Huntress discovered a previously unseen ransomware variant named Obscura that was deployed via a ransomware executable placed in the domain NETLOGON (C:WINDOWSsysvolsysvol[domain].localscripts), automatically replicating across controllers and executed by scheduled tasks to encrypt hosts. The Go-based binary requires administrative privileges, terminates security and backup processes, deletes volume shadow copies, and uses XChaCha20/Curve25519 encryption with a recoverable footer; #Obscura #Cephalus
Keypoints
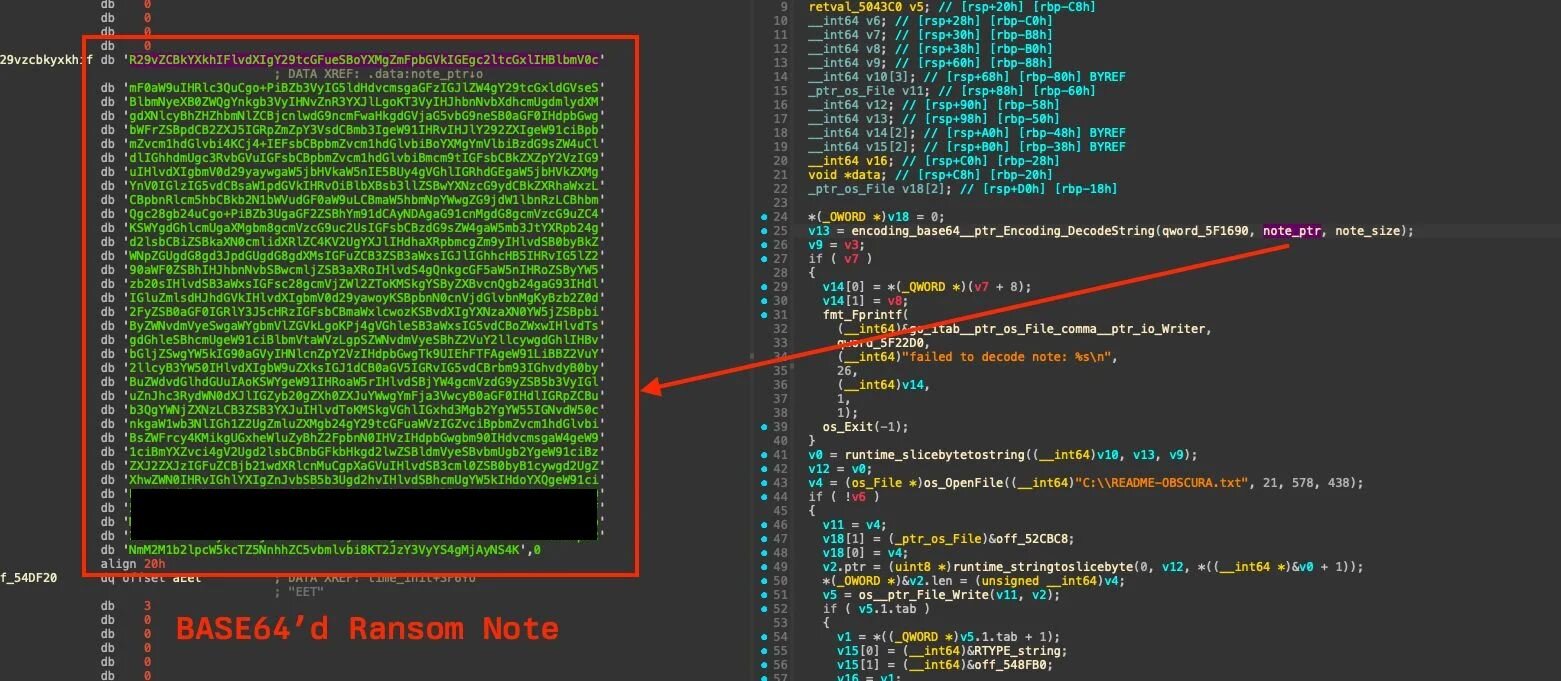
- Obscura is a Go-built ransomware discovered 29 August 2025 with its ransom note embedded as a base64 string and written to C:README-OBSCURA.txt.
- The executable was placed in the NETLOGON/SYSVOL scripts folder on a domain controller, causing automatic replication across domain controllers and likely network-wide deployment.
- Scheduled tasks (e.g., SystemUpdate and iJHcEkAG) were created to execute the binary and to enable RDP via netsh, facilitating access and execution.
- The binary requires administrative privileges (AllocateAndInitializeSid + CheckTokenMembership); if not elevated it exits, and when elevated it deletes volume shadow copies (vssadmin delete shadows /all /quiet) and terminates many security/backup/database processes.
- Encryption uses Curve25519 (X25519) to derive a shared secret, XChaCha20 for file encryption, and appends a 64-byte footer (OBSCURA! + 32-byte public key + 24-byte nonce) enabling key derivation by the attacker.
- Obscura implements file extension exclusion to preserve system functionality (15 extensions excluded, e.g., .exe, .dll, .sys, .efi, .iso, .lnk, .swapfile, .obscura).
- Huntress observed limited agent deployment which reduced detection and prevented determining initial access; Obscura joins other emerging variants such as Crux and Cephalus.
MITRE Techniques
- [T1070 ] Indicator Removal on Host – The ransomware runs “cmd.exe /c vssadmin delete shadows /all /quiet” to delete volume shadow copies and remove recovery points (“cmd.exe /c vssadmin delete shadows /all /quiet”).
- [T1486 ] Data Encrypted for Impact – The malware encrypts files using XChaCha20 with keys derived from Curve25519 ephemeral key exchange and appends a footer containing “OBSCURA!” and the public key/nonce to each encrypted file (“OBSCURA!” … “32 byte public key” … “24 byte nonce”).
- [T1053 ] Scheduled Task/Job – Threat actor creates scheduled tasks (named SystemUpdate and iJHcEkAG) to execute the ransomware and run commands to enable RDP (“scheduled task named SystemUpdate … execute the ransomware binary”; “iJHcEkAG” runs netsh to enable Remote Desktop Protocol access).
- [T1036 ] Masquerading – The ransomware executable was named for the domain and placed in the NETLOGON scripts path to blend in and be replicated across domain controllers (“the ransomware executable file was named for the domain in which it was found, in an apparent attempt to blend in”).
- [T1105 ] Ingress Tool Transfer (implied) – The executable was present in the domain NETLOGON share and copied/replicated across DCs via SYSVOL/NETLOGON replication, effectively transferring the tool across multiple hosts (“the location of the binary on the domain controller was shared as the NETLOGON folder … automatically replicated across all domain controllers”).
- [T1489 ] Service Stop – The binary forcefully terminates security, backup, and database processes by enumerating and calling TerminateProcess on matched process names to disable defenses (“killed pid %d (%s)”; iterates through a predefined list of 120 target processes including WinDefend, MsMpEng, Veeam*, Crowdstrike*).
- [T1134 ] Access Token Manipulation (privilege check requirement) – The binary explicitly checks for Administrator membership via AllocateAndInitializeSid and CheckTokenMembership and exits if not elevated, enforcing use of elevated tokens (“main_windows_api_IsRunAsAdmin … AllocateAndInitializeSid … CheckTokenMembership … user not admin. exit”).
- [T1490 ] Inhibit System Recovery – By deleting shadow copies and requiring admin privileges to access system APIs and create daemon processes, the ransomware inhibits recovery mechanisms (“vssadmin delete shadows /all /quiet” and admin requirement to terminate processes and access system APIs).
Indicators of Compromise
- [File path ] Ransomware location on domain controller – C:WINDOWSsysvolsysvol[domain].localscripts (ransomware executable placed in NETLOGON/SYSVOL).
- [File name ] Ransom note and marker – README_Obscura.txt (ransom note decoded from binary and written to C:README-OBSCURA.txt).
- [File hash ] Example ransomware binary identifier – ixesha256:c00a2d757349bfff4d7e0665446101d2ab46a1734308cb3704f93d20dc7aac23 (listed as ransomware executable hash).
- [Scheduled task ] Persistence and execution – SystemUpdate (task created on multiple hosts to execute ransomware), iJHcEkAG (task that enables RDP via netsh on a user machine).
- [Process names ] Targets for termination – examples include WinDefend, MsMpEng, VeeamTransportSvc, Crowdstrike* (ransomware attempts to kill security/backup/database processes; list contains ~120 names).
Read more: https://www.huntress.com/blog/obscura-ransomware-variant