Netskope Threat Labs released BEAM, an open-source tool that detects supply chain attacks by analyzing network traffic without requiring endpoint agents. BEAM uses user agent strings and machine learning models to identify suspicious application behavior and anomalous communications. #BEAM #SolarWinds #NetskopeThreatLabs
Keypoints
- BEAM is an open-source tool that detects supply chain attacks by analyzing existing network traffic without needing endpoint agent deployment.
- The tool leverages user agent strings and a large language model to identify applications generating network traffic.
- BEAM uses over 180 features, including behavioral, temporal, and network indicators, to profile application traffic for anomalies.
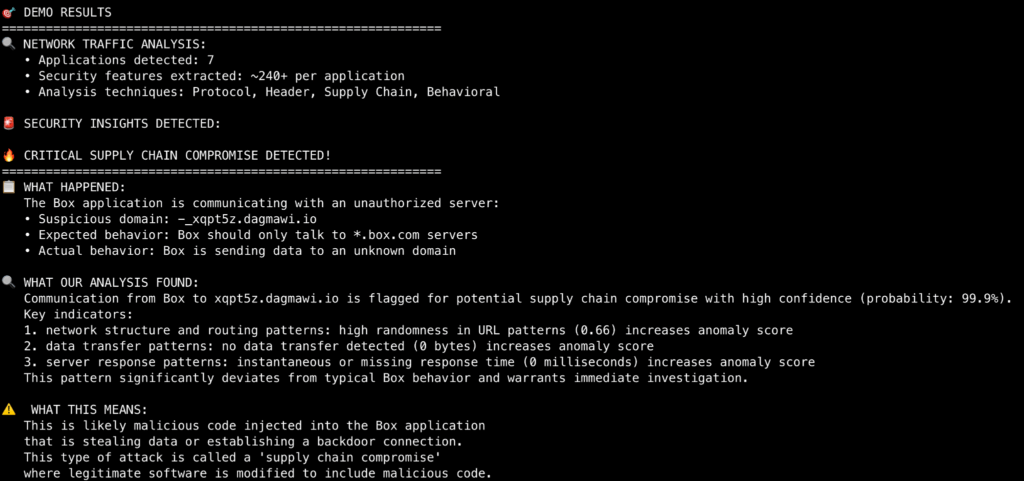
- A red team exercise demonstrated BEAM’s ability to detect compromised applications with a 94% probability using pre-trained models.
- Out-of-the-box models are available for popular applications like Asana, Box, Canva, Slack, and Spotify, among others.
- Users can create custom models for bespoke applications using unsupervised machine learning techniques if sufficient traffic is captured.
- The tool and sample data are available on GitHub for immediate use and community collaboration.
MITRE Techniques
- [T1071] Application Layer Protocol – BEAM analyzes HTTP and HTTPS network traffic to detect unusual application communication patterns (‘…analyze stored network traffic for indications of compromise…’).
- [T1566] Phishing – BEAM identifies communications to unusual external domains potentially related to command and control (C2) infrastructure (‘…the traffic in the HAR file showed communication from this Box application to an unusual endpoint…’).
- [T1083] File and Directory Discovery – BEAM parses PCAP and HAR files to extract metadata including user agent strings to identify application sources (‘…BEAM parses the traffic captures and extracts the user agent string…’).
- [T1041] Exfiltration Over C2 Channel – Detection of applications communicating with suspicious command and control URIs was demonstrated in red team exercises (‘…compromise to call out to a custom C2 URI without disclosing which application…’).
Indicators of Compromise
- [Domain] Suspicious external endpoints contacted by applications – xqpt5z.dagmawi.io (unusual endpoint contacted by compromised Box application).
- [File Type] Network traffic capture files used for analysis – HAR files (included sample file from Chrome and Box traffic), PCAP files (to be parsed by BEAM).
- [User Agent String] Application identifiers extracted from network traffic – unmodified user agent strings from corporate environments used to model application behavior.
Read more: https://www.netskope.com/blog/netskope-beam-open-source-detector-for-supply-chain-compromise