North Korean Lazarus subgroup Famous Chollima has developed PyLangGhost RAT, a Python-based remote access trojan targeting technology, finance, and cryptocurrency sectors through fake job interviews and social engineering. The malware steals browser-stored credentials and cryptocurrency wallet data by exploiting privilege escalation and sophisticated decryption methods. #PyLangGhostRAT #FamousChollima #LazarusGroup #GoLangGhostRAT
Keypoints
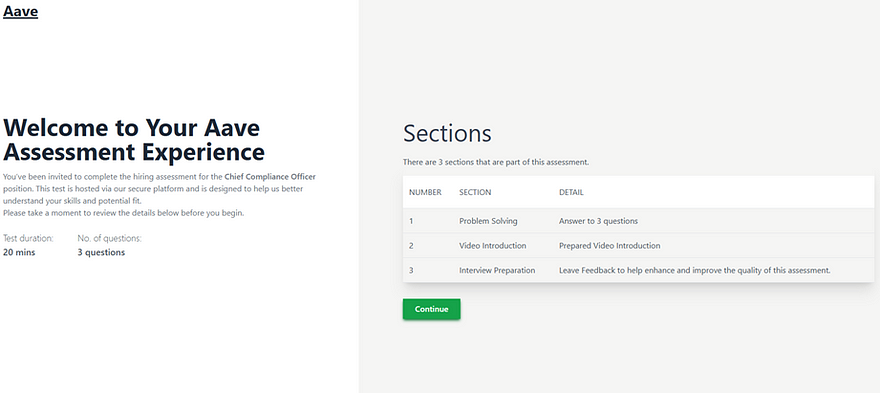
- PyLangGhost RAT is linked to the North Korean Lazarus subgroup Famous Chollima and is deployed via targeted social engineering campaigns called “ClickFix” during fake job interviews.
- The malware’s main loader (nvidia.py) uses modules for persistence, C2 communication, command execution, and credential theft, targeting Chrome extensions such as MetaMask, BitKeep, Coinbase Wallet, and Phantom.
- Delivery involves downloading and executing a malicious VBScript that installs a disguised Python environment and multiple Python modules for its operation.
- PyLangGhost RAT steals browser-stored credentials by bypassing Chrome encryption protections, including impersonating lsass.exe to gain SYSTEM privileges for decrypting newer encryption schemes.
- Communications with the command and control server use raw IP addresses and weak RC4/MD5 encryption without TLS, maintaining low detection rates on VirusTotal.
- The malware is a full Python reimplementation of GoLangGhost RAT, with evident AI-assisted code translation and obfuscation techniques like masquerading as legitimate binaries.
- PyLangGhost RAT poses financial, operational, reputational, and regulatory risks to organizations, emphasizing the need for behavioral detection, privilege restrictions, and employee awareness.
MITRE Techniques
- [T1036] Masquerading – Renames legitimate binaries such as python.exe to csshost.exe to evade detection (‘Renames legitimate binaries such as python.exe to csshost.exe.’)
- [T1059] Command and Scripting Interpreter – Uses wscript.exe to run update.vbs and csshost.exe to launch the nvidia.py loader (‘Initiates execution by using wscript.exe to run update.vbs and csshost.exe to launch the nvidia.py loader.’)
- [T1083] Files and Directory Discovery – Enumerates user profiles and browser extensions for credential theft (‘Enumerates user profiles and browser extensions.’)
- [T1012] Query Registry – Gains persistence via registry keys created by update.vbs (‘Gains persistence via registry entries created by the update.vbs script.’)
Indicators of Compromise
- [Domain] Command and control and payload download hosting domain – 360scanner.store
- [IPv4] C2 and malicious server IPs – 13.107.246.45, 151.243.101.229
- [URL] Malicious payload download URLs – https://360scanner.store/cam-v-b74si.fix, http://151.243.101.229:8080/
- [File hash] Python modules and loaders – bb794019f8a63966e4a16063dc785fafe8a5f7c7553bcd3da661c7054c6674c7 (auto.py.bin), c4fd45bb8c33a5b0fa5189306eb65fa3db53a53c1092078ec62f3fc19bc05dcb (command.py.bin), c7ecf8be40c1e9a9a8c3d148eb2ae2c0c64119ab46f51f603a00b812a7be3b45 (config.py.bin), a179caf1b7d293f7c14021b80deecd2b42bbd409e052da767e0d383f71625940 (nvidia.py.bin), ef04a839f60911a5df2408aebd6d9af432229d95b4814132ee589f178005c72f (util.py.bin)
- [Filename] Credentials and data exfiltration artifacts – chrome_logins_dump.txt, gather.tar.gz
- [Mutex] Instance control mutex file – .store
Read more: https://any.run/cybersecurity-blog/cybersecurity-blog/pylangghost-malware-analysis/