The Model Context Protocol (MCP) standardizes LLM access to external tools and data, enabling powerful integrations but introducing supply-chain and runtime security risks such as tool poisoning, session hijacking, cross‑server manipulation, ANSI escape injection, and typosquatting. The post outlines MCP architecture, common transports and flows, real-world use cases, and recommended priorities for stronger authentication, governance, and monitoring. #ModelContextProtocol #ANSIescape
Keypoints
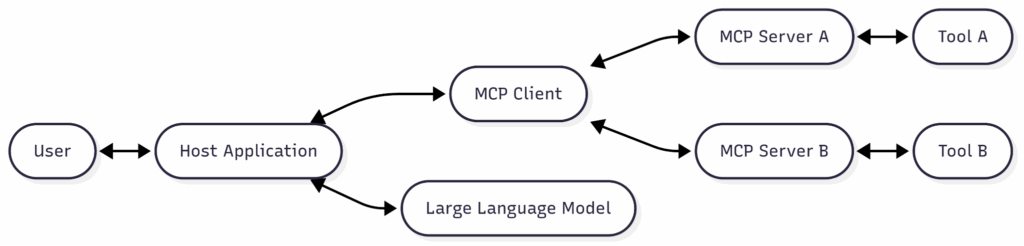
- MCP defines a JSON-RPC-based protocol for LLMs to discover and invoke external tools via MCP clients and servers, supporting transports like stdio and SSE.
- Initialization includes capability negotiation and tools/list enumeration; tools expose names, descriptions, and strict JSON input/output schemas used by LLMs.
- Authorization in MCP is optional (OAuth-style supported), so many servers may be accessible without enforced authentication, increasing risk of misuse and data leakage.
- Practical attack vectors include tool poisoning (hidden instructions), rug pulls (silent redefinition), cross-server shadowing, ANSI escape code injection, session hijacking, typosquatting, and supply-chain compromises.
- MCP registries and discovery services exist (e.g., smithery.ai, glama.ai, Docker Hub namespaces, Hugging Face Spaces, mcpindex.net) but generally lack strong identity verification, signatures, and scanning.
- Use cases span software development, data analysis, workflow automation, security operations, document retrieval, natural-language DB access, web app enhancement, and multi-agent coordination.
- Mitigations recommended include stronger governance, mandatory authentication/signatures, version pinning, tooling scanning, telemetry and monitoring, and cautious human-in-the-loop permission UX.
MITRE Techniques
- [T1553 ] Subvert Trust Controls – MCP registries and servers can be impersonated or typosquatted, allowing attackers to register malicious tools or servers that users trust (“…typosquatting, server impersonation, and supply-chain attacks.”)
- [T1609 ] Container Administration Command – Supply chain attacks compromise third-party packages or hosted MCP server implementations used by clients, leading to execution of malicious code (“…compromise the supply chain by injecting malicious code into dependencies or hosting malicious versions…”).
- [T1496 ] Resource Hijacking – Session hijacking in multi-server MCP setups allows stolen session IDs to be used to impersonate clients and perform unauthorized tool calls (“…stolen session IDs can be exploited to inject malicious prompts or impersonate legitimate clients.”).
- [T1204 ] User Execution – Tool poisoning with hidden instructions and ANSI escape code injection relies on the model (and sometimes users) executing or following concealed prompts within tool descriptions or outputs (“…embed hidden instructions within tool descriptions… ANSI terminal escape codes to hide malicious instructions … making them invisible on the screen while still being processed by the AI model.”).
- [T1604 ] Compromise Software Dependencies – Rug pulls and silent redefinition allow legitimate-seeming tools to change behavior or push malicious updates after initial approval (“…tools can alter their definitions without notifying users … leaking API keys or executing harmful actions.”).
Indicators of Compromise
- [Registry/Service ] public MCP registries and indices – examples: smithery.ai, mcpindex.net (demonstrates discovery surfaces that can be abused)
- [Endpoint/Transport ] vulnerable transports and services – example: Server-Sent Events (SSE) susceptible to DNS rebinding attacks; stdio for local integrations (context: transport types with known weaknesses)
- [Tool Names ] typosquatting candidates – example: file-summary-tool vs. file-summarizer (context: similarly named tools in registries enabling impersonation)
- [Technique/File Content ] ANSI escape sequences in tool descriptions or outputs – example: invisible terminal escape codes used to hide instructions (context: concealed payloads processed by LLMs)
- [Session Tokens ] stolen session IDs – context: session hijacking across multi-server MCP setups (example: hijacked session tokens used to craft events and impersonate clients)
Read more: https://www.netskope.com/blog/securing-llm-superpowers-navigating-the-wild-west-of-mcp