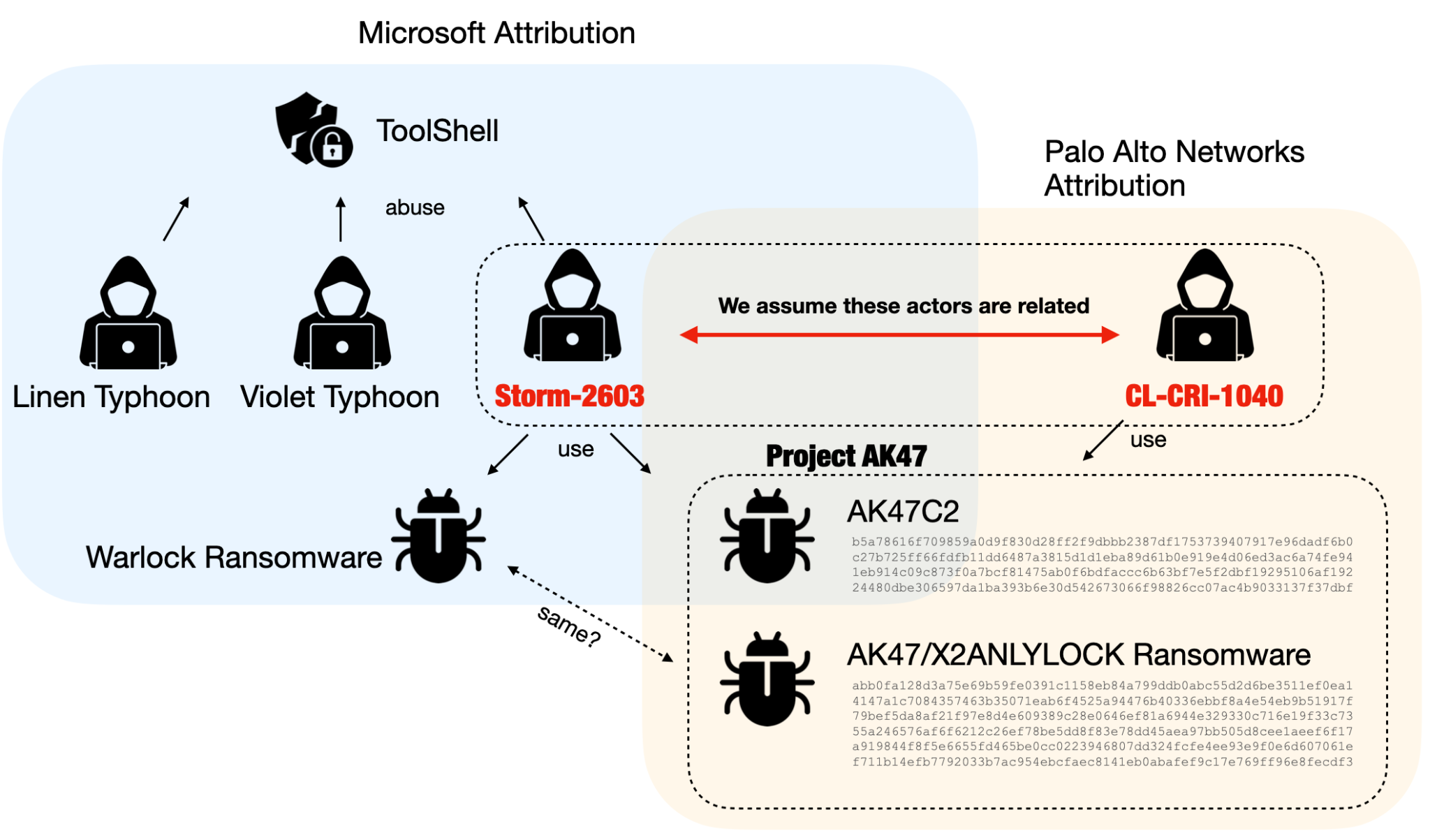
Unit 42 identified a financially motivated threat actor cluster named CL-CRI-1040, linked with Microsoft’s Storm-2603, targeting SharePoint vulnerabilities using the ToolShell exploit chain and deploying a malware suite called Project AK47. Project AK47 comprises a backdoor (AK47C2), ransomware (AK47/X2ANYLOCK), and loaders leveraging DLL side-loading, with ties to previous LockBit 3.0 affiliates and the Warlock Client double-extortion ransomware site. #CL-CRI-1040 #Storm-2603 #ProjectAK47 #ToolShell #AK47C2 #X2ANYLOCK #LockBit3 #WarlockClient
Keypoints
- CL-CRI-1040 is a financially motivated threat actor cluster exploiting recent SharePoint vulnerabilities (CVE-2025-49704, CVE-2025-49706, CVE-2025-53770, CVE-2025-53771) using the ToolShell exploit chain.
- CL-CRI-1040 employs a custom malware tool set named Project AK47, which includes a multi-protocol backdoor (AK47C2), ransomware (AK47/X2ANYLOCK), and DLL side-loading loaders.
- The AK47C2 backdoor supports DNS and HTTP communications for remote command execution and uses XOR encryption with evolving protocols.
- AK47 ransomware encrypts files with AES and RSA, terminates targeted applications, enumerates drives and shares, and drops ransom notes while checking timestamps to evade detection.
- CL-CRI-1040 was previously associated with a LockBit 3.0 affiliate and operates a double-extortion data leak site named Warlock Client Leaked Data Show.
- Evidence suggests the same threat actor cluster is tracked by Microsoft as Storm-2603, identified as a suspected China-based actor, though firm nation-state attribution remains inconclusive.
- Palo Alto Networks products provide layered protection against this threat, including machine learning, URL filtering, DNS security, and XDR solutions.
MITRE Techniques
- [T1071] Application Layer Protocol – AK47C2 backdoor uses DNS and HTTP protocols for command and control communications (“…communicate with the C2 server by XOR-encoding JSON data…”).
- [T1105] Ingress Tool Transfer – Deployment of loaders abusing DLL side-loading to load and execute malicious payloads (“…Loaders abusing DLL side-loading”).
- [T1059] Command and Scripting Interpreter – Backdoor supports executing arbitrary commands on compromised hosts (“…Executing an arbitrary command”).
- [T1486] Data Encrypted for Impact – AK47 ransomware encrypts files using AES and RSA algorithms to extort victims (“…Encrypting specific types of files using a combination of AES and RSA…”).
- [T1047] Windows Management Instrumentation – Use of legitimate tools such as PsExec by the threat actor (“PsExec.exe” and “PsExec64.exe” included in tools).
- [T1112] Modify Registry – Anti-analysis and anti-debugging techniques used in loaders (“…known anti-analysis and anti-debugging techniques…”).
Indicators of Compromise
- [SHA256 Hash] Malware components – AK47C2 dnsclient (ceec1a2d…), AK47C2 httpclient (24480dbe…), AK47 Ransomware (4147a1c7…), various loaders (1d85b180…, 7e9632ab…), LockBit 3.0 samples (dbf5ee8d…, 3b013d5a…).
- [Domain] C2 server – update.updatemicfosoft[.]com used by dnsclient version 202503 for DNS-based C2 communication.
- [File Name] Ransomware note files – “How to decrypt my data.txt” and “How to decrypt my data.log” dropped by AK47 ransomware.
- [Executable] Loader and utility files from Evidencia.rar – nxc.exe (PyPyKatz), SharpHostInfo.x64.exe, 7z.exe (legitimate executable used for DLL sideloading).
Read more: https://unit42.paloaltonetworks.com/ak47-activity-linked-to-sharepoint-vulnerabilities/