A novel AV killer malware leveraging the vulnerable ThrottleStop.sys driver has been active since at least October 2024, used to terminate antivirus processes and facilitate lateral movement in ransomware attacks such as MedusaLocker. Kaspersky’s products include mechanisms to defend against such threats, but this incident emphasizes the importance of defense in depth and strong access controls. #MedusaLocker #ThrottleStop.sys #BYOVD
Keypoints
- A new AV killer malware, using the vulnerable ThrottleStop.sys driver (renamed ThrottleBlood.sys), emerged in the wild since October 2024, targeting multiple antivirus products.
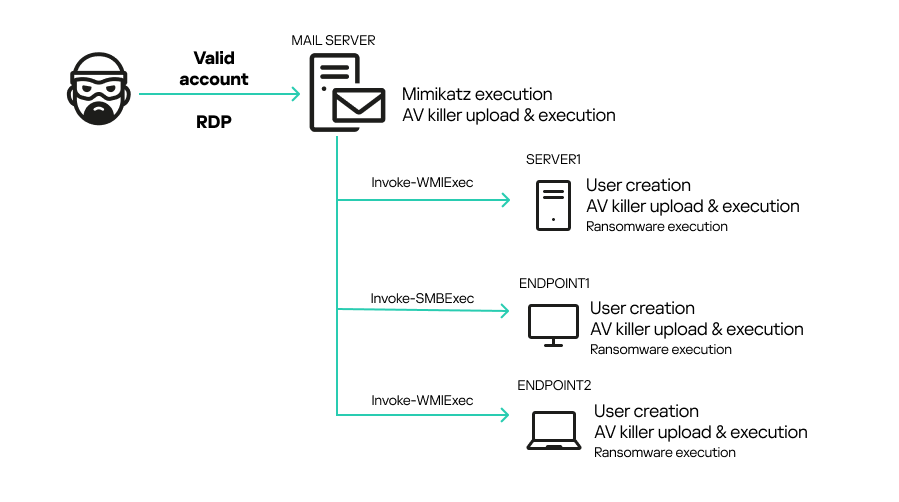
- The attack started by gaining initial access via valid RDP credentials, followed by credential theft with Mimikatz and lateral movement using pass-the-hash techniques.
- The AV killer disables antivirus protection by loading a vulnerable driver and injecting kernel-mode code to terminate AV processes like Windows Defender, Kaspersky, Avast, and others.
- The ThrottleStop.sys driver vulnerability (CVE-2025-7771) allows arbitrary physical memory read/write via IOCTL calls accessible by administrators.
- The malware targets antivirus processes by name and continuously kills and prevents their restart, facilitating successful ransomware deployment (MedusaLocker variant).
- Kaspersky products have built-in self-defense features that can mitigate this AV killer’s attempts to disable protections.
- Recommendations include enforcing strong password policies, restricting RDP access, network segmentation, multi-factor authentication, patch management, and use of EDR and IDS/IPS tools.
MITRE Techniques
- [T1057] Process Discovery – The malware enumerates running processes using Process32FirstW() and Process32NextW to identify AV processes. (‘The AV killer starts a loop to find target processes using the Process32FirstW() and Process32NextW API calls.’)
- [T1562.001] Impair Defenses: Disable or Modify Tools – The AV killer disables antivirus by terminating key AV processes via kernel memory manipulation. (‘The AV killer checks all running processes against the hardcoded list. If any match, it kills them by using the vulnerable driver to call the PsLookupProcessById and PsTerminateProcess kernel functions.’)
- [T1562.006] Impair Defenses: Indicator Blocking – The malware hijacks kernel routines via the vulnerable driver to evade detection and maintain persistence. (‘The malware writes shellcode that jumps to a target address within the kernel and restores the original kernel code to prevent system crashes.’)
- [T1543.003] Create or Modify System Process: Windows Service – The AV killer loads the vulnerable driver with SCM API functions such as OpenSCManagerA() and StartServiceW(). (‘When the binary is executed, it first loads the ThrottleBlood.sys driver using Service Control Manager (SCM) API methods.’)
- [T1489] Service Stop – The malware repeatedly terminates security services like MsMpEng.exe to prevent protection services from running. (‘Windows Defender will attempt to restart the service… the main loop will continue to identify and kill the associated AV process.’)
Indicators of Compromise
- [File Hash] Vulnerable driver ThrottleBlood.sys – 82ed942a52cdcf120a8919730e00ba37619661a3
- [File Hash] AV killer executable All.exe – c0979ec20b87084317d1bfa50405f7149c3b5c5f
- [File Hash] Ransomware sample haz8.exe – f02daf614109f39babdcb6f8841dd6981e929d70
- [File Hash] Other AV killer variants – e.g., eff7919d5de737d9a64f7528e86e3666051a49aa0a15be464a603b1eebc61744dc and multiple additional hashes
Read more: https://securelist.com/av-killer-exploiting-throttlestop-sys/117026/