Wiz investigated a Soco404 campaign that hid cryptominer payloads in fake 404 HTML pages hosted on Google Sites, exploiting cloud misconfigurations and vulnerabilities; Google removed the sites after reporting. WhoisXML API and other data sources linked nine initial IoC domains to extensive DNS, WHOIS, and IP artifacts, uncovering thousands of related domains, client IPs, and historical records. #Soco404 #moneroocean.stream
Keypoints
- Wiz discovered Soco404 cryptomining payloads embedded in fake 404 pages on Google Sites; Google took down the sites after reporting.
- Nine domains were identified as initial IoCs; WhoisXML API analysis expanded artifacts and contextual data around those domains.
- 1,516 unique client IPs made 18,052 DNS requests to four IoCs between 15–23 July 2025, spanning five ASNs (IASC data).
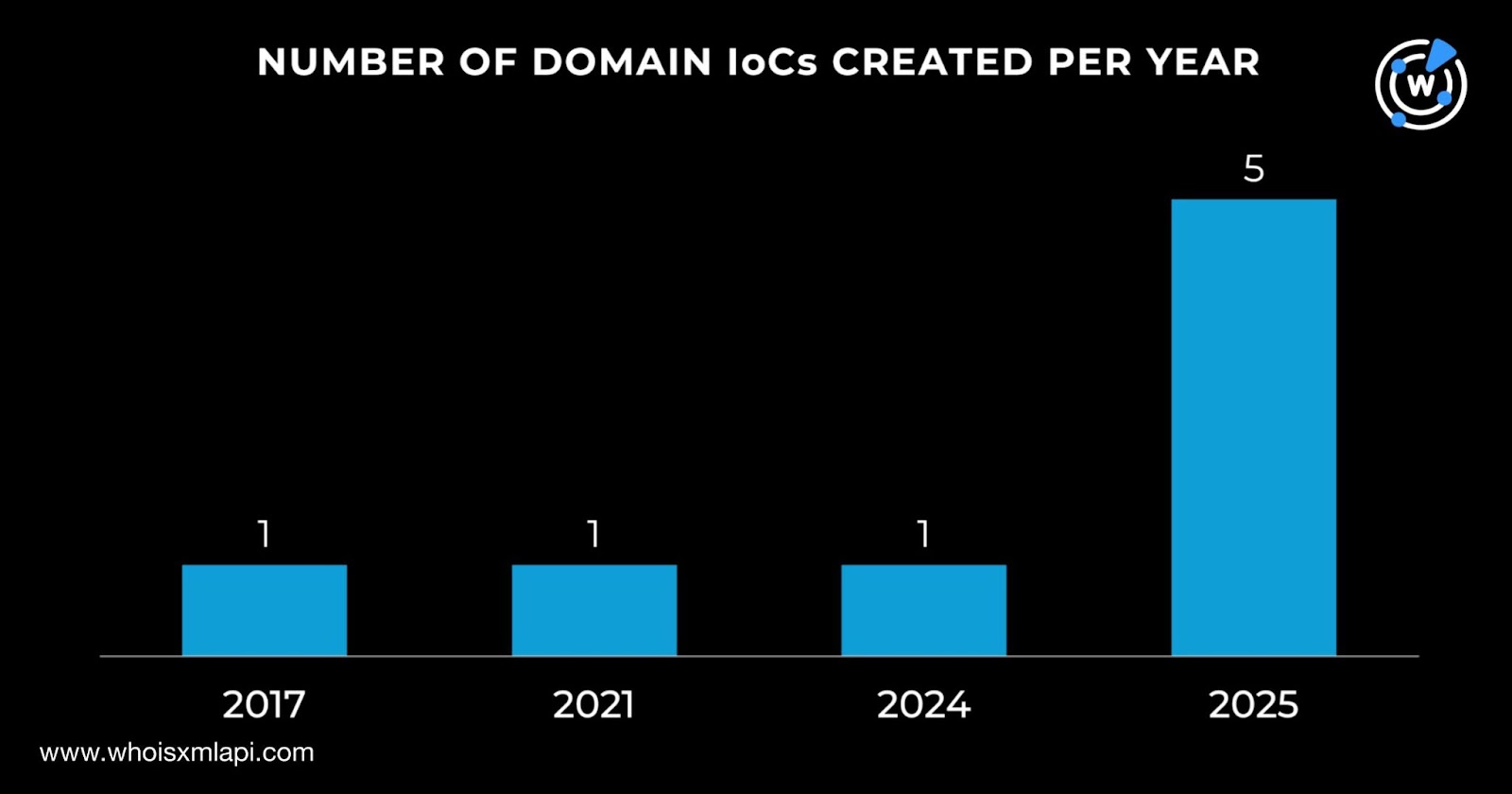
- Domain registration analysis showed eight domains with WHOIS records; most were created in 2025, with one dating to 2017 (moneroocean[.]stream).
- DNS history revealed many domain-to-IP resolutions (e.g., moneroocean[.]stream: 486 resolutions; arcticoins[.]com: 165 resolutions), suggesting re-registration and re-use.
- First Watch flagged dblikes[.]cyou and seeyoume[.]top as likely-to-turn-malicious 165 and 65 days before Wiz’s reporting.
- Expansions found 9,459 email-connected domains (one linked to malware: kapatoken[.]com), 17 IPs (15 malicious), one IP-connected domain, and 45 string-connected domains.
MITRE Techniques
- [T1190] Exploit Public-Facing Application – Soco404 leveraged vulnerabilities and misconfigurations in cloud environments and Google Sites to host malicious fake 404 pages and deliver payloads. Quote: ‘…payloads were embedded in fake 404 HTML pages hosted on websites built using Google Sites.’
- [T1059] Command and Scripting Interpreter – Cryptomining payloads imply the use of scripts/binaries to run mining processes on compromised hosts after delivery via fake pages. Quote: ‘…deploy cryptominers.’
- [T1071] Application Layer Protocol – DNS was abused for communications and resolution insights; 18,052 DNS requests from 1,516 unique client IPs indicate reliance on DNS-related activity. Quote: ‘…1,516 unique client IPs communicated with four IoCs via 18,052 DNS requests.’
- [T1583] Acquire Infrastructure – Threat actors registered multiple domains (many in 2025) and re-registered older names (e.g., arcticoins[.]com) to host malicious content. Quote: ‘…the newest—fastsoco[.]top—was created on 21 June 2025’ and ‘…arcticoins[.]com recorded 165 IP resolutions…not consistent with the domain’s current WHOIS record creation date.’
- [T1086] PowerShell – Common for cryptominer deployment and post-exploitation activity; inferred from mining deployment methodology and script-based delivery from web-hosted payloads. Quote: ‘…deploy cryptominers.’
Indicators of Compromise
- [Domain ] initial IoCs and related domains – moneroocean[.]stream, fastsoco[.]top, and 6 other domains (nine total identified as IoCs).
- [Domain ] flagged likely-to-turn-malicious – dblikes[.]cyou, seeyoume[.]top (flagged 165 and 65 days before Wiz reporting).
- [Domain ] email-connected domain linked to malware – kapatoken[.]com (found among 9,459 email-connected domains).
- [IP Address ] client IPs contacting IoCs – 1,516 unique client IPs observed contacting four IoCs via DNS (example aggregate; 17 IPs identified in DNS resolutions with 15 assessed malicious).
- [DNS Resolution ] domain-to-IP history – moneroocean[.]stream (486 resolutions), arcticoins[.]com (165 resolutions), fastsoco[.]top (176 resolutions).
- [Registrar/Country ] registrant context – domains registered via Namecheap, NameSilo, Reg.ru, Dynadot, OnlineNIC; registrant countries include US, Iceland, Russia.
Read more: https://circleid.com/posts/spilling-the-beans-on-multiplatform-cryptominer-soco404