Check Point Research uncovered the JSCEAL campaign using malicious ads to distribute fake Node.js-based cryptocurrency trading apps, with about 35,000 malicious ads viewed millions of times in the EU during H1 2025. Researchers identified 94 domain IoCs and extensive DNS/WHOIS connections—highlighting mass registrations, typosquatting, and thousands of client IPs communicating with IoCs. #JSCEAL #CheckPointResearch
Keypoints
- Threat actors used malicious advertisements to push fake versions of nearly 50 popular crypto trading apps, distributing JSCEAL variants to victims.
- About 35,000 malicious ads were released in the first half of 2025 and were viewed millions of times in the EU.
- CPR identified 94 domain IoCs and analyzed DNS, WHOIS, and historical data to map infrastructure and relationships.
- Sample DNS traffic (15–19 July 2025) showed 75,172 unique client IPs across 3,271 ASNs made 1,048,575 DNS requests to two IoCs.
- 56 of the 94 domains were flagged by First Watch as likely-to-turn-malicious 63–509 days before being reported as IoCs.
- Analysis uncovered typosquatting groups, registrant-connected domains (31), email-connected domains (280), and IP-connected domains (33), with multiple malicious IPs and domains.
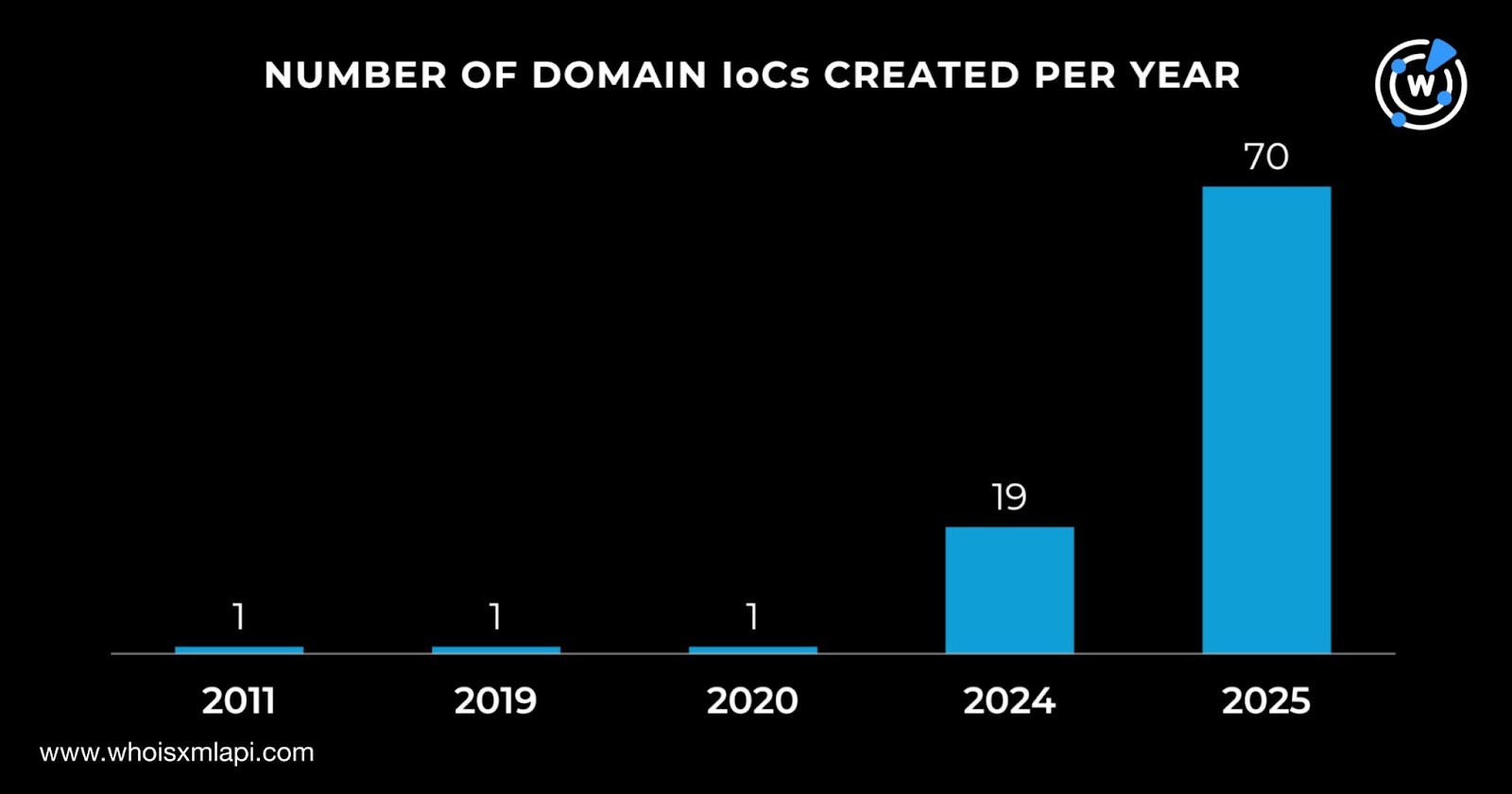
- Most IoC domains were newly created in 2025, primarily registered via a small set of registrars (WebCC, Global Domain Group, Dynadot) and largely registered in the U.S. and Malaysia.
MITRE Techniques
- [T1589] Gather Victim Identity Information – Actors created many look-alike domains and registered dozens of domains to impersonate crypto apps and harvest victims via fake installers (“fake versions of close to 50 of the most popular cryptocurrency trading apps”).
- [T1588] Obtain Infrastructure – Actors registered at least 94 domains and used multiple registrars and hosting providers, including Cloudflare-hosted IPs, to build infrastructure (“18-22-59[.]com, foo-foo[.]bar … were hosted on Cloudflare-administered IP ranges”).
- [T1598] Phishing: Spearphishing via Service – Malicious ads lured users to download fake apps, functioning as a delivery method for JSCEAL variants (“used malicious ads to lure victims to install fake versions … the apps the users downloaded were … masked variants of JSCEAL”).
- [T1583] Acquire Infrastructure: Domains – Bulk registration and pre-flagging of domains occurred, with many domains deemed likely to turn malicious at registration (“56 of the 94 domains were deemed likely to turn malicious upon registration, 63—509 days prior”).
- [T1595] Active Scanning – Analysis observed massive DNS resolution activity with 1,048,575 DNS requests from many client IPs and ASNs interacting with IoCs, indicating large-scale discovery and probing (“75,172 unique client IPs under 3,271 unique ASNs communicated … via 1,048,575 DNS requests”).
Indicators of Compromise
- [Domains] Identified IoCs and look-alikes – examples: apps-downloads-pc[.]com, ohyoulookstupid[.]win, and 92 more domains (total 94 identified domains).
- [IP Addresses] Hosting and malicious IPs – examples: 104[.]21[.]12[.]37, 172[.]67[.]193[.]164 (Cloudflare-administered), and 69 more IPs (total 71 IPs, 70 malicious).
- [DNS Requests / Client IPs] Large-scale DNS traffic – 75,172 unique client IPs under 3,271 ASNs made 1,048,575 DNS requests to IoCs (15–19 July 2025).
- [Email Addresses] Historical WHOIS emails linked to domains – 219 unique historical WHOIS email addresses with 21 public emails, leading to 280 email-connected domains.
Read more: https://circleid.com/posts/into-the-deep-dns-sea-with-the-jsceal-campaign