EvilAI is an active global campaign that disguises Node.js-based trojans as legitimate AI or productivity applications—using professional UIs and code-signing—to steal browser credentials, maintain AES-encrypted C2 communications, and persist via scheduled tasks, registry Run keys, and Start Menu shortcuts. Telemetry shows rapid, widespread infections across Europe, the Americas, and AMEA, heavily impacting manufacturing, government/public services, and healthcare. #EvilAI #JustAskJacky
Keypoints
- EvilAI operators distribute malicious applications (e.g., App Suite, Epi Browser, JustAskJacky, PDF Editor, Recipe Lister) that provide legitimate-looking features while executing hidden Node.js JavaScript payloads.
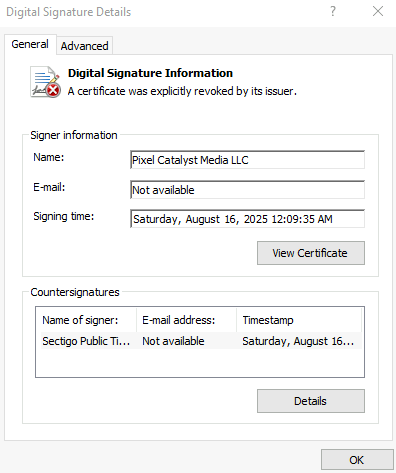
- The malware uses digital signatures from newly registered companies (e.g., App Interplace LLC, Byte Media Sdn Bhd) to appear trusted and evade initial detection.
- Initial access and persistence rely on installers that drop GUID‑named .js files into %TEMP%, launch node.exe via minimized cmd.exe, create scheduled tasks (sys_component_health_{UID}), Start Menu shortcuts, and add Run key entries (PDFEditorUpdater).
- EvilAI performs reconnaissance (WMI and PowerShell to enumerate chrome.exe and msedge.exe), queries registry entries for security/AV products, and terminates browser processes to access credential files.
- The threat steals browser credential data by copying “Web Data” and “Preferences” files and appending “Sync” before exfiltration.
- Network communication uses AES-256-CBC (key derived from instance UUID) and HTTPS to exchange encrypted JSON commands with C2, enabling file download/write, registry modifications, process execution, and arbitrary command execution.
- Malware employs heavy obfuscation (Unicode-escaped strings, control-flow flattening, MurmurHash3-based anti-analysis loops) to hinder static analysis and force dynamic investigation.
MITRE Techniques
- [T1036 ] Masquerading – Malware disguised as legitimate applications with convincing UIs and valid digital signatures (“disguises their malware as legitimate applications…professional-looking interfaces and valid digital signatures”)
- [T1204 ] User Execution – Social engineering and promoted download links encourage users to run malicious installers (“encouraging users to download tools for productivity…promoted download links on forums and social media”)
- [T1053 ] Scheduled Task – Persistence via scheduled task creation named sys_component_health_{UID} that launches node.exe to execute a Temp .js file (“schtasks /Create /TN “sys_component_health_{UID}”… “%LOCALAPPDATA%TEMP{UID}or.js””)
- [T1547.001 ] Registry Run Keys / Startup Folder – Persistence by adding Run key entry PDFEditorUpdater under CurrentVersionRun and Start Menu shortcut creation (“HKEY_USERSSoftwareMicrosoftWindowsCurrentVersionRunPDFEditorUpdater”; Start Menu shortcut PDF Editor.lnk)
- [T1057 ] Process Discovery – Use of WMI/PowerShell to enumerate running processes like chrome.exe and msedge.exe (“Get-WmiObject Win32_Process | Where-Object { $_.Name -eq ‘chrome.exe’ }”)
- [T1485 ] Data Destruction (anti-forensics) – Deletion and cleanup routines via registry delete operations and self-cleaning behaviors (“deleting… reg delete via spawnSync with the /f force flag” and “self-cleaning techniques that temporarily modify system objects before erasing all traces”)
- [T1005 ] Data from Local System – Credential theft by copying browser profile files Web Data and Preferences (renamed with “Sync”) from Chrome and Edge user directories (“created copies of both the ‘Web Data’ and ‘Preferences’ files…append ‘Sync’ to the filenames”)
- [T1059.007 ] Command and Scripting Interpreter: JavaScript – Execution of malicious JavaScript via node.exe launched from cmd.exe to run payloads (“cmd.exe /c start “” /min “%LOCALAPPDATA%Programsnodejsnode.exe” “%LOCALAPPDATA%TEMP{UID}or.js””)
- [T1041 ] Exfiltration Over C2 Channel – Encrypted exfiltration and command/control via HTTPS using AES-256-CBC with keys derived from instance UUID (“AES-256-CBC encryption to secure JSON payloads…key is derived from the malware’s unique instance ID (UUID)”)
- [T1105 ] Ingress Tool Transfer – Remote file download capability using HTTPS GET and fs.createWriteStream to save payloads from C2 (“creates an HTTPS GET request, streams the response data directly to a file using fs.createWriteStream”)
Indicators of Compromise
- [File Names ] Node.js-launched JS payloads and app names – GUID‑suffixed .js files ending in “or”/”ro”/”of” (e.g., {GUID}or.js), and fake app installers like PDF Editor.exe, JustAskJacky.exe
- [Registry Keys ] Persistence and artifacts – Run key PDFEditorUpdater at HKEY_USERSSoftwareMicrosoftWindowsCurrentVersionRun; scheduled task stored at C:WindowsSystem32TasksPDFEditorUScheduledTask
- [File Paths ] Browser credential files copied – Edge/Chrome profile copies such as C:Users{User Name}AppDataLocalMicrosoftEdgeUser DataDefaultWeb Data Sync and …Preferences Sync
- [Digital Signatures ] Observed signer names used to sign samples – App Interplace LLC, Byte Media Sdn Bhd, Echo Infini Sdn. Bhd., GLINT SOFTWARE SDN. B.H.D., Global Tech Allies ltd, Pixel Catalyst Media LLC
- [Commands/Artifacts ] Persistence and execution commands – schtasks creation command (shows sys_component_health_{UID} and node.exe launch), cmd execution pattern “cmd.exe /c start “” /min “%LOCALAPPDATA%Programsnodejsnode.exe” “%LOCALAPPDATA%TEMP{UID}or.js””
Read more: https://www.trendmicro.com/en_us/research/25/i/evilai.html