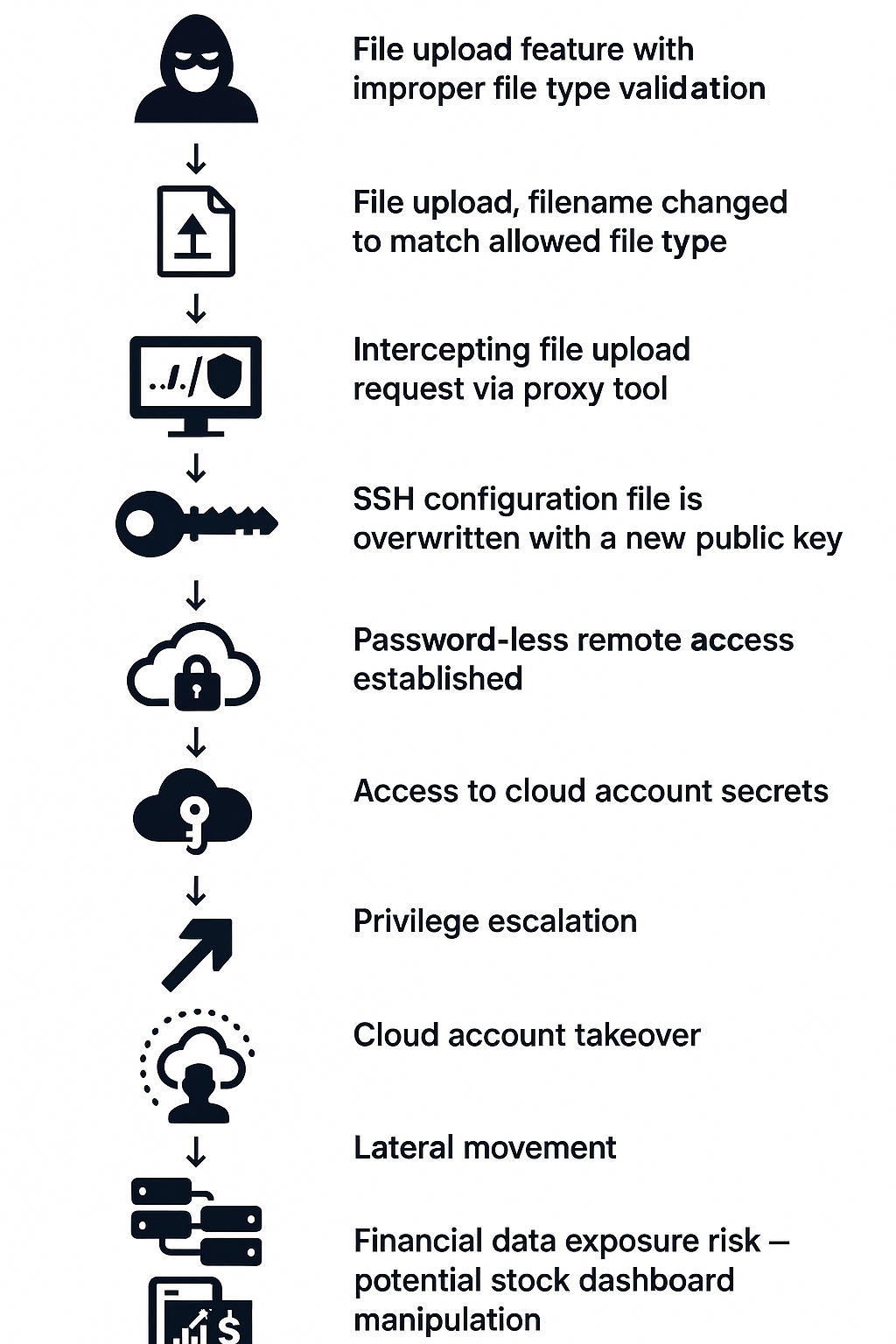
A vulnerability in Streamlit’s file upload feature allows threat actors to bypass file type restrictions and take over misconfigured cloud instances, risking manipulation of financial data dashboards. The flaw stems from client-side enforcement without backend validation, which can be exploited for cloud account takeover and stock market disruption. #Streamlit #CloudAccountTakeover #FinancialDashboards
Keypoints
- Streamlit’s file upload widget (st.file_uploader) enforced file-type restrictions only on the client side, lacking backend validation.
- This vulnerability enables attackers to upload malicious files by bypassing frontend file-type filters.
- Attackers can exploit misconfigured cloud instances running Streamlit apps to overwrite sensitive files (e.g., authorized_keys) and gain SSH access.
- The exploit can lead to cloud account takeover, exposing sensitive data and allowing tampering with financial dashboards displaying stock market data.
- Streamlit released a patch (version 1.43.2) adding backend file-type validation after responsible disclosure by Cato Networks.
- Streamlit does not consider the issue a security vulnerability, placing responsibility on developers for secure handling of uploads.
- Cato Networks enhanced threat detection within its SASE Cloud Platform to detect unauthorized file upload bypass and directory traversal attempts.
MITRE Techniques
- [T1105] Ingress Tool Transfer – Attackers upload malicious files by bypassing client-side file-type restrictions to gain initial access. (‘Threat actor intercepts and manipulates upload requests to bypass UI restriction’)
- [T1190] Exploit Public-Facing Application – Misconfigured Streamlit instances deployed publicly enable exploitation. (‘Threat actor discovers publicly accessible Streamlit application with upload capability’)
- [T1078] Valid Accounts – Using overwritten authorized_keys files, attackers gain passwordless SSH access. (‘Upload file to overwrite .ssh/authorized_keys and obtain SSH access’)
- [T1210] Exploitation of Remote Services – Remote shell access is achieved via SSH after file overwrite. (‘Threat actor now has passwordless SSH access’)
- [T1531] Account Access Removal – Attackers manipulate cloud environment credentials post-compromise. (‘Access metadata, extract IAM roles, and list IAM users’)
Indicators of Compromise
- [File Name] Malicious uploads targeting sensitive paths – ../../.ssh/authorized_keys used to overwrite SSH keys.
- [File Hashes] Examples of malicious files renamed to bypass filters (e.g., malicious.exe disguised as .pdf) referenced in demonstration (specific hashes not provided).
- [IP Addresses] Public IP addresses of misconfigured cloud instances running Streamlit applications (specific addresses not disclosed).
Read more: https://www.catonetworks.com/blog/cato-ctrl-new-streamlit-vulnerability/