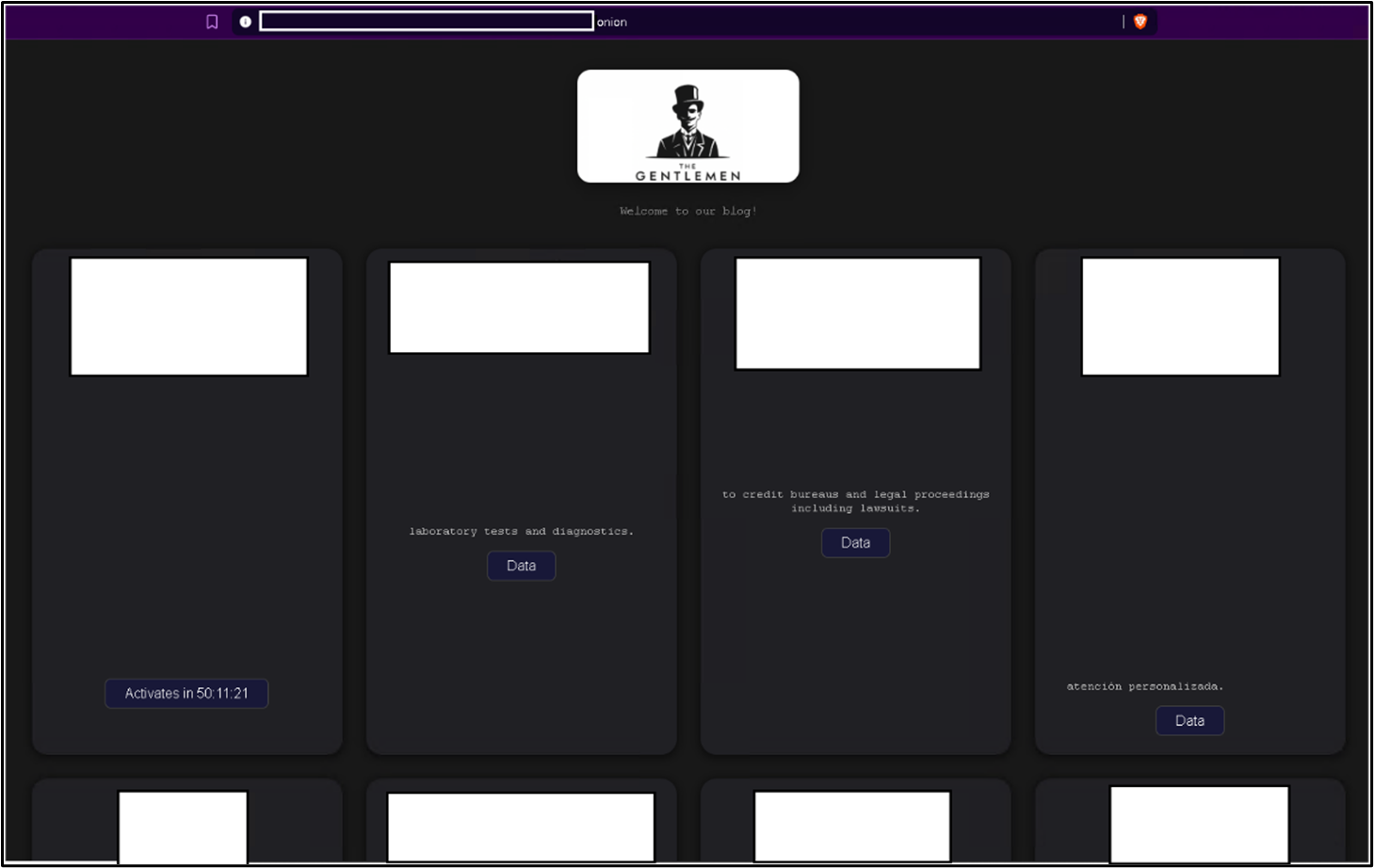
The Gentlemen ransomware group ran a highly tailored campaign using legitimate driver abuse, custom anti-AV tools, Group Policy manipulation, privileged account compromise, and encrypted exfiltration to bypass enterprise defenses and deploy ransomware domain-wide. Victims spanned critical sectors in at least 17 countries, with specific tooling and IOCs including ThrottleBlood.sys, PowerRun.exe, AnyDesk, WinSCP, README-GENTLEMEN.txt, and .7mtzhh. #ThrottleBlood.sys #PowerRun.exe
Keypoints
- The Gentlemen used legitimate driver abuse (ThrottleBlood.sys) and custom tools (All.exe, Allpatch2.exe, KILLAV variants) to disable security products and achieve kernel-level process termination.
- Initial access likely involved exposed internet-facing services (compromised FortiGate admin) or valid credentials, followed by network reconnaissance with Advanced IP Scanner and Nmap.
- Attackers performed extensive Active Directory discovery and mass account enumeration via batch scripts and encoded PowerShell, preparing for domain-wide impact and lateral movement.
- Group Policy manipulation and registry modifications were used to enable RDP, weaken authentication, and deploy domain-wide payloads via NETLOGON share.
- Persistence and C2 relied on AnyDesk and modified registry settings, while exfiltration used encrypted channels via WinSCP and WebDAV connections for staged data.
- The ransomware appended the .7mtzhh extension, dropped README-GENTLEMEN.txt, required an 8-byte –password parameter, and executed broad service/process termination and cleanup to hinder recovery.
- Recommended defenses include Zero Trust controls, MFA for admin interfaces, driver signature enforcement, monitoring for mass AD queries and NETLOGON changes, and endpoint hardening (tamper protection, application control).
MITRE Techniques
- [T1190] Exploit Public-Facing Application – Compromised FortiGate server and admin account via Nmap and exposed FortiGate (“Compromised FortiGate server and admin account via Nmap”).
- [T1078.002] Valid Accounts: Domain Accounts – Use of compromised domain accounts for domain-wide actions (“Compromised domain accounts”).
- [T1046] Network Service Discovery – Nmap executed for service discovery (“Nmap executed for service discovery”).
- [T1018] Remote System Discovery – Advanced IP Scanner used for network mapping (“Advanced IP Scanner used for network mapping”).
- [T1087.002] Account Discovery: Domain Account – Batch script 1.bat queried numerous domain user accounts (“Batch script querying multiple domain accounts”).
- [T1069.002] Permission Groups Discovery: Domain Groups – Enumeration of domain groups and local admin/virtualization groups (“Enumeration of domain groups”).
- [T1482] Domain Trust Discovery – PowerShell used to identify the PDC emulator (“(Get-ADDomain).PDCEmulator” and “Get-ADDomain | Select-Object PDCEmulator”).
- [T1059.003] Command and Scripting Interpreter: Windows Command Shell – Use of cmd.exe to run commands and scripts (“Used cmd.exe to execute different commands”).
- [T1059.001] Command and Scripting Interpreter: PowerShell – Encoded and direct PowerShell used to deploy anti-AV and ransomware (“PowerShell commands used to deploy anti-av and ransomware”).
- [T1562.001] Impair Defenses: Disable or Modify Tools – Stopped security services using anti-AV tools and custom utilities (“Stopped security services using Anti-AV tools”).
- [T1014] Rootkit – Deployed a vulnerable signed driver for kernel-level process termination (“Deployed vulnerable driver for process termination”).
- [T1112] Modify Registry – Registry changes to weaken authentication, enable RDP, and persist (“Registry changes to weaken authentication”).
- [T1562.004] Impair Defenses: Disable or Modify System Firewall – Modified firewall settings to enable RDP remote access (“Modified firewall settings for RDP access”).
- [T1027] Obfuscated Files or Information – Execution of Base64-encoded PowerShell commands (“Execution of base64 encoded PowerShell commands”).
- [T1484.001] Domain or Tenant Policy Modification: Group Policy Modification – Use of GPMC/GPME and encoded PowerShell to deploy domain policies (“GPO manipulation for domain-wide impact”).
- [T1219] Remote Access Software – Installed and used AnyDesk for persistent remote access and C2 (“Installed AnyDesk for remote access.”).
- [T1021.002] Remote Services: SMB/Windows Admin Shares – Used PsExec and NETLOGON share for lateral movement and ransomware deployment (“Used PSExec for lateral movement” and “Ransomware deployed via NETLOGON share”).
- [T1021.001] Remote Services: Remote Desktop Protocol – Enabled RDP via registry modification (“Enabled RDP via registry modification”).
- [T1021.004] Remote Services: SSH – Possible use of PuTTY for SSH-based lateral movement (“Used PuTTY for SSH movement”).
- [T1074.001] Data Staged: Local Data Staging – Data staged in C:ProgramDatadata during collection (“Data staged in C:ProgramDatadata”).
- [T1039] Data from Network Shared Drive – WebDAV connections observed to internal shares (“WebDAV connections to internal shares”).
- [T1071.001] Application Layer Protocol: Web Protocols – WebDAV used for C2 and data movement (“WebDAV used for C&C server and data movement”).
- [T1048.001] Exfiltration Over Alternative Protocol: Exfiltration Over Symmetric Encrypted Non-C2 Protocol – Data exfiltrated using WinSCP (“Data exfiltrated using WinSCP”).
- [T1486] Data Encrypted for Impact – Ransomware encryption deployed across domain with .7mtzhh extension and README-GENTLEMEN.txt (“Ransomware deployed via NETLOGON share”).
- [T1489] Service Stop – Termination of many backup, database, and security services to maximize impact (“Termination of security services”).
Indicators of Compromise
- [File names] Tools and artifacts observed – All.exe, Allpatch2.exe, PowerRun.exe, WinSCP.exe, README-GENTLEMEN.txt.
- [File extensions] Ransomware extension – .7mtzhh appended to encrypted files.
- [Driver] Vulnerable signed driver used for kernel abuse – ThrottleBlood.sys.
- [SHA1 hashes] Ransomware and tools – c12c4d58541cc4f75ae19b65295a52c559570054 (Ransom.Win64.GENTLEMAN.THHAIBE), c0979ec20b87084317d1bfa50405f7149c3b5c5f (Trojan.Win64.KILLAV.THHBHBE), and df249727c12741ca176d5f1ccba3ce188a546d28 (Patched KILLAV); plus e00293ce0eb534874efd615ae590cf6aa3858ba4 (PowerRun detection).
- [Registry changes/commands] Persistence and weakening controls – examples include reg add HKEY_LOCAL_MACHINESYSTEMCurrentControlSetControlLsaMSV1_0 /v RestrictSendingNTLMTraffic /t REG_DWORD /d 0 /f, and Set-MpPreference -DisableRealtimeMonitoring $true -Force.
- [Tools/software] Legitimate utilities abused – AnyDesk (remote access), PsExec (lateral movement), Nmap and Advanced IP Scanner (reconnaissance), PuTTY (possible SSH movement).
Read more: https://www.trendmicro.com/en_us/research/25/i/unmasking-the-gentlemen-ransomware.html