SentinelLABS uncovered cryptocurrency scams using malicious smart contracts disguised as trading bots to steal over $900,000 from victims. These scams exploit aged YouTube accounts and AI-generated videos to create false legitimacy and manipulate users into deploying harmful contracts. #SmartContractScam #JazzBraze #MEVBot
Keypoints
- Threat actors distribute weaponized Solidity smart contracts through YouTube videos, posing as crypto trading bots to steal funds.
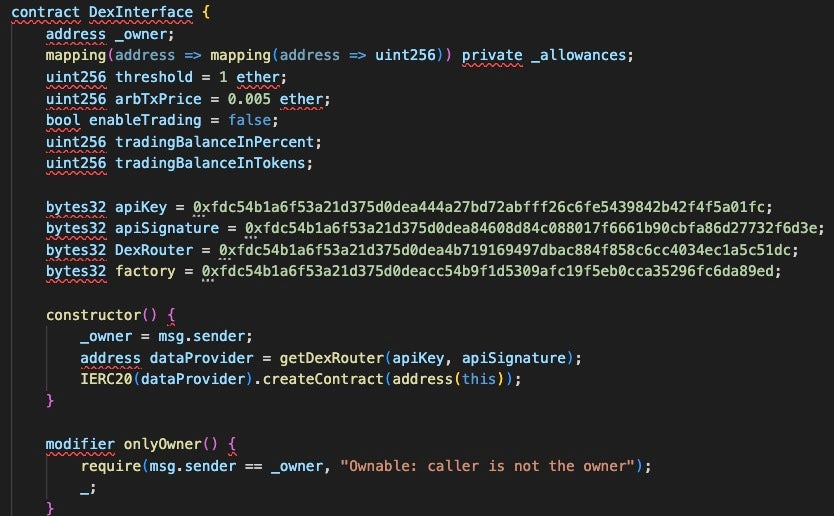
- The smart contracts use advanced obfuscation techniques such as XOR, string concatenation, and decimal-to-hex conversions to conceal attacker wallet addresses.
- Aged YouTube accounts and AI-generated video content are leveraged to build credibility and disseminate the scam effectively.
- Victims are instructed to deploy smart contracts and fund them with ETH, enabling attackers to later withdraw these funds via obfuscated owner addresses.
- The most successful scam linked to the Jazz_Braze channel resulted in over 244.9 ETH (~$902,000 US) stolen from victims.
- Comments on scam videos are heavily moderated to remove negative feedback, fostering a misleading positive environment.
- Indicators of compromise include specific Solidity contract hashes, hosting URLs, and attacker Ethereum EOAs used to track scam activity.
MITRE Techniques
- [T1027] Obfuscated Files or Information – The smart contracts use obfuscation techniques like XOR operations and string concatenation to hide the attacker’s wallet address (‘The attacker-controlled wallet address is obfuscated in each smart contract…using XOR, string concatenation, and large decimal to hex conversions’).
- [T1190] Exploit Public-Facing Application – Victims are tricked into deploying malicious smart contracts via unverified YouTube videos and external links (‘The scams are marketed through YouTube videos…the video descriptions share a link to an external site that hosts the weaponized smart contract code’).
- [T1606] Forge Web Credentials – Actors use aged YouTube accounts and AI-generated content to forge credibility and deceive users (‘The scam videos show a considerable amount of effort focused on aging the YouTube accounts…Several videos appear to be AI-generated…’).
- [T1110] Brute Force / Password Guessing (indirectly) – Comment moderation features filter out negative feedback to maintain positive comments on scam videos (‘…the actors are likely managing the YouTube comment section to delete any negative comments’).
- [T1499] Endpoint Denial of Service (Failover mechanism) – The smart contracts contain failover code allowing attackers to withdraw funds even if the victim does not trigger the primary function (‘…contract contains a failover mechanism that allows the attacker to withdraw funds that have been sent to the contract’).
Indicators of Compromise
- [File Hashes] Solidity malicious smart contracts – 2923cdf2caba3a92e0ea215d14343ce73e8f08a5 (JazzBraze video), 47d567e799f0403bcd4057bff50244125cac926a (ToddTutorials video), and 4 more hashes.
- [URLs] Hosting weaponized smart contract code – hxxps://pastebin[.]com/raw/8Yar7QyU (ToddTutorials), hxxps://codeshare[.]io/0bV94e (Jazz_Braze), and 2 more URLs.
- [Ethereum EOAs] Attacker wallet addresses involved in fund theft – 0x872528989c4D20349D0dB3Ca06751d83DC86D831 (JazzBraze scam), 0x2eEE3A0ed51AE22813050212E8D9Fa216bd51df4 (ToddTutorials), 0x7359EA6AA3343b3238171e76F97e6aA3cDB8d696 (SolidityTutorials).