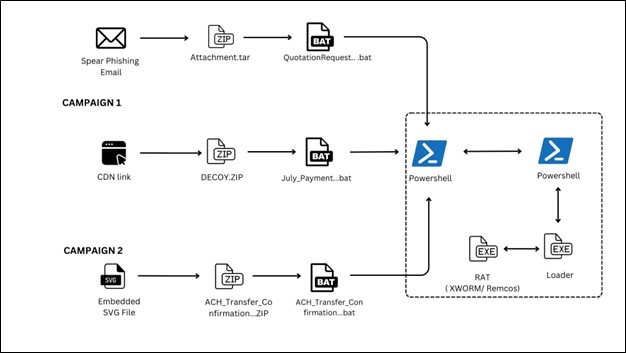
Recent campaigns use obfuscated BAT-based loaders and SVG-embedded JavaScript to deliver in-memory Remote Access Trojans, notably XWorm and Remcos, often via ZIP archives hosted on platforms like ImageKit. The attacks rely on PowerShell decoding, AMSI/ETW disabling, and encrypted .NET/shellcode loaders to achieve fileless execution and persistence. #XWorm #Remcos
Keypoints
- BAT files delivered via EML attachments or ImageKit-hosted URLs serve as the initial access vector and often contain obfuscated content that triggers PowerShell loaders.
- PowerShell scripts decode Base64 content embedded in batch file comments, disable AMSI and ETW via in-memory patches, and execute decrypted payloads in memory.
- Loaders decrypt and execute either .NET assemblies via Assembly.Load or decrypted shellcode using VirtualProtect and delegates to achieve fileless execution.
- Persistence is achieved by placing BAT files in the Windows Startup folder, ensuring execution on user login.
- Campaign 2 uses SVG files with embedded JavaScript to download ZIP archives containing obfuscated BAT scripts, exploiting image rendering and phishing vectors.
- Final payloads observed include XWorm and Remcos RATs, offering capabilities like keylogging, remote command execution, and data exfiltration.
- IOCs include MD5 hashes for BAT, JS, loader, XWorm, and Remcos samples, and detections map to several MITRE ATT&CK techniques focused on execution, evasion, and persistence.
MITRE Techniques
- [T1059.001 ] Command and Scripting Interpreter: PowerShell – PowerShell is used to interpret commands, decode Base64 strings, decrypt and execute embedded payloads in memory. Quote: ‘This PowerShell command runs the script by decoding a Base64 encoded string and executing it in the memory.’
- [T1106 ] Execution Through API – The script uses .NET APIs (Assembly.Load, Invoke) to load and run decrypted .NET assemblies directly in memory. Quote: ‘Assembly.Load followed by .EntryPoint.Invoke, allowing the loader to run managed code without writing the executable to disk.’
- [T1027 ] Obfuscated Files or Information – Payloads are Base64 encoded, AES-encrypted, and compressed to bypass static detections. Quote: ‘Payloads are Base64 encoded, AES-encrypted, and compressed to bypass static detections.’
- [T1140 ] Deobfuscate/Decode Files or Information – The script decodes, decrypts and decompresses payloads from BAT file comments before execution. Quote: ‘It attempts to decode the Base64 string into a byte array…then converts it into a Unicode string…which is then executed in memory.’
- [T1055.012 ] Process Injection: .NET Assembly Injection – Decrypted .NET assemblies are loaded and executed in memory without touching disk. Quote: ‘These variants decrypt the shellcode, modify the memory protections using VirtualProtect…and then execute it using a delegate.’ (describes in-memory execution methods including .NET assembly loading)
- [T1036 ] Masquerading – Malicious content is hidden within batch files and SVG images crafted to appear benign. Quote: ‘The malicious BAT scripts…embedded in SVGs contain JavaScript that triggers the execution chain when rendered.’
- [T1053 ] Scheduled Task/Job – Persistence is established via the Windows Startup folder so BAT files execute on user login. Quote: ‘The malware achieves persistence by creating a BAT file in the Windows Startup folder.’
- [T1204 ] User Execution – Initial access depends on user actions such as opening attachments, previewing SVGs, or executing BAT files. Quote: ‘Execution depends on a user manually running the batch file.’
- [T1132 ] Data Encoding – Base64 and AES encryption are used to encode commands and payloads transmitted or embedded in files. Quote: ‘Base64 and encryption are used to encode commands or payloads.’
- [T1219 ] Remote Access Software – XWorm provides remote access/control capabilities and is used as the final RAT payload. Quote: ‘Xworm provides full remote access and control over the infected host.’
- [T1056.001 ] Input Capture: Keylogging – XWorm includes keylogging functionality to capture credentials and user input. Quote: ‘XWorm includes keylogging functionality to steal user input and credentials.’
- [T1041 ] Exfiltration Over C2 Channel – Stolen data is exfiltrated via the C2 channels used by XWorm. Quote: ‘Stolen data is exfiltrated via the same C2 channel used by Xworm.’
Indicators of Compromise
- [File hash ] Sample file hashes referenced – EDA018A9D51F3B09C20E88A15F630DF5 (BAT), 23E30938E00F89BF345C9C1E58A6CC1D (JS)
- [File hash ] Loader and RAT hashes – 1CE36351D7175E9244209AE0D42759D9 (LOADER), EC04BC20CA447556C3BDCFCBF6662C60 (XWORM), D439CB98CF44D359C6ABCDDDB6E85454 (REMCOS)
- [File name/type ] Delivery artifacts – Obfuscated .bat files (aoc.bat example) and SVG files with embedded JavaScript used to trigger downloads.
- [Hosting platform ] Malicious distribution context – ZIP archives hosted on ImageKit or delivered as EML attachments (ImageKit-hosted URL, EML attachment)
Read more: https://www.seqrite.com/blog/xworm-remcos-bat-svg-malware-analysis/