XLab discovered a novel Linux backdoor—MystRodX—delivered by a dropper dst86.bin from IP 139.84.156.79, featuring multi-layer XOR/AES encryption, passive activation via crafted DNS/ICMP triggers, and flexible C2 communication modes. Active C2s tied to campaigns “neybquno” and “zoufkcfr” (e.g., 149.28.137.254:8010) remain online, and multiple sample hashes and indicators are provided to aid hunting. #MystRodX #dst86.bin
Keypoints
- XLab’s CTIA detected dst86.bin from 139.84.156.79; initial AV labels called it Mirai but analysis revealed a new dropper/backdoor named MystRodX.
- MystRodX implements multi-layer encryption: single-byte XOR for VM/debug strings, a custom Transform algorithm for AES keys/payloads/triggers, and AES-CBC for configuration.
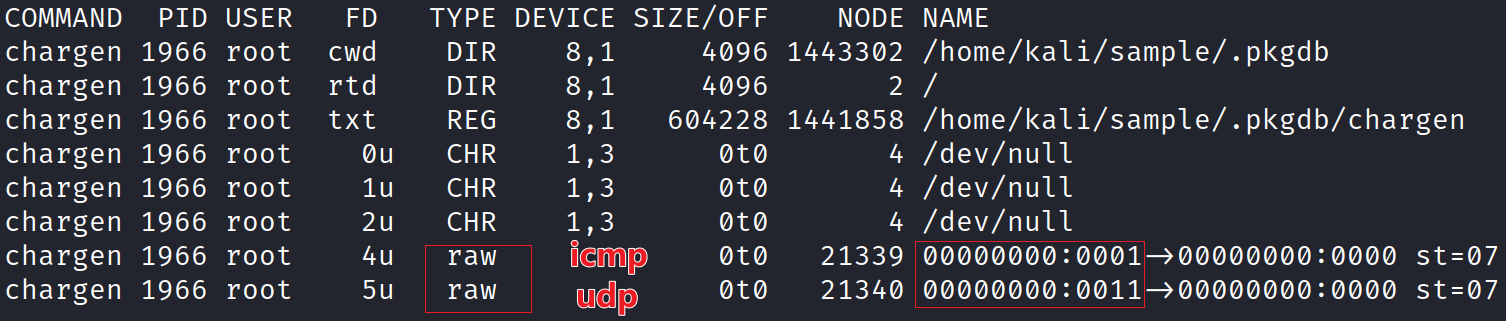
- The backdoor supports passive wake-up mode using RAW sockets to monitor traffic and activate via specially crafted DNS or ICMP payloads without open ports.
- Configurations include activation timestamp, C2 hosts/ports, and RSA public keys linking C2s to campaigns (e.g., neybquno, zoufkcfr); three active C2s were found (including 149.28.137.254, 156.244.6.68, 185.22.153.228).
- MystRodX features a dual-process guardian (Launcher/daytime + chargen backdoor), dynamic enabling of features (TCP/HTTP, AES/plaintext), and standard backdoor functions (reverse shell, file mgmt, SOCKS, port forwarding).
- Attackers use command 7 to enable traffic encryption; decryptable MagicString links some C2s to known campaigns while others indicate unknown campaigns and uncaptured samples.
- IOCs provided: dropper URL, C2 domains/IPs, sample MD5s, public keys, and the Transform algorithm to assist defenders in detection and decryption.
MITRE Techniques
- [T1071] Application Layer Protocol – MystRodX can use TCP or HTTP for C2 communication and can switch between plaintext or AES-encrypted traffic (“it can be configured to enable or disable AES encryption” and “supports two communication modes: TCP and HTTP”).
- [T1573] Encrypted Channel – MystRodX supports optional traffic encryption and uses AES-CBC for configuration and a custom Transform algorithm for AES keys/payloads (“Configuration is encrypted using AES in CBC mode” and “AES keys, Payloads, and Trigger packets are encrypted using a custom ‘transform algorithm’”).
- [T1036] Masquerading (Payload Deception/Launcher) – The dropper releases files named chargen, busybox, and daytime with a Launcher that manages the backdoor, using typical Unix-like utility names to blend in (“The decrypted Payload contains three critical files: chargen, busybox, and daytime… daytime is the Launcher”).
- [T1218] System Binary Proxy Execution – MystRodX’s Launcher and dual-process guardian mechanism continuously monitor and restart the backdoor process to ensure persistence (“the Launcher will restart the backdoor process… dual-process guardian mechanism”).
- [T1059] Command and Scripting Interpreter (Reverse Shell) – The backdoor implements reverse shell functionality among its capabilities (“supports features like file management, port forwarding, reverse shell, and socket management”).
- [T1078] Valid Accounts (Use of Public Keys for Campaigns) – MystRodX configurations include RSA public keys tied to campaigns and used for decrypting command 7 payloads to enable encryption, linking C2s to campaigns (“MystRodX configurations include RSA public keys… two known keys linked to the ‘neybquno’ and ‘zoufkcfr’ campaigns”).
- [T1572] Protocol Tunneling (ICMP/DNS Triggers) – MystRodX passively listens on RAW sockets and hides activation payloads in DNS query domains or ICMP payloads to trigger the backdoor without open ports (“it hides activation instructions directly in the payload of ICMP packets or within DNS query domains” and “uses a RAW socket to monitor all incoming traffic—without binding to any open port”).
- [T1497] Virtualization/Sandbox Evasion – MystRodX uses single-byte XOR-encrypted strings to detect VMs and debuggers by checking BIOS vendor files and parent process names (“VM-related: Checks the contents of /sys/class/dmi/id/bios_vendor… Debugger-related: Checks the parent process name for common debugging tools”).
Indicators of Compromise
- [Downloader URL] dropper distribution – http://139.84.156[.]79/dst-x86.bin
- [C2 IPs/Domains] active C2 infrastructure – 149.28.137[.]254:8010 (neybquno), 149.28.137[.]254:8443 (zoufkcfr), airtel.vpndns.net:443 (neybquno), 149.28.130[.]195:443 (zoufkcfr), 156.244.6[.]68:443 (unknown), 185.22.153[.]228:443 (unknown)
- [Sample MD5 – dropper/implants] example hashes – 5e3a2a0461c7888d0361dd75617051c6 (dst dropper), 72d377fa8ccf23998dd7c22c9647fc2a (chargen backdoor), 5bf67ce1b245934965557de6d37f286f (daytime launcher); and 3 more hashes.
- [Patched Samples] XLab-patched hashes – 4dc20d1177da7932be3d63efe939b320, 2775d9eac1c4a5eb2c45453d63ea6379 (used for testing and lowering AV detection).
- [Public Keys] campaign RSA public keys – ‘neybquno’ and ‘zoufkcfr’ public keys (PEM blocks provided in report) used to decrypt command 7 payloads.
Read more: https://blog.xlab.qianxin.com/mystrodx_covert_dual-mode_backdoor_en