Use of custom malware framework ak47c2 for deploying backdoors and ransomware payloads (‘custom backdoor used by the group… communicating over DNS tunneling or HTTP’).
- [T1071.001] Application Layer Protocol: Web Protocols – HTTP-based C2 communications with the ak47http backdoor (‘builds a JSON object… sent in an HTTP POST request to the C2 server’).
- [T1071.004] Application Layer Protocol: DNS – DNS tunneling for C2 communication via ak47dns (‘builds a DNS-based command-and-control payload… queries to update.micfosoft[.]com’).
- [T1218] Signed Binary Proxy Execution – DLL hijacking used to load malicious payloads such as LockBit Black and Warlock/x2anylock ransomware (‘ransomware deployed via DLL hijacking’).
- [T1055] Process Injection – Use of vulnerable drivers to interfere with antivirus processes (‘custom Antivirus Terminator abusing third-party signed legitimate driver to kill processes’).
- [T1086] PowerShell – Use of command execution with cmd.exe /c for running commands received from C2 (‘commands run under cmd.exe /c 2>&1’).
Indicators of Compromise
- [Domain] Command and Control infrastructure – update.updatemicfosoft[.]com (C2 for DNS and HTTP backdoors).
- [File Name] Ransomware payloads – Evidencia.rar (archive containing custom backdoors and ransomware components), bbb.msi (installer launching DLL hijacking deployment), dnsclient.exe (custom DNS backdoor).
- [File Hash] Malware samples and installers (various MSI and executable files uploaded to VirusTotal in April 2025 associated with Storm-2603, such as Warlock and LockBit Black related files).
- [Driver] Vulnerable signed driver – ServiceMouse.sys, signed component abused to kill antivirus processes.
- [Email] Ransomware support contact emails – multiple proton.me addresses used in ransom notes (e.g., [redacted]@proton.me).