On June 20th, two rarely used Toptal open source packages, Picasso and Xene, were briefly compromised due to old leaked credentials from LastPass. The malicious code was quickly removed, with no known impact to users, data, or systems. Reports of “5,000 downloads” were caused by automated security scanners, not real usage. The issue was contained swiftly, and enhanced security measures have since been implemented.
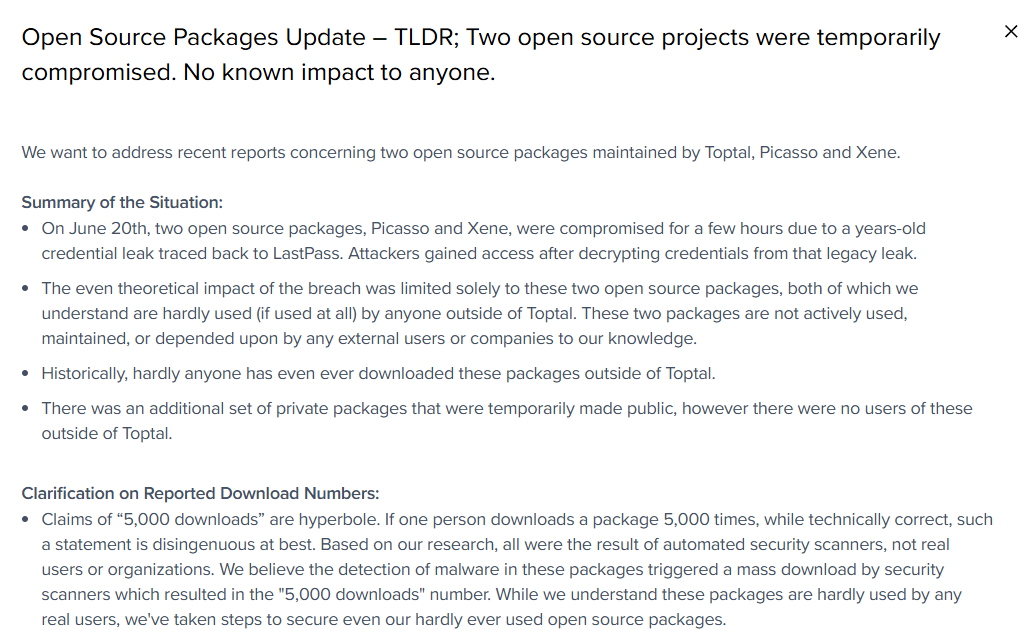
Open Source Packages Update – TLDR; Two open source projects were temporarily compromised. No known impact to anyone.
We want to address recent reports concerning two open source packages maintained by Toptal, Picasso and Xene.
Summary of the Situation:
- On June 20th, two open source packages, Picasso and Xene, were compromised for a few hours due to a years-old credential leak traced back to LastPass. Attackers gained access after decrypting credentials from that legacy leak.
- The even theoretical impact of the breach was limited solely to these two open source packages, both of which we understand are hardly used (if used at all) by anyone outside of Toptal. These two packages are not actively used, maintained, or depended upon by any external users or companies to our knowledge.
- Historically, hardly anyone has even ever downloaded these packages outside of Toptal.
- There was an additional set of private packages that were temporarily made public, however there were no users of these outside of Toptal.
Clarification on Reported Download Numbers:
- Claims of “5,000 downloads” are hyperbole. If one person downloads a package 5,000 times, while technically correct, such a statement is disingenuous at best. Based on our research, all were the result of automated security scanners, not real users or organizations. We believe the detection of malware in these packages triggered a mass download by security scanners which resulted in the “5,000 downloads” number. While we understand these packages are hardly used by any real users, we’ve taken steps to secure even our hardly ever used open source packages.
Analysis and Observations:
- The compromised code was available only for a few hours before immediate detection and removal by our security team.
- Server logs from the server hosting the malicious webhook, which Toptal was able to analyze and receive, showed that 17 unique IP addresses accessed the server where the webhook was hosted. This is the upper limit of how many users could even theoretically have been impacted. Based on our research, we’ve concluded these are either automated security scanners and research tools, not real users of the open source packages.
- No partners, customers, users, or third-party projects are known to depend on these packages, either currently or historically.
- Based on historical statistics, we average approximately 0 downloads per week for Picasso and Xene combined from GitHub or NPM. Even 17 unique users would be astronomically high to have that many downloads or updates occur within a few hours, let alone a week.
- The webhook was shut down on July 24th, and data from the server logs where the webhook was hosted only received data up until July 22nd.
Impact and Response:
- No Toptal customer, company, or individual was affected by this incident.
- No Toptal data was accessed or deleted, and our core systems remain secure.
- The affected open source packages and repositories were restored from clean backups immediately, and the attacker’s webhook was promptly shut down.
Looking Forward:
- We have already implemented further security enhancements and continue to monitor all our open source projects, even our now unused ones.
To reiterate:
To our knowledge, no users, companies, or projects outside Toptal ever used or depended on the affected open source packages. There has been zero known impact on any external parties.
If you have further questions or concerns, please contact [email protected]