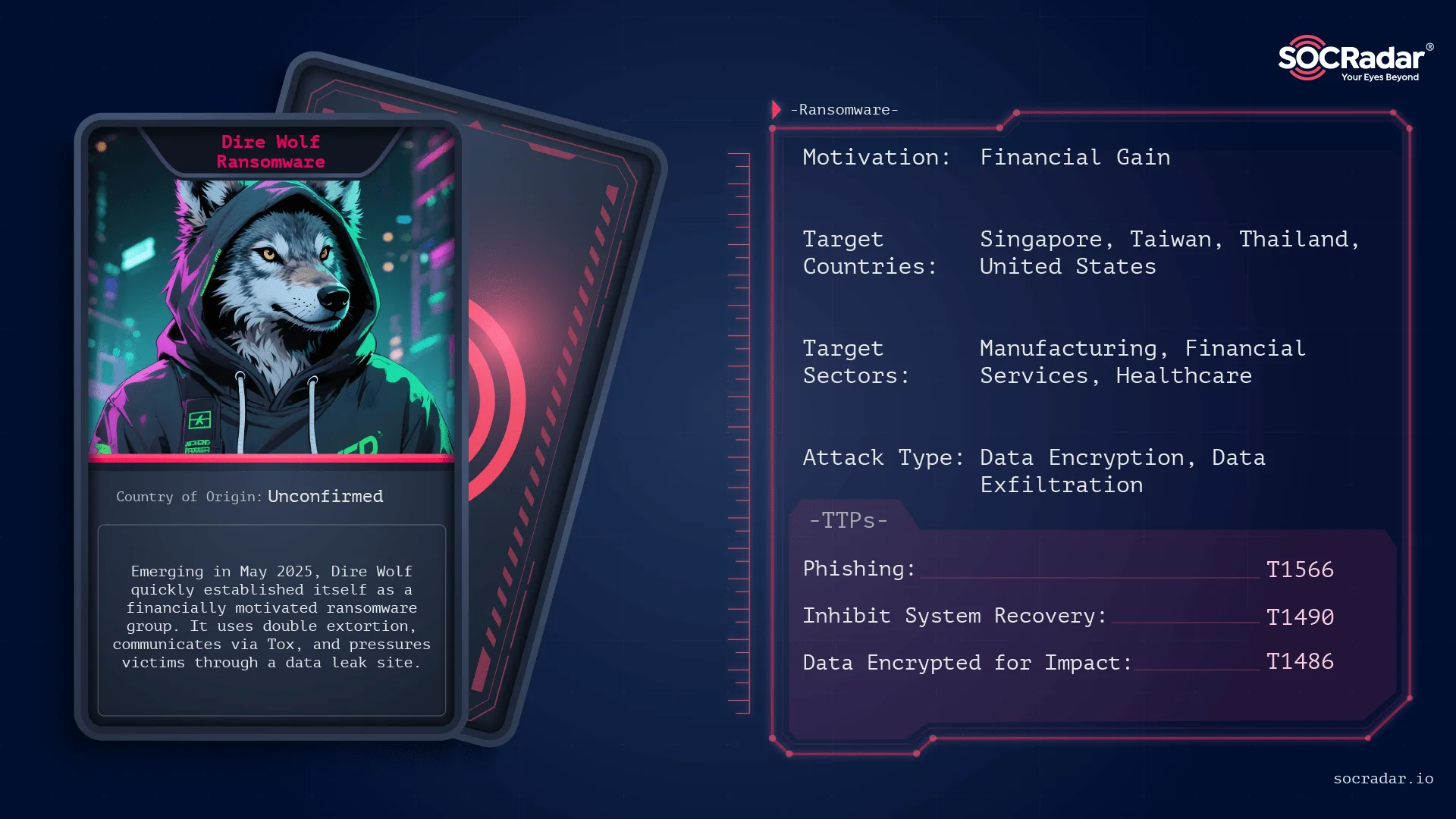
Dire Wolf surfaced in May 2025 as a financially motivated ransomware group that rapidly claimed dozens of victims across Asia, Europe, and North America using a double-extortion model and a Tor leak site for pressure. The group uses a Go-based, UPX-packed payload that encrypts files with ChaCha20/Curve25519, leaves a HowToRecoveryFiles.txt ransom note, and marks files with the .Dire Wolf extension. #DireWolf #HowToRecoveryFiles.txt
Keypoints
- Dire Wolf emerged publicly in May 2025 and claimed responsibility for 41 victims worldwide within months.
- The group operates a classic double-extortion model: steal data, encrypt systems, and threaten publication on a Tor leak site if payments are not made.
- Victims are concentrated in Asia (notably Singapore, Taiwan, Thailand) but include targets in the US, UK, Australia, Brazil, and Canada across multiple sectors.
- Technical indicators include a Go-written, UPX-packed payload, a marker file (C:runfinish.exe), mutex (GlobalDire WolfAppMutex), and the .Dire Wolf file extension.
- Ransom negotiations occur via a Tor negotiation portal and Tox channels, with victim-specific credentials provided in HowToRecoveryFiles.txt and proof data samples available.
- Pre-encryption actions disable recovery and logging (vssadmin, wmic, wbadmin, bcdedit, wevtutil), terminate enterprise services and backups, then encrypt files using Curve25519 and ChaCha20.
- Propagation is human-operated following initial access (spear-phishing, exposed RDP/VPN, credential abuse), with network mapping, privilege escalation, data exfiltration, then coordinated multi-host encryption.
MITRE Techniques
- [T1566] Phishing – Initial compromise likely via spear-phishing emails with malicious attachments (“Initial compromise is likely achieved through spear-phishing emails with malicious attachments”).
- [T1133] External Remote Services – Exploitation of exposed services like RDP or VPN for initial access (“exploitation of exposed services such as RDP or VPN”).
- [T1078] Valid Accounts – Use of weak credentials and credential-based access to gain entry (“weak credential practices” and leveraging compromised accounts).
- [T1086] PowerShell – Restriction recommendation notes misuse of PowerShell as an administrative tool that should be limited, implying its abuse during intrusions (“restrict tools like PowerShell … to administrators only”).
- [T1490] Inhibit System Recovery – Disabling backups and recovery mechanisms using vssadmin, wmic, wbadmin, and bcdedit (“deletes shadow copies, backup catalogs, and recovery options using vssadmin, wmic, wbadmin, and bcdedit”).
- [T1070] Indicator Removal on Host – Clearing event logs with wevtutil to erase forensic evidence (“clears the main event logs … with wevtutil to remove traces”).
- [T1486] Data Encrypted for Impact – Encrypting files with ChaCha20 and appending .Dire Wolf extension to force ransom payments (“ChaCha20 for file encryption … All affected files receive the .Dire Wolf extension”).
- [T1499] Endpoint Denial of Service? (process/service termination) – Stopping processes and services (databases, mail servers, virtualization, backup, AV/EDR) to enable encryption (“forcefully stops processes and services … including database engines … backup solutions … antivirus or EDR agents”).
- [T1041] Exfiltration Over C2 Channel – Data theft prior to encryption and publication on leak site as pressure (“They steal data, encrypt systems, then threaten publication on a Tor leak site”).
- [T1105] Ingress Tool Transfer – Deployment of customized builds and tools across multiple hosts during coordinated manual deployment (“Builds are customized per victim … launch a coordinated, multi-host deployment”).
Indicators of Compromise
- [File Extension] Evidence of compromise – .Dire Wolf extension used on encrypted files.
- [File Name] Ransom note filename – HowToRecoveryFiles.txt (dropped in each directory as the ransom note).
- [File Path / Marker] Host marker file – C:runfinish.exe created after encryption completes.
- [Mutex] In-memory artifact – GlobalDire WolfAppMutex used to ensure single-run behavior.
- [Communication ID] Tox contact identifier – long published Tox ID used for victim negotiations (example: published long Tox ID for contact).
- [Service / Portal] Tor leak portal – known onion address tied to Dire Wolf for publishing stolen data and negotiations (example: Tor leak portal reachable at a known onion address tied to Dire Wolf).
Read more: https://socradar.io/dark-web-profile-dire-wolf-ransomware/