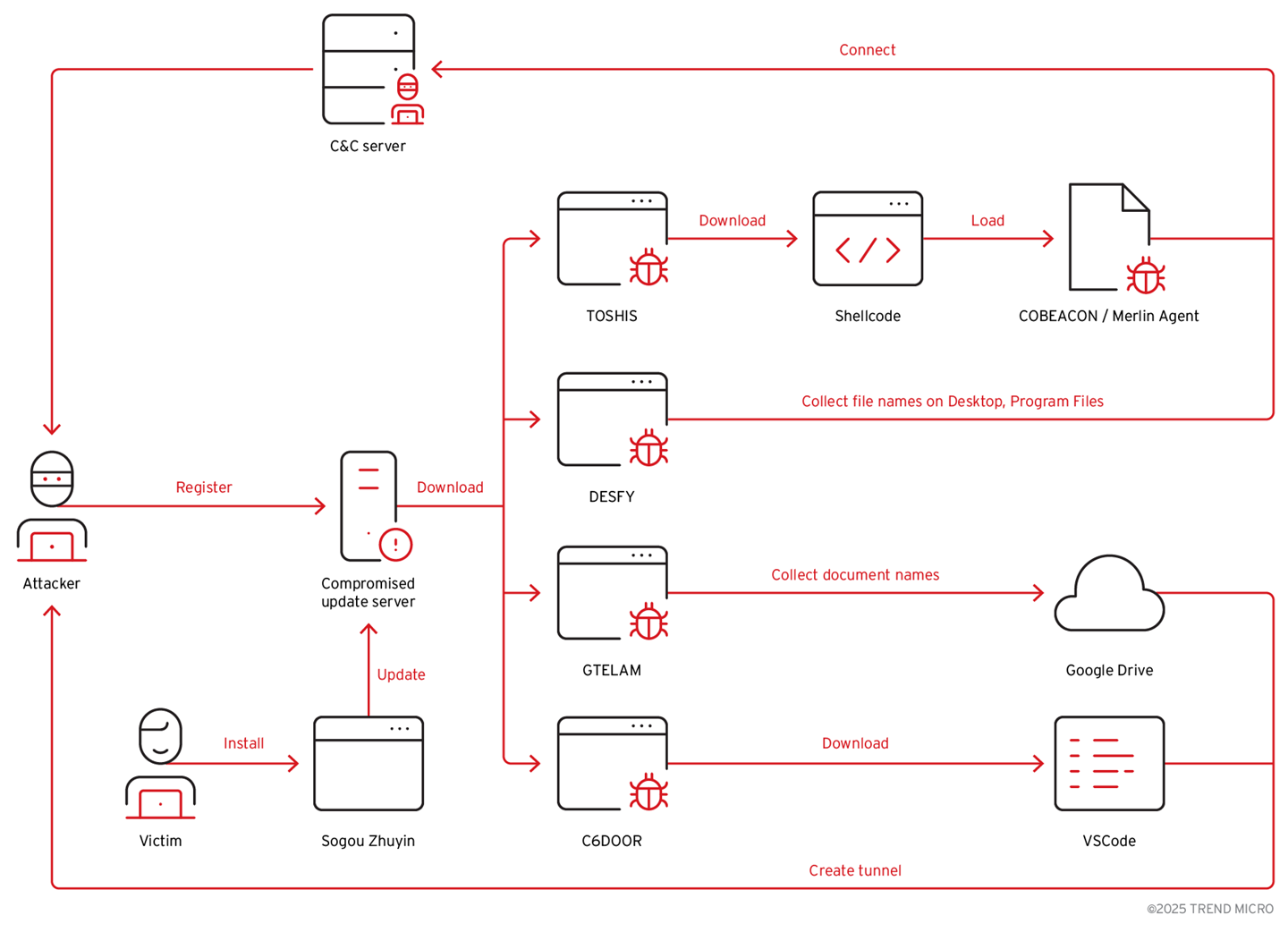
The TAOTH campaign abused an abandoned Sogou Zhuyin update server and targeted victims across Eastern Asia using spear-phishing and hijacked software updates to deliver multiple malware families, including TOSHIS, C6DOOR, DESFY, and GTELAM. Attackers focused on reconnaissance of high-value targets (dissidents, journalists, researchers, business/tech leaders) and reused shared C2 infrastructure and tooling linked to prior activity. #TOSHIS #C6DOOR #GTELAM #DESFY
Keypoints
- Attackers hijacked the abandoned Sogou Zhuyin update domain (sogouzhuyin[.]com) in Oct 2024 to distribute malicious updates beginning Nov 2024.
- Multiple malware families were deployed via the update channel and phishing: TOSHIS (loader/Xiangoop variant), DESFY (file-name collector), GTELAM (document enumerator uploading names to Google Drive), and C6DOOR (Go backdoor).
- Spear-phishing campaigns used fake cloud storage pages and fake OAuth login flows to either deliver TOSHIS or obtain OAuth consent to access victims’ mailboxes for lateral abuse.
- Victims were primarily high-value individuals in Eastern Asia (Taiwan, China, Hong Kong, Japan, South Korea) including dissidents, journalists, researchers, and tech/business leaders; some victims in US and Norway were also observed.
- TOSHIS loads follow-up payloads (Cobalt Strike or Merlin) after patching PE entry points and using a consistent decryption key; it targets specific language IDs (zh-TW, zh-CN, ja-JP).
- C6DOOR implements extensive remote commands (file ops, screenshots, shell execution, SSH/SFTP, scanning) and includes embedded Simplified Chinese hints at actor language.
- Infrastructure and tooling overlap (shared C2 IP 45.32.117.177, Xiangoop/TOSHIS lineage, Cobalt Strike watermark 520, VSCode tunnels) link TAOTH to previously documented activity and indicate a persistent reconnaissance/espionage actor.
MITRE Techniques
- [T1098] Account Manipulation – Obtained OAuth consent to attacker-controlled apps to access and manipulate victim mailboxes (“…OAuth URLs prompting users to grant consent to the attacker-controlled application…request scopes for email manipulation, such as gmail.modify and mail.read+mail.send”).
- [T1195] Supply Chain Compromise – Hijacked an end-of-support software update server (Sogou Zhuyin) to distribute malicious updates (“…attacker took over the abandoned update server and…used the domain to host malicious updates since October 2024.”).
- [T1204] User Execution – Lured victims to run captured executables (fake PDF reader PDFreader.exe / McOds.exe) that trigger DLL sideloading (“…victim clicks on a counterfeit PDF reader executable named PDFreader.exe…McVsoCfg.dll will be launched via DLL sideloading.”).
- [T1059] Command and Scripting Interpreter – Executed system and network discovery commands during post-exploitation (e.g., tasklist.exe, quser.exe, ipconfig.exe) (“…The commands used in the post-exploitation stages: C:WindowsSystem32tasklist.exe /svc … C:WindowsSystem32ipconfig.exe /all”).
- [T1105] Ingress Tool Transfer – Downloaded secondary payloads and decoy documents via the loader (TOSHIS/TOSHIS stager retrieves additional payloads from C2) (“TOSHIS acts as a stager by retrieving additional payloads from its command-and-control (C&C) server.”).
- [T1027] Obfuscated Files or Information – Used obfuscated intermediary web pages (obfuscator.io) as web beacons for phishing and tracking (“…The obfuscated intermediary page works as a web beacon…The page is obfuscated by a public service obfuscator.io.”).
- [T1036] Masquerading – Used fake cloud storage and login pages mimicking legitimate services to trick users into downloading malicious archives or granting OAuth consent (“…fraudulent page is designed to mimic a legitimate cloud storage service…victims are automatically prompted to download an archive file named material.zip.”).
- [T1005] Data from Local System – Collected filenames and documents from Desktop and Program Files for profiling (DESFY and GTELAM collection behaviors) (“DESFY gathers filenames from Desktop and Program Files…GTELAM collects document names with extensions .pdf .doc .docx … and sends them to Google Drive.”).
- [T1041] Exfiltration Over C2 Channel – Exfiltrated collected filenames/documents to attacker C2 or cloud storage (GTELAM uploads AES-encrypted filenames to Google Drive) (“…All collected filenames are encrypted in AES and sent to Google Drive.”).
Indicators of Compromise
- [Domain] malicious or impersonated infrastructure – dl.sogouzhuyin[.]com (malicious update distribution), srv-pc.sogouzhuyin[.]com (embedded update URL)
- [IP Address] shared C2 infrastructure – 45.32.117.177 (overlap with prior cases), 64.176.50.181 (observed in hunting queries)
- [Filenames/Binaries] modified or abused executables – ZhuyinUp.exe (legitimate updater retrieving malicious config), PDFreader.exe / McOds.exe (fake PDF reader used to launch McVsoCfg.dll)
- [OAuth URLs/Redirects] attacker-controlled OAuth endpoints – accounts.google.com…redirect_uri=https%3A%2F%2Fwww.auth-web.com%2Fgm-oauth2-callback, login.microsoftonline.com…redirect_uri=https%3A%2F%2Fauth.onedrive365-jp.com%2Fgetauthtoken
- [Hash/Key material] cryptographic keys used by tools – C6DOOR AES key: fee8211f723b5bfeb74cc45b0eac7fcd275397ea8f538cf5ea138f12586e5b26 and IV: 6679580b03a7e9284f26c5936c8655fa; TOSHIS payload key: “qazxswedcvfrtgbn”
Read more: https://www.trendmicro.com/en_us/research/25/h/taoth-campaign.html