Validin re-tested pivoting and threat-hunting techniques from four recent blog posts (Laundry Bear, phishing/HTTP features, Transparent Tribe, and BlueNoroff) to see which methods still produce novel indicators and active infrastructure. Host response, header/body/hash, DNS/IP, and registration pivots remained fruitful in many cases, producing new domains, IPs, and certificate-based links, while some specific pivots (favicons, title tags, wildcard subdomains) aged out faster. #LaundryBear #TransparentTribe #BlueNoroff
Keypoints
- Replicating Laundry Bear host response pivots produced many new domains (e.g., 1drvms[.]co[.]za subdomains) and banner-hash-linked domains, showing continued viability of banner/host-response pivots.
- HTML/HTTP feature pivots in Validin yielded novel phishing and fake-app domains (e.g., smsecuring[.]com, mailrdx[.]com, and many pages[.]dev Eventbrite lookalikes), though some features like favicons or specific title-tags lost effectiveness.
- Phishing redirector and body/header hash pivots found recently created domains and clusters tied to active campaigns (examples include header_hash dd01ae95… and body hash 539b0037… returning many domains).
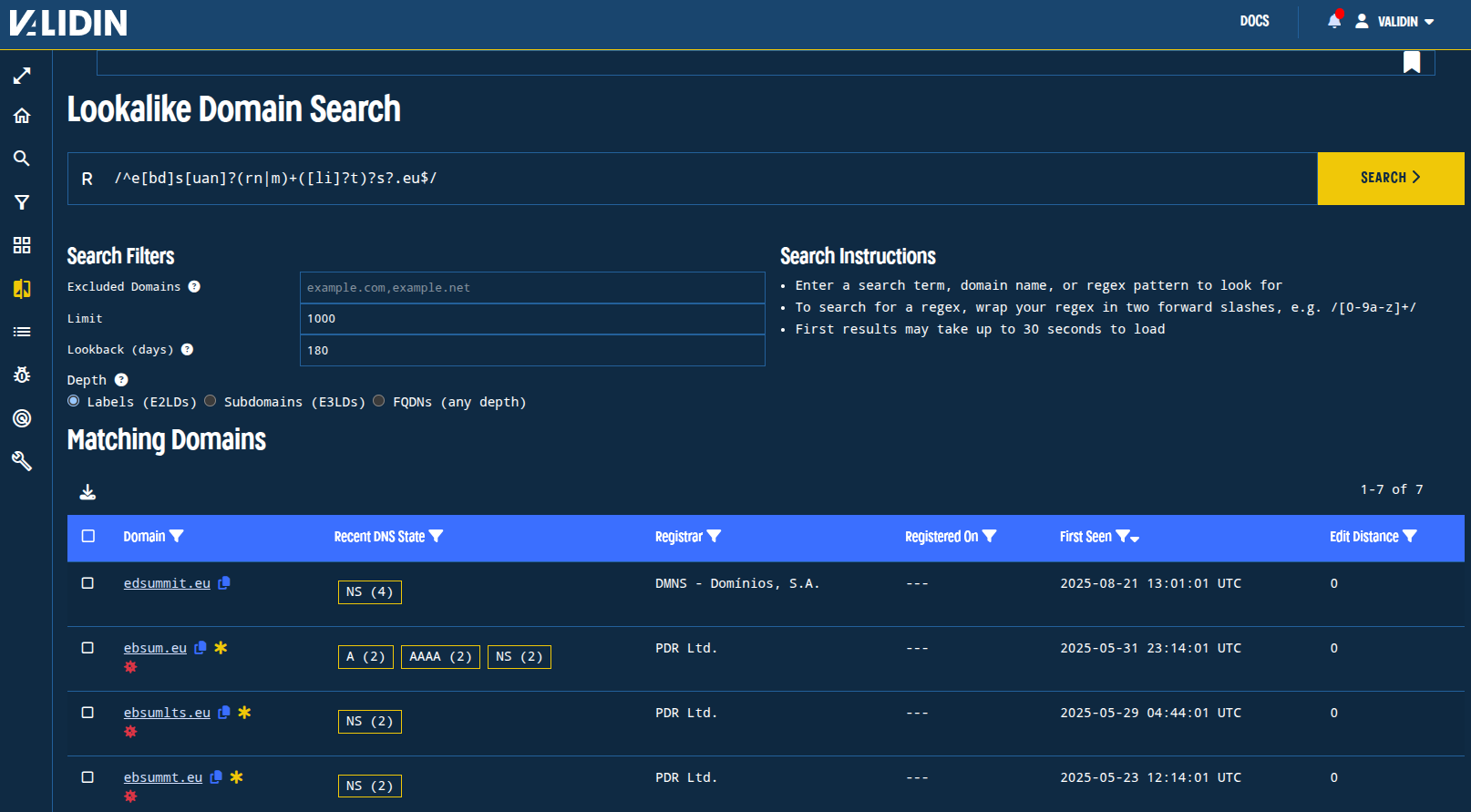
- Transparent Tribe pivots had mixed results: E-TAG pivot remained useful for months, while wildcard subdomains and a specific title tag became stale; fresh Transparent Tribe indicators still yield useful leads (e.g., viewpage[.]xyz).
- BlueNoroff pivots (DNS resolution to 8.8.8.8, IP pivots, certificate/RDP fingerprint pivots, and registration-time pivots) continued to reveal new Zoom-lookalike and Web3-themed domains and active IPs (e.g., 23.254.226[.]83 and 23.254.225[.]152).
- Some pivots cease to be effective over time (favicons, specific title strings, wildcard subdomain enumeration), so continuous monitoring and re-evaluation of pivot value is necessary.
- Overall, following the documented pivoting workflows reproduced reproducible results and surfaced novel indicators long after original publication, validating the methods for ongoing threat hunting.
MITRE Techniques
- [T1583] Acquire Infrastructure – Used by actors to register and host phishing/impersonation domains; article shows pivoting on domain registrations and hosting to find related infrastructure (“…find one additional domain that matches the regex…” and registration-time pivots found batch-registered web3 domains).
- [T1598] Phishing – Phishing redirectors and lookalike domains are used to deliver credential theft, evidenced by continued discovery of redirecting domains to mlpro-trckr[.]com and many Zoom lookalikes (“…domains that are still redirecting to mlpro-trckr[.]com”).
- [T1574] Hijack Execution Flow (Web Shells/Redirectors) – Use of redirector domains and malicious extensions as command-and-control or feeder points; article documents redirector chains and malicious-extension C2 body hashes (“…redirect domains that are still redirecting…”; “body SHA hash to identify suspicious domains used as command and control endpoints”).
- [T1588] Obtain Capabilities (Domain Accounts) – Actors obtain domains and certificates; article documents reuse of certificates and RDP certificate names as pivots (“HTTP certificate fingerprint 38eaff5… continues to be associated…” and RDP certificate domain hwc-hwp-9230840).
- [T1566] Phishing – Use of lookalike Zoom and Microsoft domains to impersonate services and lure victims, demonstrated by many discovered Zoom- and Office365-themed domains (“Zoom lookalike domains”, “micsrosoftonline[.]com lookalike domains”).
- [T1595] Active Scanning – Use of host-response features (banner hashes, header/body hashes) to identify similarly-configured hosts and cluster infrastructure (“banner hash a6b3cc14… observed over 1000 connections across… apex domains”).
Indicators of Compromise
- [Domain ] Laundry Bear/Office365 lookalikes – examples: micsrosoftonline[.]com, 1drvms[.]co[.]za
- [Domain ] Phishing/redirectors and new finds – examples: mlpro-trckr[.]com, smsecuring[.]com
- [Domain ] Malicious extension / body-hash linked domains – examples: r.ytbypass[.]com, lodysource[.]net (and many more such as srcjourneclick[.]net, loadmatchgo[.]com)
- [Domain ] Fake Eventbrite / Pages-hosted invites – examples: partieveie.pages[.]dev, invitee.pages[.]dev (and 40+ similar pages[.]dev domains)
- [IP ] BlueNoroff DNS/IP pivots – examples: 23.254.226[.]83, 23.254.225[.]152
- [IP ] Transparent Tribe historical IPs – examples: 37.221.64[.]134, 45.141.58[.]224
- [Certificate/Hash ] Banner/header/body/hash pivots – examples: HTML SHA1 38c47d338a9c5ab7ccef7413edb7b2112bdfc56f, banner hash a6b3cc14237029c0f1fa9b6de007358a, header_hash dd01ae950b6011988c44, body hash 539b0037602495bc1c16c2fb85a32913f14ae12f