The article analyzes the Backdoor.Win32.Buterat sample, detailing its persistence, obfuscated strings and API usage (notably SetThreadContext and ResumeThread), dropped files, hashes, and C2 infrastructure. It also provides technical controls and remediation steps including indicators like file hashes and the C2 domain. #Backdoor.Win32.Buterat #ginomp3.mooo.com
Keypoints
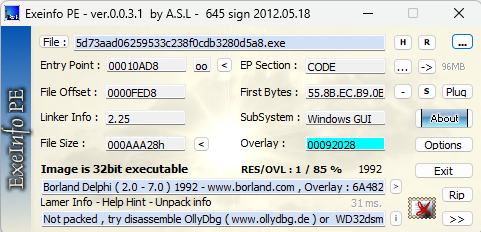
- The sample is identified as Backdoor.Win32.Buterat with provided hashes (MD5, SHA-1, SHA-256) and was compiled with Borland Delphi.
- Static analysis shows encrypted/obfuscated strings likely hiding API calls and execution flow.
- Dynamic analysis identifies entry point at 0x00410AD8, obfuscated API calls, and thread manipulation using SetThreadContext and ResumeThread.
- The malware drops multiple executables in C:UsersAdmin (amhost.exe, bmhost.exe, cmhost.exe, dmhost.exe, lqL1gG.exe) for persistence and further activity.
- Network activity includes communication with a C2 server at http://ginomp3.mooo.com/.
- Recommended mitigations include endpoint protection, network monitoring, firewall/IDS, system integrity monitoring, application allowlisting, and employee training against phishing and malicious downloads.
- Point Wild’s Lat61 platform and threat intelligence team are noted as tracking and defending against this threat.
MITRE Techniques
- [T1055] Process Injection – Uses APIs and thread control (e.g., “SetThreadContext”) to hijack or manipulate existing threads for stealthy payload delivery (‘SetThreadContext’).
- [T1609] Abuse Elevation Control Mechanism – Resumes manipulated threads to continue execution after modification (‘ResumeThread’).
- [T1497] Virtualization/Sandbox Evasion – Employs encrypted and obfuscated strings to hide execution flow and evade detection (‘encrypted or obfuscated strings’).
- [T1105] Ingress Tool Transfer – Drops multiple executable files into C:UsersAdmin (amhost.exe, bmhost.exe, cmhost.exe, dmhost.exe, lqL1gG.exe) to deploy additional payloads (‘Files Dropped during infection’).
- [T1071] Application Layer Protocol – Communicates with remote C2 infrastructure over HTTP to receive commands and exfiltrate data (‘connects to a remote C2 server at http://ginomp3.mooo.com/’).
Indicators of Compromise
- [File Hash ] sample identification – f50ec4cf0d0472a3e40ff8b9d713fb0995e648ecedf15082a88b6e6f1789cdab, c5cdb87162f6e9162a92b461909a3624547e0ec8b9ffe36c2150ec5f78ce1164, and 4 other hashes.
- [File Path ] dropped executables – C:UsersAdminamhost.exe, C:UsersAdminbmhost.exe (also cmhost.exe, dmhost.exe, lqL1gG.exe).
- [Domain ] command-and-control – http://ginomp3.mooo.com/ (C2 server used by the sample).
Read more: https://www.pointwild.com/threat-intelligence/analysis-of-backdoor-win32-buterat