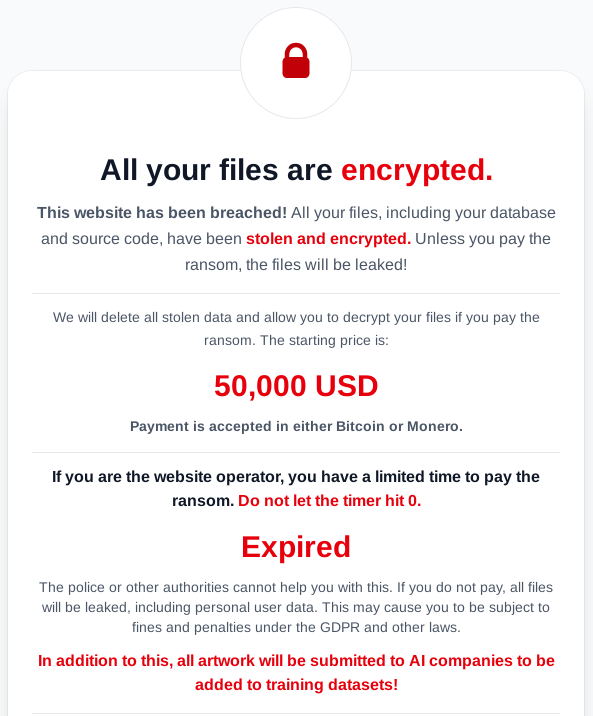
The LunaLock ransomware group claimed to have stolen and encrypted data from a freelance artist-client platform and threatened to publish the data if a ransom is not paid. They added a new extortion dimension by saying they would sell or hand over the stolen artworks to AI companies for model training if the victim does not pay. #LunaLock #AI
Keypoints
- LunaLock claimed responsibility for an attack on a platform connecting freelance artists and clients, stating they stole and encrypted data.
- The group posted a ransom demand on their Data Leak Site and threatened public disclosure of stolen materials if unpaid.
- A novel extortion tactic was disclosed: stolen digital artworks would be provided to AI companies for model training if the ransom is not paid.
- The case highlights how threat actors adapt extortion methods to exploit emerging technologies and market trends.
- This evolution raises specific risks for digital artists, whose creative works can become direct targets and exploited assets.
- The incident underscores the need for creators to prioritize protecting digital content alongside traditional IT security measures.
MITRE Techniques
- [T1490] Data Encrypted for Impact – Threat actor encrypted victim data and demanded ransom; quoted content: ‘…stating they stole and then encrypted the data…’
- [T1530] Data from a Local System/Exfiltration – Data theft from a platform connecting artists and clients was claimed; quoted content: ‘…claimed the attack on a platform… stating they stole…’
- [T1592] Exfiltration to Grid/Multiple Exfiltration Methods – Stolen artworks were threatened to be handed over to third parties (AI companies) for training, increasing pressure on the victim; quoted content: ‘…would deliver the stolen artworks to AI companies for model training.’
- [T1499] Impact – Threat actor threatens reputational damage by releasing stolen materials publicly if ransom is not paid; quoted content: ‘…threaten to publish the stolen material…’
Indicators of Compromise
- [Data Leak Site ] LunaLock posted the ransom claim on their Data Leak Site – no specific URL provided in article.
- [Victim Platform ] Target type and context – a freelance artist-client platform was attacked (platform name not disclosed).