North Korea-aligned actors behind the Contagious Interview cluster used cyber threat intelligence platforms (Validin, VirusTotal, Maltrail) and coordinated team workflows (likely Slack) to monitor, scout, and rapidly replace exposed infrastructure while conducting ClickFix social engineering against job seekers in the crypto sector. SentinelLABS recovered ContagiousDrop server logs showing over 230 victims and numerous IOCs including domains, IPs, email addresses, and SHA-1 hashes. #ContagiousInterview #ClickFix
Keypoints
- The Contagious Interview actors actively monitor CTI platforms (Validin, VirusTotal, Maltrail) to detect exposure and scout new infrastructure.
- They operate in coordinated teams with real-time collaboration indicators (likely Slack) and shared workflows across multiple accounts.
- Rather than making broad OPSEC changes, they make limited, sporadic modifications and prioritize rapidly deploying new infrastructure after takedowns.
- ClickFix social engineering lures job seekers to run commands (e.g., curl) that download ContagiousDrop malware tailored by OS and architecture.
- ContagiousDrop applications log victim data and notify operators via email, enabling detailed victimology; SentinelLABS found logs for over 230 victims (Jan–Mar 2025).
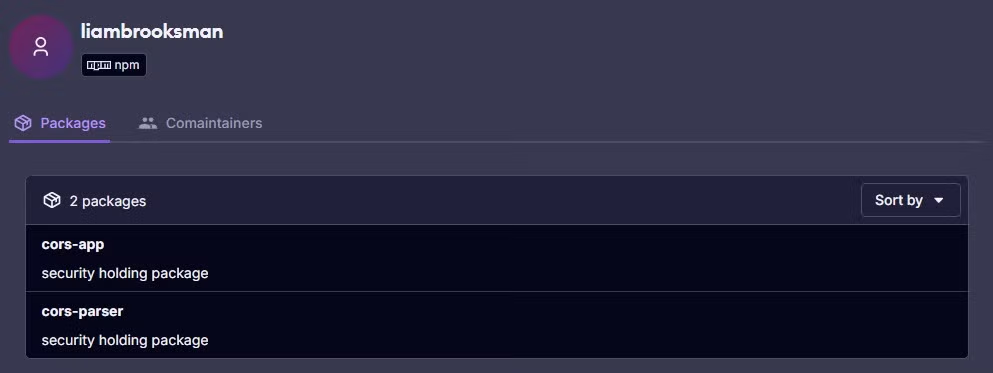
- Actors used fake personas, fabricated companies, and reused email addresses to register lure domains and Validin accounts, sometimes revealing operator linkages.
- Repeated OPSEC failures (exposed web roots, logs, timestamps) allowed researchers to reconstruct timelines and operational practices.
MITRE Techniques
- [T1583 ] Acquire Infrastructure – Actors scouted and purchased domains and hosting, using Validin to evaluate assets before acquisition (“to scout and evaluate new infrastructure prior to purchase… likely to determine whether it had been previously reported as malicious”).
- [T1598 ] Phishing for Credentials – ClickFix social engineering lures job seekers into executing commands to download malware (“A targeted job seeker receives an invitation… prompted to complete a skill assessment… instructed to copy and paste command lines… unknowingly deploying malware”).
- [T1105 ] Ingress Tool Transfer – Delivery of malware via commands like curl from ClickFix distribution servers to victim systems (“they are then instructed to copy and paste command lines, often involving utilities like curl, to download and execute a supposed update”).
- [T1027 ] Obfuscated Files or Information – Use of tailored payloads and disguised updates to avoid detection (“deliver malware disguised as software updates or essential utilities… tailored payload based on the victim’s operating system”).
- [T1071 ] Application Layer Protocol – Use of web servers and HTTP GET/POST to deliver payloads and log interactions (“These applications run servers that listen on configured ports to handle incoming HTTP GET and POST requests”).
- [T1608 ] Stage Capabilities – Rapid deployment and replacement of infrastructure in response to takedowns to sustain operations (“rapidly deployed new infrastructure in response to service provider takedowns”).
- [T1082 ] System Information Discovery – ContagiousDrop gathered victim OS and architecture to select appropriate payloads (“distribute a tailored payload based on the victim’s operating system (Windows, macOS, or Linux), system architecture”).
- [T1114 ] Email Collection – Applications send email notifications to operators containing victim engagement details (“integrated email notification system… provide the Contagious Interview threat actors with insights into victim engagement”).
Indicators of Compromise
- [Email Addresses ] Operator accounts and notification addresses – designedcuratedamy58[@]gmail.com, brooksliam534[@]gmail.com, and many others (full list includes ~40 addresses such as excellentreporter321[@]gmail.com, fairdev610[@]gmail.com).
- [IP Addresses ] Used for Validin registration/logins – 181.215.9[.]29 (account registration and logins), 194.33.45[.]162 (Astrill VPN-associated registration), and other IPs like 70.39.70[.]194, 38.170.181[.]10.
- [Domains ] Lure and infrastructure domains – paxos-video-interview[.]com, skillquestions[.]com, webcamfixer[.]online, and other Contagious Interview domains like talentcheck[.]pro and VidHireHub[.]com.
- [Malware Distribution Servers ] ClickFix/ContagiousDrop endpoints – api.drive-release[.]cloud, api.release-drivers[.]online, api.camdriverhelp[.]club, glitchmedic[.]com.
- [Hashes ] ContagiousDrop application files (app.js) – SHA-1 24042a8eea9b9c20af1f7bae00296b44968a068f, 44ddabf5b5d601077936a130a2863a96d2af1c8e, and 4a8bfa28d46ae14e45a50e105e2d34f850ffa96c.