Two clusters of weaponized archives (XLS with obfuscated VBA) delivered between April and July 2025 targeted Ukraine and Poland, dropping first-stage DLL implants that collect system information and retrieve next-stage payloads from web-based C2 infrastructure. The activity shows tool, code, and infrastructure overlaps consistent with previously reported UAC-0057/UNC1151 (FrostyNeighbor/Ghostwriter) operations, using domains like sweetgeorgiayarns[.]online and taskandpurpose[.]icu for C2. #UAC-0057 #sweetgeorgiayarns[.]online
Keypoints
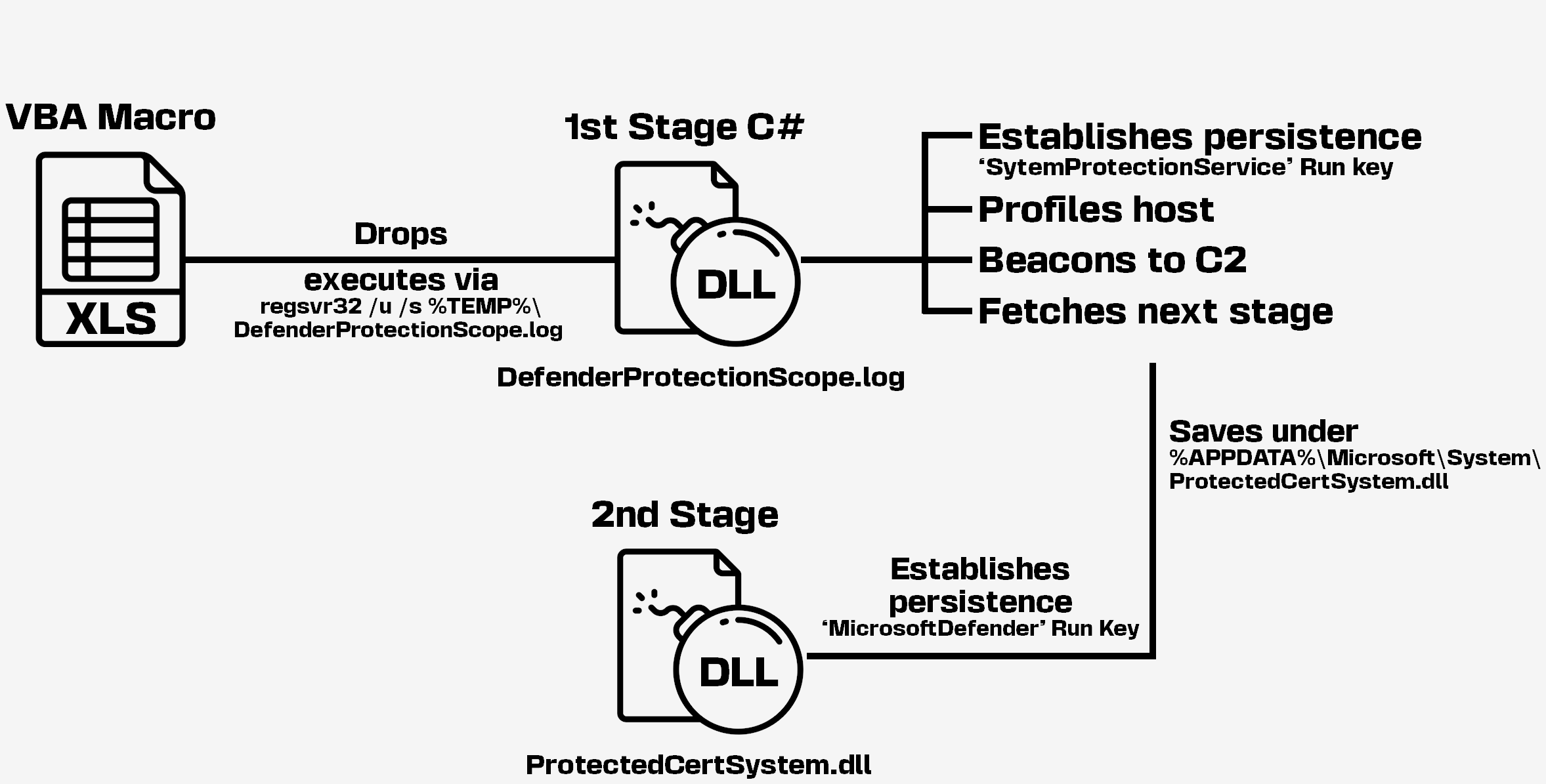
- Two related campaigns (targeting Ukraine and Poland) used compressed archives containing XLS spreadsheets with MacroPack-obfuscated VBA macros to drop and load DLL first-stage implants.
- First-stage implants included ConfuserEx-obfuscated C# downloaders and UPX-packed C++ DLLs that collected host info and polled web-hosted C2 URLs for next stages.
- Collected telemetry (OS, hostname, user, WMI queries, AV info, external IP via ip-info.ff.avast[.]com) was exfiltrated via HTTP POSTs or Slack webhooks to C2 domains such as sweetgeorgiayarns[.]online, taskandpurpose[.]icu, and punandjokes[.]icu.
- Persistence mechanisms included HKCU Run entries and scheduled tasks (e.g., UpdateSDX and RuntimeBroker), with repeated use of LNK files and regsvr32/rundll32 execution patterns.
- Infrastructure showed consistent registration patterns (PublicDomainRegistry, Proton/ProtonMail registrant emails, Cloudflare DNS/proxy) and domain impersonation of legitimate sites to host C2 image URLs.
- Some Poland-targeting variants used Slack as a C2 channel (webhooks and files), and one variant loaded a Cobalt Strike Beacon from medpagetoday[.]icu.
- Attribution low-to-medium confidence to UAC-0057/UNC1151 (FrostyNeighbor/Ghostwriter) based on tooling, techniques, infrastructure, targeting, and code reuse, with minor evolutions like Slack C2 and TLD changes.
MITRE Techniques
- [T1204] User Execution – Malicious XLS spreadsheets with VBA macros were used to trick users into enabling macros and execute the payloads. Quote: ‘XLS spreadsheets with a VBA macro that drops and loads a DLL.’
- [T1064] Scripting – VBA macros wrote files (DLL/CAB) and invoked system utilities (regsvr32, expand.exe, rundll32) to execute payloads. Quote: ‘the VBA macro writes a DLL to %TEMP%… and uses the Shell.ShellExecute method to load it with regsvr32 /u /s %TEMP%…’
- [T1218] Signed Binary Proxy Execution – Use of legitimate Windows binaries (regsvr32.exe, rundll32.exe, expand.exe, shell32.dll ShellExec_RunDLL) to load and execute dropped DLLs. Quote: ‘uses regsvr32 /u /s “%LOCALAPPDATA%Servx00bac729fe.log”‘
- [T1547] Boot or Logon Autostart Execution – Persistence via registry Run keys and scheduled tasks to re-launch implants. Quote: ‘adds two entries to the current user’s “Run” registry key’ and ‘registering a scheduled task named UpdateSDX which runs … at user logon.’
- [T1059] Command and Scripting Interpreter – Use of cmd.exe /c to run downloaded payloads and WScript.Shell via COM to execute next stages. Quote: ‘runs it using the provided command (spawned via cmd.exe /c)’ and ‘run the next stage using a WScript.Shell object instantiated via the COM API.’
- [T1071] Application Layer Protocol – Implants communicate with web-hosted C2 using HTTP(S) POST/GET and cookies to exfiltrate info and retrieve payloads. Quote: ‘sent as form data to hxxps://punandjokes[.]icu/cannabis-jokes.jpg’ and ‘sent as a cookie (mod0api) value to … sweetgeorgiayarns[.]online…’
- [T1105] Ingress Tool Transfer – Downloaders retrieve next-stage payloads from C2 URLs (JPEG endpoints) and write them to disk for execution. Quote: ‘tries to download a next stage from the C2 server… the next stage is written to %APPDATA%…ProtectedCertSystem.dll’
- [T1497] Virtualization/Sandbox Evasion – Use of checks (response size threshold) to decide whether to accept/download next stage content, limiting sandbox exposure. Quote: ‘involving a check on the response size to make sure that the data is larger than 220000 bytes’
Indicators of Compromise
- [Hash ] example dropped DLLs and archives – a2a2f0281eed6ec758130d2f2b2b5d4f578ac90605f7e16a07428316c9f6424e (C# DLL, Ukraine July 2025), 5fa19aa32776b6ab45a99a851746fbe189f7a668daf82f3965225c1a2f8b9d36 (SDXHelp.dll, Poland May 2025)
- [Domain ] C2 infrastructure – sweetgeorgiayarns[.]online (C2 URL used for Ukraine July 2025), taskandpurpose[.]icu (C2 for Poland May 2025)
- [URL ] C2 endpoints embedding images – hxxps://sweetgeorgiayarns[.]online/wp-content/uploads/2025/04/06102226/Kims-hand-cards.jpg (C2 URL), hxxps://taskandpurpose[.]icu/hews/coast-guard-0reg0n-c0ncrete.jpg (C2 URL)
- [File path ] persistence and drop locations – %LOCALAPPDATA%SDXHelpSDXHelp.dll (C++ downloader, Poland May 2025), %APPDATA%MicrosoftWindowsProtection overview.lnk (LNK used to load DLLs)
- [Slack webhook ] Slack-based C2 – hxxps://hooks.slack[.]com/services/T08NWSF1L78/… (Slack webhook used in April 2025 campaign), and 1 more webhook URL
Read more: https://harfanglab.io/insidethelab/uac-0057-pressure-ukraine-poland/