Attackers have been exploiting CVE-2024-36401 in GeoServer to achieve remote code execution and deploy legitimate SDKs or apps that silently monetize victims’ internet bandwidth as residential proxies. The campaign uses multiple distribution hosts and pivots infrastructure to evade detection while delivering payloads (examples: 37.187.74[.]75, 64.226.112[.]52) and abusing SDKs/apps designated e193, z593, a593. #CVE-2024-36401 #GeoServer
Keypoints
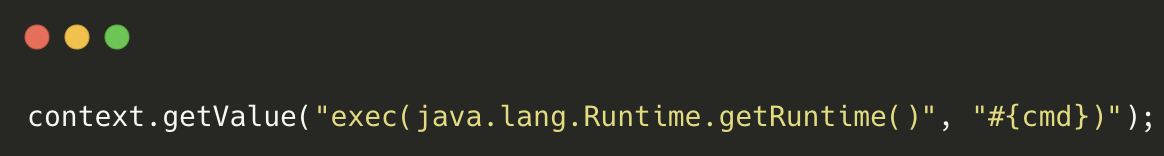
- Attackers exploited CVE-2024-36401 (GeoServer) to inject JXPath expressions that invoke Java Runtime.exec(), enabling remote code execution.
- The campaign delivers legitimate-looking SDKs and apps (misused SDK variants: a593, c593, d593, s593, z593; app variants: a193, d193, e193) to monetize victim bandwidth quietly.
- Initial exploitation observed in early March 2025 with exploit source IPs including 108.251.152[.]209 and distribution hosts 37.187.74[.]75 and later 185.246.84[.]189 and 64.226.112[.]52.
- Attackers used transfer.sh-like private file-sharing instances on port 8080 to distribute payloads and staged loaders (z593 → z401, z402 → main executable) to maintain stealth and persistence.
- Cortex Xpanse telemetry showed thousands of publicly exposed GeoServer instances (3,706 in early May; 7,126 across March–April 2025), indicating a large attack surface.
- Malicious payloads are cross-compiled with Dart for Linux to broaden targets and potentially evade detection; the SDK used appears identical to the vendor’s legitimate SDK.
- Palo Alto Networks protections (Threat Prevention signature 95463, Advanced WildFire, URL Filtering, DNS Security, Cortex XDR/XSIAM) and patching are recommended to mitigate this campaign.
MITRE Techniques
- [T1203] Exploitation for Client Execution – The adversary exploited CVE-2024-36401 in GeoServer to inject JXPath expressions that trigger Java runtime execution (“…invoke methods like getRuntime().exec()…”).
- [T1059] Command and Scripting Interpreter – The exploit forces execution of system commands to download and run payloads (payload “forces the victim to execute a system command to download a file from the attacker’s host distribution IP addresses”).
- [T1105] Ingress Tool Transfer – Attackers hosted payloads on attacker-controlled file-sharing instances (transfer.sh on 64.226.112[.]52:8080 and 37.187.74[.]75:8080) to transfer second-stage payloads like z593.
- [T1547] Boot or Logon Autostart Execution – Stager scripts create hidden directories and place main executables for persistent/covert execution (z401 “creating a hidden directory and placing the main executable within it”).
- [T1222] File and Directory Discovery – The malicious loaders inspect and monitor device resources to decide when to share bandwidth, enabling stealthy operation (“monitoring device resources and illicitly sharing the victim’s bandwidth whenever possible”).
Indicators of Compromise
- [IP Address ] campaign distribution and exploit sources – 37.187.74[.]75:8080, 64.226.112[.]52:8080 (also observed: 185.246.84[.]189, 108.251.152[.]209)
- [File Hash ] staged and payload binaries – example hashes: 89f5e7d66098ae736c39eb36123adcf55851268973e6614c67e3589e73451b24, 4e4a467abe1478240cd34a1deaef019172b7834ad57d46f89a7c6c357f066fdb (and many more hashes)
- [URLs ] malicious download endpoints – hxxp://37.187.74[.]75:8080/w1wOYGVLEX/a101, hxxp://64.226.112[.]52:8080/MFTYFuqKGU/a401 (multiple other paths listed on both hosts)
- [File Names ] staged scripts and components – z593 (second-stage), z401 (creates hidden directory), z402 (launches main executable); app/SDK filenames: a193, d193, e193, a593, c593, d593, s593, z593
Read more: https://unit42.paloaltonetworks.com/attackers-sell-your-bandwidth-using-sdks/