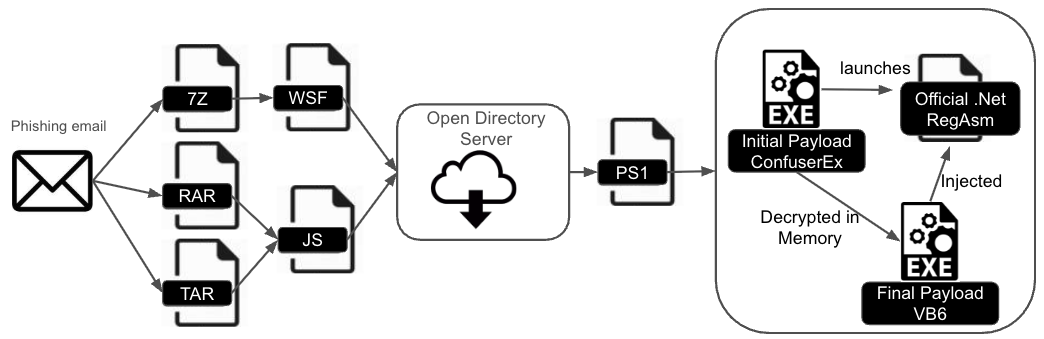
DarkCloud Stealer has evolved with new infection chains using ConfuserEx obfuscation and a Visual Basic 6 payload, complicating detection and analysis. The malware is distributed via phishing emails containing various archive types that deliver obfuscated scripts to deploy the payload. #DarkCloudStealer #ConfuserEx #RunPE
Keypoints
- DarkCloud Stealer’s distribution method shifted in April 2025, adding infection chains involving ConfuserEx obfuscation and VB6 payloads.
- Phishing emails deliver tarball, RAR, or 7Z archives containing obfuscated JavaScript or Windows Script Files that download PowerShell scripts.
- The PowerShell (PS1) scripts use multi-layer encryption and drop ConfuserEx-protected executables that deploy the final VB6 malware payload.
- ConfuserEx protections include anti-tampering, symbol renaming, control flow obfuscation, method reference hiding, and constant encoding.
- The final VB6 DarkCloud payload uses process hollowing via RegAsm.exe and encrypts critical strings with RC4 using unique keys.
- Indicators of compromise include specific archive and script file hashes, phishing URLs, and Telegram API credentials for command and control (C2).
- Palo Alto Networks products like Advanced WildFire, Cortex XDR, and Advanced URL Filtering provide mitigation against these threats.
MITRE Techniques
- [T1566] Phishing – Malware is delivered through phishing emails containing TAR, RAR, or 7Z archives with obfuscated scripts. (‘phishing email that contains either a tarball (TAR), Roshal (RAR) or a 7-Zip (7Z) archive’)
- [T1204] User Execution – The scripts require execution by the user to initiate the infection chain. (‘executing the script downloads and executes a PowerShell (PS1) file’)
- [T1059.001] PowerShell – PowerShell scripts are heavily obfuscated and used to download and execute payloads. (‘ActiveXObject objects to download and execute a PS1 file’)
- [T1027] Obfuscated Files or Information – ConfuserEx is used to protect the final payload with multiple obfuscation methods. (‘ConfuserEx comes with many features and protections such as anti-tampering, symbol renaming, control flow obfuscation’)
- [T1055] Process Injection – The final VB6 payload uses RunPE (process hollowing) to inject malicious code into RegAsm.exe. (‘process hollowing to inject the final VB6 payload’)
- [T1071.001] Application Layer Protocol – Telegram API is leveraged for C2 communications. (‘Telegram API credentials (used for C2 purposes)’)
Indicators of Compromise
- [File Hash] Archive and script hashes – RAR archive: bd8c0b0503741c17d75ce560a10eeeaa0cdd21dff323d9f1644c62b7b8eb43d9, JS file: 6b8a4c3d4a4a0a3aea50037744c5fec26a38d3fb6a596d006457f1c51bbc75c7
- [File Hash] Executables – Initial ConfuserEx .NET EXE: 24552408d849799b2cac983d499b1f32c88c10f88319339d0eec00fb01bb19b4, Final VB6 payload EXE: ce3a3e46ca65d779d687c7e58fb4a2eb784e5b1b4cebe33dbb2bf37cccb6f194
- [URL] Malware distribution server – hxxp[:]//176.65.142[.]190 hosting malicious scripts and PS1 files
- [URL] Command and Control – Telegram API URL: hxxps[:]//api.telegram[.]org/bot7684022823:AAFw0jHSu-b4qs6N7yC88nUOR8ovPrCdIrs/sendMessage?chat_id=6542615755
Read more: https://unit42.paloaltonetworks.com/new-darkcloud-stealer-infection-chain/