DNS tunneling is increasingly used for stealthy data exfiltration and command-and-control by embedding encoded data in DNS queries and responses, exploiting permissive DNS traffic and flexible record types like TXT. Notable tools—iodine, dnspot, and dnscat2—demonstrate tunneling, chat, and C2 over DNS; mitigation includes restricting resolvers, anomaly detection, and deep DNS inspection. #iodine #dnspot #dnscat2
Keypoints
- DNS is frequently allowed through firewalls and can be abused for covert communication, making it a preferred channel for data exfiltration and C2.
- Flexible DNS record types (notably TXT, A, AAAA, CNAME, MX) enable attackers to embed encoded payloads and instruction fragments within queries and responses.
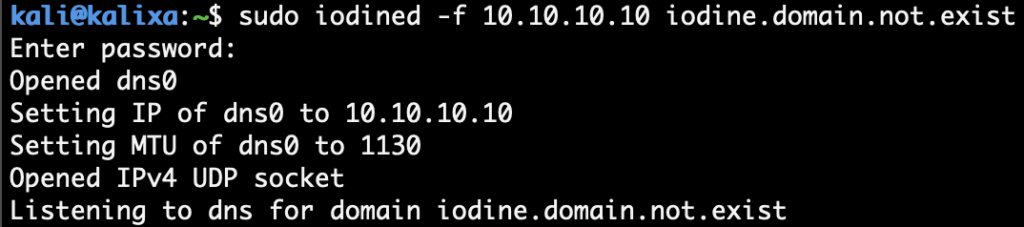
- Iodine provides IP-level tunneling over DNS, creating a virtual interface (dns0) and enabling access to remote resources via DNS queries.
- dnspot supports chat and C2 over DNS using long hostnames and key-based server/client interactions to exchange messages covertly.
- dnscat2 enables interactive, encrypted (but not inherently verified) C2 sessions over DNS, allowing remote command execution and file/system enumeration.
- Network indicators of DNS tunneling include unusually long or high-entropy hostnames, periodic/query-type patterns (e.g., frequent TXT requests), and recurring hexadecimal payload fragments.
- Mitigations include restricting DNS to approved resolvers, applying anomaly detection for DNS query patterns, and routing DNS through inspection proxies/filters to block NRDs/NODs and suspicious domains.
MITRE Techniques
- [T1071.004] Application Layer Protocol: DNS – Used as a covert channel for data exfiltration and C2 by tunneling data within DNS queries/responses: ‘tunnel data and command-and-control (C2) directives within seemingly valid DNS queries and replies.’
- [T1095] Non-Application Layer Protocol: DNS Tunneling (mapped to tunneling techniques) – Tools like iodine create virtual interfaces and tunnel IPv4 over DNS to transmit data: ‘Iodine is a tool that enables the tunneling of IPv4 data through a DNS server.’
- [T1572] Protocol Tunneling (or alternate technique for covert channel) – dnscat2 and dnspot establish encrypted or chat sessions over DNS to provide C2 and covert messaging: ‘dnscat2 is a powerful tool that enables command-and-control (C2) communication over the seemingly innocuous DNS traffic.’
- [T1070.004] File Deletion (visibility technique related) – Attackers can use interactive shells over dnscat2 to run system commands and view or manipulate files remotely, as shown by executed ‘whoami’ and ‘dir’ commands in the dnscat2 session: ‘whoamicmd.exe… whoami winvic99administrator’
Indicators of Compromise
- [Domain / FQDN] Nonexistent or attacker-controlled domains used for tunneling – example: domain.not.exist (used by iodine, dnspot, dnscat2).
- [DNS Record Types / Query Patterns] Suspicious record usage and patterns – frequent TXT queries, excessively long hostnames, high-entropy subdomains (examples: repeated TXT queries and extremely long hostnames observed in packet traces).
- [Public Keys / Identifiers] Server/client key material shown in tool output – example: dnspot server public key eskfpbyb6jfnwz06o701ki53btpwaviya68ar41l85b98e1zjb and private key 1cw3o8b7ga8wlmbhe4ws7pxx3lbqpv9bo8zaeugtdl7zumq40c (context: dnspot server/client setup).
- [Session Strings / Handshake Text] Verification strings shown in dnscat2 sessions – examples: ‘Poxes Story Peace Harp Lordy Flacks’ and ‘Shirks Abate Winful Sonny Wages Ripe’ used to validate encrypted sessions.
Read more: https://www.netskope.com/blog/dns-tunneling-the-blind-spot-in-your-network-security-strategy