This article excerpts a Donut-generated shellcode malware analysis tutorial that walks through an end-to-end infection chain and demonstrates beginner-friendly static and dynamic analysis techniques. The excerpt focuses on a position-independent PC-relative addressing routine used in the shellcode and tools/methods used to analyze it. #Donut
Keypoints
- The tutorial analyzes a Donut-generated shellcode sample through a full infection chain from initial sample to final payload identification.
- It targets readers with basic malware-analysis knowledge and teaches use of tools like IDA Pro, x64dbg, dnSpy, and ProcessHacker.
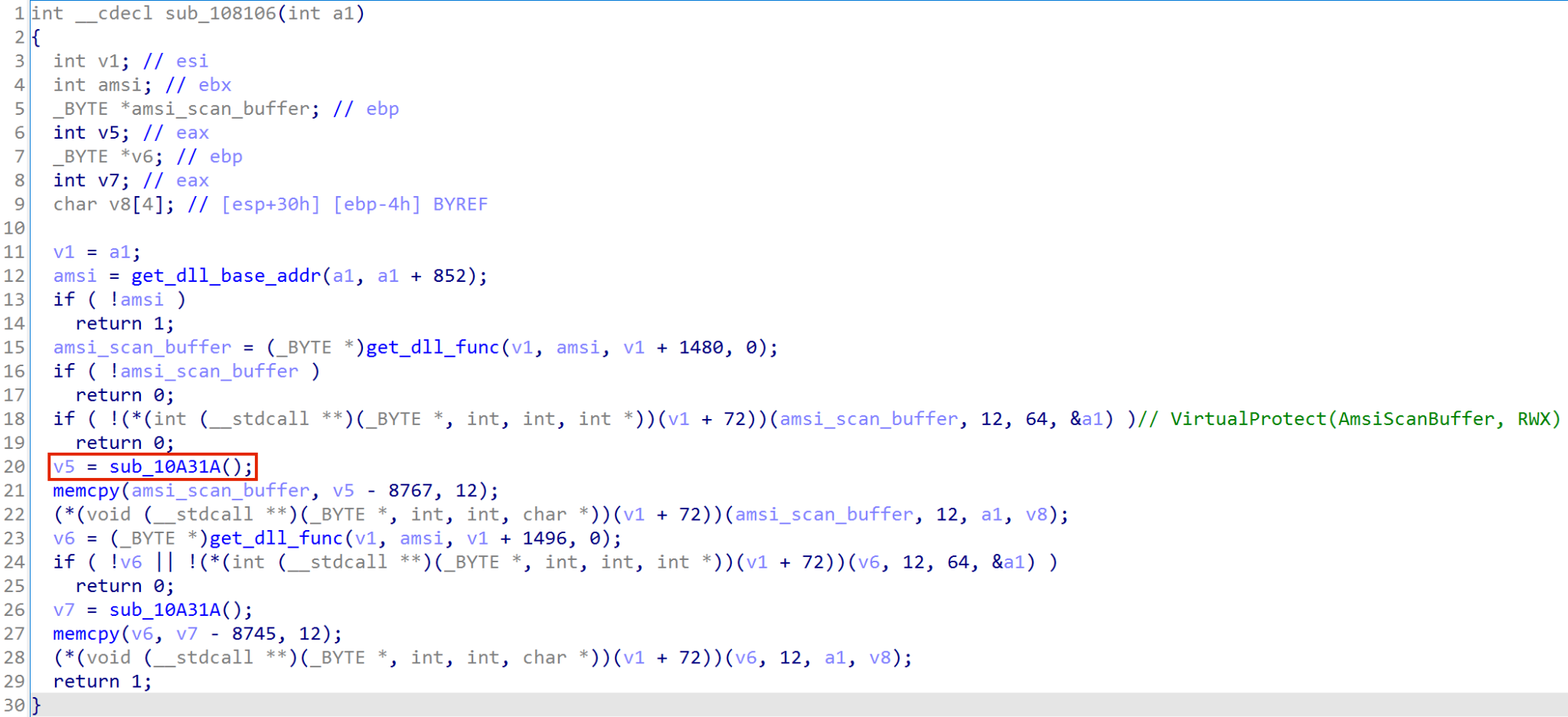
- The excerpt dissects an unknown function (sub_10A31A) that implements PC-relative addressing using a call/pop/sub sequence for position-independent code.
- Dynamic analysis in x64dbg confirms the function returns its own address (used as a base for resource offsets) and explains the mechanics of call $+5 and pop eax.
- The tutorial emphasizes combining static and dynamic techniques to understand malware behavior and reasoning behind observed actions.
- Palo Alto Networks products (WildFire, Advanced URL Filtering, DNS Security, Cortex XDR, XSIAM) provide protections informed by this research.
- Indicators of Compromise are provided, including a SHA256 hash for the decrypted Donut-generated shellcode sample.
MITRE Techniques
- [T1055 ] Process Injection – shellcode implements position-independent code and PC-relative addressing to locate and copy resources into memory for injected code execution (“…the shellcode can access the resources it needs by using an offset relative to the address of sub_10A31A…”).
- [T1106 ] Native API – dynamic API resolution referenced as a common technique (“Recognize common techniques used by malware in its natural context, such as: Dynamic API resolution”).
- [T1562.001 ] Impair Defenses: Disable or Modify Tools – bypassing AMSI by using memory patching (“Bypassing AMSI by using memory patching”).
- [T1059 ] Command and Scripting Interpreter – use of shellcode and in-memory execution implies non-file, in-memory payload execution techniques shown in the tutorial (“Decrypted Donut-generated shellcode”).
Indicators of Compromise
- [File Hash ] Decrypted Donut-generated shellcode sample – SHA256: d2bea59a4fc304fa0249321ccc0667f595f0cfac64fd0d7ac09b297465cda0c4
- [File Metadata ] File details – File size: 1,092,149 bytes; File type: Data; Description: Decrypted Donut-generated shellcode
Read more: https://unit42.paloaltonetworks.com/donut-malware-analysis-tutorial/