Bqtlock is a newly observed Ransomware-as-a-Service (RaaS) strain linked to the actor “ZerodayX” that uses anti-analysis techniques, process hollowing, privilege escalation, scheduled-task persistence, and double-extortion tactics while demanding Monero payments. The operator markets builder/subscription services with customizable options and has released an updated variant adding UAC bypasses, credential theft from browsers, stronger obfuscation, and expanded exfiltration via Discord webhooks. #Bqtlock #ZerodayX
Keypoints
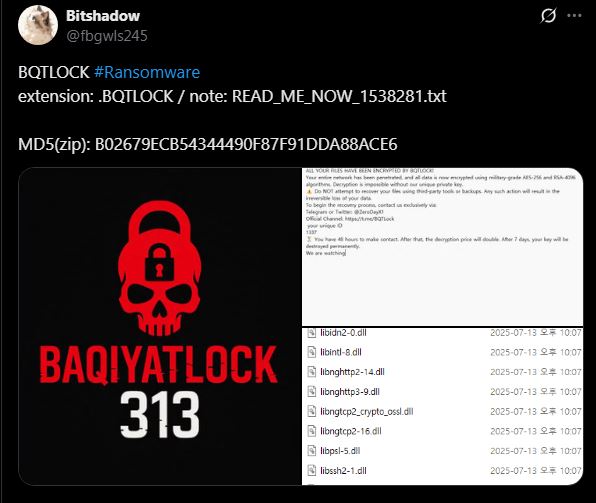
- Bqtlock is a RaaS active since mid‑July, associated with the operator ZerodayX and promoted via Telegram/X, offering starter/professional/enterprise subscription tiers with many customization options.
- The ransomware is distributed in ZIP archives (containing executables and DLLs) and encrypts files with AES-256 + RSA-4096, appending a .bqtlock extension and dropping ransom notes demanding 13–40 XMR with doubling and life‑time deletion threats.
- It employs multiple anti-analysis techniques (string obfuscation, debugger checks, anti-VM stubs), mutex checks, privilege escalation (SeDebugPrivilege and UAC bypasses), process hollowing (targeting explorer.exe), and scheduled-task persistence named MicrosoftWindowsMaintenanceSystemHealthCheck.
- Bqtlock performs reconnaissance (host/user/local & public IP via icanhazip.com), creates a local admin account (BQTLockAdmin / Password123!), terminates protection processes, disables recovery features, and modifies wallpaper/icons to intimidate victims.
- Data exfiltration is implemented using Discord webhooks (JSON payloads), screenshots, logs, and the updated variant adds credential stealing from multiple browsers and attempts lateral movement by copying bqtpayload.exe to %TEMP%.
- The updated August 5, 2025 variant adds new anti-debug checks (CheckRemoteDebuggerPresent, OutputDebugString, timing checks), multiple UAC bypass methods (cmstp, fodhelper, eventvwr registry abuse), heavier obfuscation, self-deletion, and event log clearing.
- IOC artifacts include file hashes, onion site and Telegram channels, a Monero wallet, and an email contact; promotional activity and a ransomware builder (BQTLock Ransomware Builder V4) indicate active commercialization of the malware.
MITRE Techniques
- [T1055 ] Process Injection / Process Hollowing – Bqtlock performs process hollowing targeting explorer.exe via a function named Perform_hollowing (“…perform hollowing targeting explorer.exe…”).
- [T1134 ] Create or Modify System Process (Create Account) – Creates a new local user “BQTLockAdmin” and adds it to Administrators using NetUserAdd and NetLocalGroupAddMembers (“…creating a new local user ”BQTLockAdmin” with the password “Password123!” … adding it to the Administrators group”).
- [T1490 ] Inhibit System Recovery – Executes commands to disable Windows recovery mechanisms to prevent file recovery (“…execute a series of system commands designed to disable Windows recovery mechanisms”).
- [T1071 ] Application Layer Protocol (Webhook Exfiltration) – Exfiltrates collected system data via a Discord webhook sending JSON payloads (“…exfiltrates collected system data through a Discord webhook, transmitting information in JSON format”).
- [T1486 ] Data Encrypted for Impact – Encrypts files using AES-256 and encrypts keys with RSA-4096, appending .bqtlock and dropping ransom notes demanding Monero payments (“…hybrid encryption approach of using AES-256 with RSA-4096 … appending a custom extension (.bqtlock) … ransom note”).
- [T1053 ] Scheduled Task/Job – Achieves persistence by registering a scheduled task via schtasks.exe named MicrosoftWindowsMaintenanceSystemHealthCheck (“…constructs a command to register a scheduled task … MicrosoftWindowsMaintenanceSystemHealthCheck”).
- [T1136 ] Create Account – Creates a local admin account for persistence and lateral capabilities (“…creating a new local user ”BQTLockAdmin” … and elevating its privileges”).
- [T1140 ] Deobfuscate/Decode Files or Information – Embeds many payload elements (ransom note, extension, wallpaper, RSA key, webhook URL) in Base64 and decodes them at runtime (“…embeds all key elements … in Base64 format”).
- [T1112 ] Modify Registry – Modifies DefaultIcon registry keys for file type icons and UAC bypass registries under HKCUSoftwareClassesms-settingsShellOpencommand for fodhelper/eventvwr UAC bypasses (“…updates their DefaultIcon registry keys …” and “…modify registry keys under HKCUSoftwareClassesms-settingsShellOpencommand”).
- [T1056 ] Input Capture (Credential Theft) – New variant harvests stored browser credentials from Chromium-based browsers and Firefox (logins.json + key4.db) (“…harvests credentials … ‘Login Data’ and ‘logins.json’ and retrieves the corresponding decryption key from ‘key4.db’”).
- [T1547 ] Boot or Logon Autostart Execution (Scheduled Task) – Uses scheduled tasks for persistence (“…register a scheduled task using schtasks.exe … for persistence”).
- [T1497 ] Virtualization/Sandbox Evasion (Anti-analysis) – Uses IsDebuggerPresent, CheckRemoteDebuggerPresent, OutputDebugString, GetTickCount, string obfuscation, and anti-VM stubs to evade analysis (“…string obfuscation, debugger detection, and virtual machine evasion…” and “IsDebuggerPresent(), CheckRemoteDebuggerPresent(), OutputDebugString(), and GetTickCount()”).
- [T1068 ] Exploitation for Privilege Escalation (UAC Bypass) – Uses multiple UAC bypass techniques such as CMSTP .inf auto-elevation and registry auto-elevation via fodhelper/eventvwr (“…using CMSTP … abuse CMSTP’s auto-elevation…” and “…fodhelper.exe & eventvwr.exe … modify registry keys … to execute payload with elevated privileges”).
- [T1110 ] Brute Force (Account Creation for Persistence/Lateral Movement) – Creates a default account with known password for persistence and potential lateral movement (“…local user ‘BQTLockAdmin’ with the password ‘Password123!’”).
Indicators of Compromise
- [File Hash ] Sample ransomware hashes – 4E7434AC13001FE55474573AA5E9379D, 7170292337A894CE9A58F5B2176DFEFC (ransomware samples referenced).
- [Domain / Onion ] RaaS and data-leak sites – hxxp[:]//yywhylvqeqynzik6ibocb53o2nat7lmzn5ynjpar3stndzcgmy6dkgid[.]onion, hxxps[:]//x[.]com/Zerodayx1 (promotional/listing sites).
- [Telegram / Social ] Operator and promotion channels – hxxps[:]//t[.]me/BQTlock, hxxps[:]//t[.]me/Fuch0u, hxxps://t[.]me/BQTnet, hxxps://t[.]me/BQTlock_raas (channels used to advertise and distribute).
- [Wallet ] Monero payment address – 89RQN2EUmiX6vL7nTv3viqUAgbDpN4ab329zPCEgbceQJuS233uye4eXtYk3MXAtVoKNMmzgVrxXphLZbJPtearY7QVuApr (payment destination for ransom demands).
- [Email ] Contact for victims – [email protected] (ransom negotiation contact listed in note).
- [File Names ] Payload and artifacts – Update.exe (encryptor in ZIP), bqtpayload.exe (self-copy for execution), bqt_screenshot.png, bqt_wallpaper.bmp, bqt_icon.ico (dropped artifacts and payload names).
Read more: https://labs.k7computing.com/index.php/examining-the-tactics-of-bqtlock-ransomware-its-variants/