This article walks through a proof-of-concept exploit for CVE-2020-12446 in the eneio64.sys driver (Trident Z Lighting Control v1.00.08), which exposes primitives to map, read and write physical memory and can be loaded on Windows 11 with HVCI enabled. The write-up details obtaining CR3 from the Low Stub, performing virtual-to-physical translations via mapped PhysicalMemory, and abusing those primitives to steal SYSTEM’s token and spawn a SYSTEM shell. #CVE-2020-12446 #eneio64.sys
Keypoints
- eneio64.sys (Trident Z Lighting Control v1.00.08) exposes IOCTLs that map physical memory into user space using ZwOpenSection/ZwMapViewOfSection, allowing read/write access to physical memory from user mode.
- The author loaded the driver on Windows 11 (22H2, 23H2, 24H2) despite HVCI, verified permissive security descriptor rights, and used IOCTL 0x80102040 to map physical memory and IOCTL 0x80102044 to unmap it.
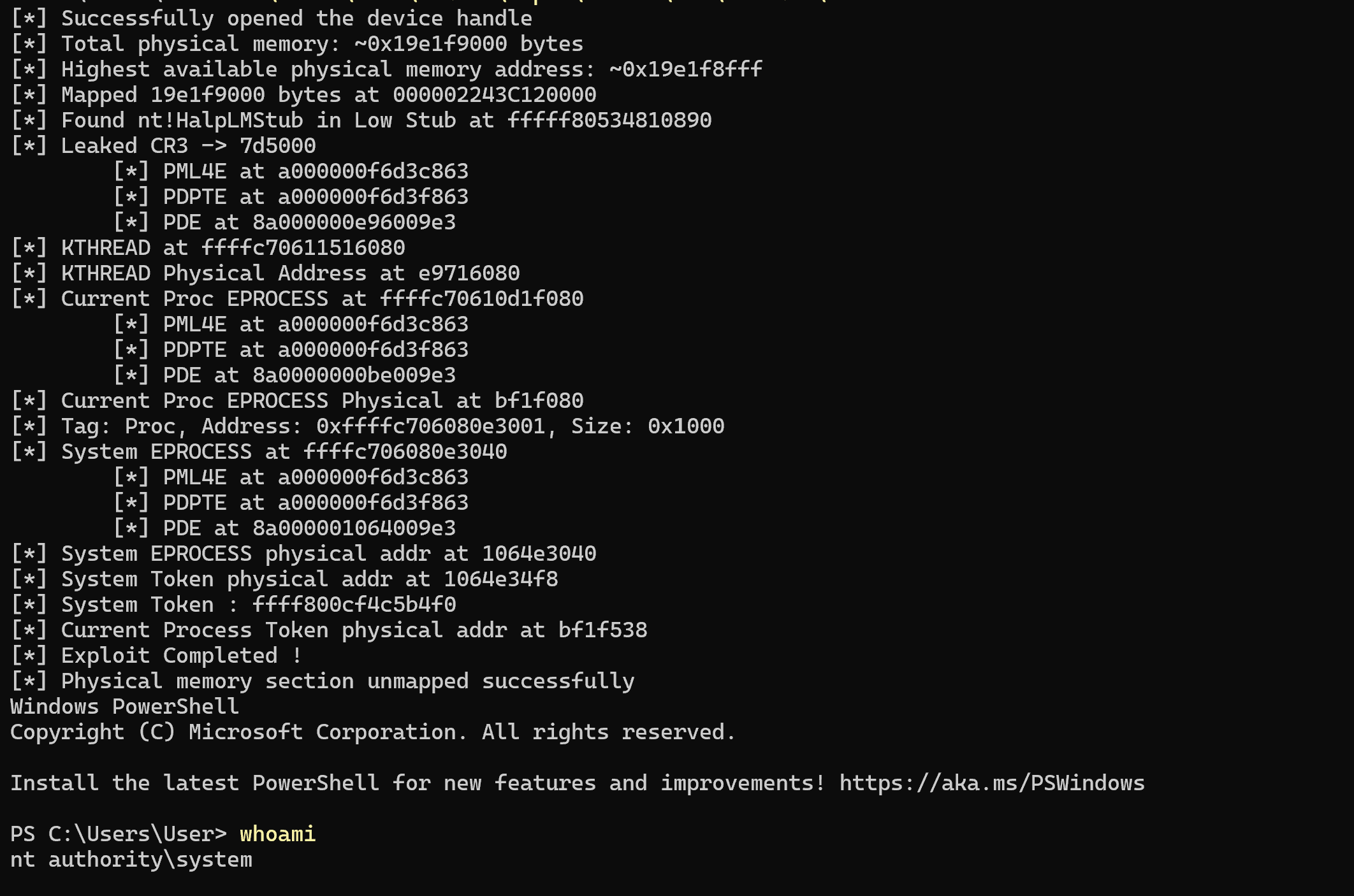
- By mapping the physical memory section starting at physical address 0 and reading the Low Stub range (0x10000–0x20000), the exploit locates nt!HalpLMStub to derive the kernel CR3 value from the Low Stub structure.
- With CR3 and the mapped physical memory, the author implements a virtual-to-physical translation (page-table walk through PML4/PDPT/PDT/PT) to resolve physical addresses for kernel objects.
- The exploit leaks a thread’s KTHREAD via NtQuerySystemInformation(SystemHandleInformation), converts the KTHREAD->Process pointer to a physical address, locates the System EPROCESS via Big Pool scanning (tag ‘Proc’), and reads System’s token.
- System token is copied into the current process token’s physical location, granting NT AUTHORITYSYSTEM privileges and launching a SYSTEM shell; driver unmap is used for cleanup.
- The full exploit code and detailed implementation notes (offsets, structure layouts, and pitfalls such as drivers using MmMapIoSpace) are available in the referenced GitHub repository and blog post.
MITRE Techniques
- [T1612 ] Develop Capabilities – The author developed a proof-of-concept exploit leveraging eneio64.sys IOCTLs and custom virtual-to-physical translation code to read/write kernel memory. Quote: ‘The complete exploit source code can be found here.’
- [T1210 ] Exploitation of Vulnerability – The driver exposes IOCTL 0x80102040 to map physical memory and IOCTL 0x80102044 to unmap it, which is exploited to gain read/write primitives. Quote: ‘IOCTL_WINIO_MAPPHYSTOLIN’ and ‘IOCTL_WINIO_UNMAPPHYSADDR’
- [T1003 ] OS Credential Dumping – The exploit locates and copies the SYSTEM process token into the current process token to elevate privileges to SYSTEM. Quote: ‘Finally, we take System.exe’s token and copy it to the physical address referencing our process’s token.’
- [T1547 ] Boot or Logon Autostart Execution (contextual mitigation discussion) – The article references Microsoft mitigations (Vulnerable Driver Blocklist, HVCI) that aim to prevent vulnerable drivers from loading, informing the attacker’s choice of driver. Quote: ‘Microsoft has reinforced Windows preminution against the loading of vulnerable drivers with the Vulnerable Driver Blocklist… and reinforced with HVCI.’
- [T1082 ] System Information Discovery – The author uses System information APIs (EnumDeviceDrivers, NtQuerySystemInformation for Big Pool and Handles) to find ntoskrnl base, pool addresses, and kernel object addresses. Quote: ‘EnumDeviceDrivers’ and ‘NtQuerySystemInformation2(SystemBigPoolInformation)’
Indicators of Compromise
- [File name ] vulnerable kernel driver used as exploit vector – eneio64.sys (Trident Z Lighting Control v1.00.08)
- [CVE ] vulnerability identifier – CVE-2020-12446
- [IOCTL ] driver control codes exploited – IOCTL 0x80102040 (IOCTL_WINIO_MAPPHYSTOLIN), IOCTL 0x80102044 (IOCTL_WINIO_UNMAPPHYSADDR)
- [Kernel symbol/offset ] ntoskrnl offset referenced – nt!HalpLMStub offset 0x00410890 (used to locate CR3), plus EPROCESS token offset (referenced as EPROCESS_TOKEN_OFFSET) and KTHREAD->Process offset (KTHREAD_PROCESS_OFFSET)
- [GitHub repo ] exploit source location – referenced as ‘The full exploit is available on this Github repository’ (exact repo URL provided in the original article)
Read more: https://xacone.github.io/eneio-driver.html