Koi Security and WhoisXML API detailed a coordinated GreedyBear campaign that used 150 malicious Firefox extensions, nearly 500 malicious executables, dozens of phishing sites, and has stolen over US$1 million to date. The investigation identified 18 domain IoCs, additional IPs, email-linked domains, and numerous domain-to-IP resolutions revealing early indicators and artifacts such as trezor-wallet[.]io and snipersol[.]com. #GreedyBear #trezor-wallet
Keypoints
- Koi Security reported the GreedyBear campaign employed 150 weaponized Firefox extensions, ~500 malicious executables, and dozens of phishing sites, resulting in over US$1 million in theft.
- WhoisXML API identified 18 domain indicators of compromise (IoCs) and performed deeper analysis uncovering additional artifacts and connections.
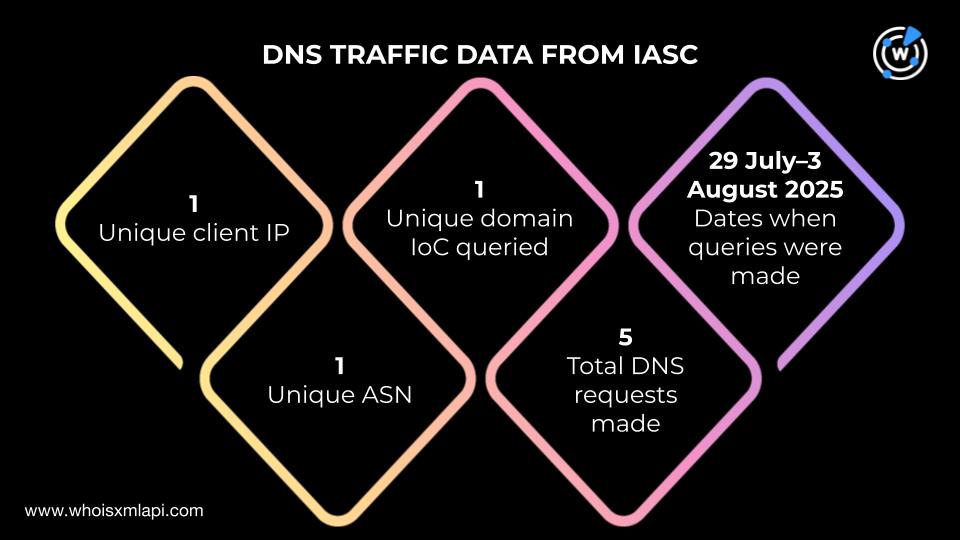
- Analysis of threat intelligence feeds showed one unique client IP queried an IoC domain via five DNS requests between 29 July and 3 August 2025.
- First Watch data indicated five domains were flagged as likely to turn malicious 33–82 days before being officially labeled IoCs on 8 August 2025.
- WHOIS queries found 11 of the 18 IoC domains had current records; 10 of those were created in 2025 and were registered across six registrars with varying registrant countries.
- DNS history analysis revealed 13 of the 18 domains had 255 domain-to-IP resolutions in total, with snipersol[.]com showing 178 resolutions dating back to 2017.
- Detailed look at trezor-wallet[.]io showed it resolves to 185[.]208[.]156[.]66, has 45 subdomains often mimicking popular wallets, and is associated with malware distribution warnings.
MITRE Techniques
- [T1078 ] Valid Accounts – Threat actors used weaponized browser extensions and phishing sites to harvest credentials and access crypto wallets (“…used 150 weaponized Firefox extensions…dozens of phishing sites…”).
- [T1105 ] Ingress Tool Transfer – Actors deployed nearly 500 malicious executables and distributed malware via domains and downloads (“…utilized close to 500 malicious executables and dozens of phishing sites…”).
- [T1566 ] Phishing – Phishing sites were used as part of the campaign to trick victims into installing malicious extensions or revealing wallet credentials (“…dozens of phishing sites…”).
- [T1592 ] Gather Victim DNS Information – Analysis of DNS query logs and domain-to-IP resolutions was used to identify communications and artifact connections (“…one unique client IP address…communicated with one domain identified as an IoC via five DNS queries…”).
- [T1584 ] Compromise Infrastructure – Actors registered and operated multiple domains and subdomains, including domains mimicking legitimate wallet services to host malicious content (“…trezor-wallet[.]io…has 45 subdomains, many of which were crypto wallet-related…”).
Indicators of Compromise
- [Domains ] Primary IoCs and suspicious domains – trezor-wallet[.]io, snipersol[.]com (and 16 other IoC domains)
- [IP addresses ] Resolutions and hosting – 185[.]208[.]156[.]66 (trezor-wallet[.]io resolves here), and 4 unique IPs where 10 domains resolved (three flagged malicious)
- [WHOIS data ] Registrant and creation context – 11 domains had current WHOIS records with 10 created in 2025 and one in 2024; registrars include PDR, NiceNIC, Web Commerce Communications
- [Email addresses ] Historical WHOIS email links – three IoCs had nine historical email addresses leading to one email-connected domain bonkpunk[.]com
- [Domain-to-IP resolutions ] DNS history examples – snipersol[.]com (178 resolutions), extprojectdev[.]top (flagged 82 days before IoC), trezor-wallet[.]io (191 resolutions)
Read more: https://circleid.com/posts/a-deep-dive-into-the-greedybear-attack