Telecom-targeted phishing campaigns surged in May–July 2025, with attackers abusing brand impersonation, DGA-like domains, and the Tycoon2FA phishing kit to harvest Microsoft credentials and bypass 2FA. ANY.RUN’s Interactive Sandbox, YARA searches, and Threat Intelligence Lookup enabled detection of malicious PDFs, phishing redirects (xjrsel.ywnhwmard[.]es), and recurring sender patterns to produce actionable IOCs and proactive hunting capabilities. #Tycoon2FA #xjrsel.ywnhwmard.es
Keypoints
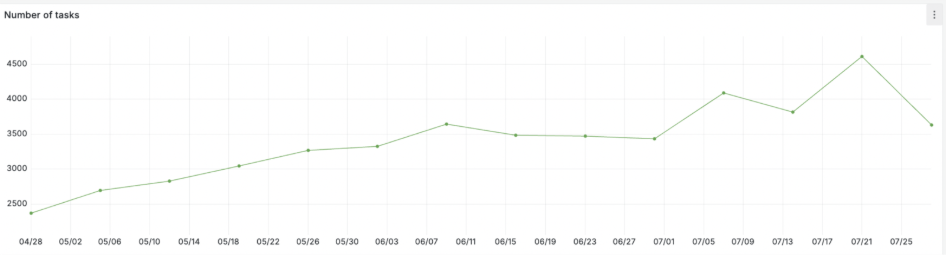
- Telecom and media companies were targeted in 56% of observed APT campaigns from May–July 2025, with peak activity in May and renewed growth in July.
- Attackers weaponize telecom brand trust using logos, official-looking domains, and familiar corporate communication styles to bypass users and filters.
- Tycoon2FA phishing kit is actively used to spoof Microsoft login pages and bypass two-factor authentication in enterprise telecom environments.
- ANY.RUN’s Interactive Sandbox captured full attack chains from malicious PDF attachments to final phishing pages and DGA-like redirect domains (xjrsel.ywnhwmard[.]es).
- Simple YARA rules and pattern-based detection (e.g., sender address structure “._*” ) exposed mass phishing campaigns and enabled bulk extraction of indicators.
- Suricata network detections flagged phishing-related activity and provided MITRE technique context (T1566) and domain telemetry for early warning.
- TI Lookup queries found ~40 UK-related sandbox analyses for a specific PDF hash and revealed 86 sessions and 70 domains when searching for “telecom” in phishing contexts.
MITRE Techniques
- [T1566] Phishing – Phishing emails with malicious PDF attachments and links were used to trick employees: “A phishing email sample detonated in ANY.RUN’s Sandbox” and Suricata alerts referenced T1566.
- [T1204] User Execution – Malicious PDFs and a “Review and Sign” button prompted users to interact and follow redirects to credential pages: “…the PDF attachment to the final phishing page… ‘Review and Sign’ button…”
- [T1110] Brute Force or Credential Access (credential harvesting) – Tycoon2FA spoofed Microsoft login pages to harvest credentials and bypass 2FA: “This threat was identified as the Tycoon2FA phishing kit, known for spoofing Microsoft login pages and harvesting credentials.”
- [T1588] Phishing for Information (use of phishing kits/infrastructure) – Use of Tycoon2FA and DGA-like domains to host fake login pages: “…redirected the user to a fake Microsoft login page hosted on xjrsel.ywnhwmard[.]es… Tycoon2FA phishing kit…”
- [T1583] Acquire Infrastructure – DGA-like domains and automated sender-address generation were used to scale operations and host phishing pages: “…a domain resembling a DGA-generated address… sender address patterns… suggests automated mass phishing.”
Indicators of Compromise
- [Domain] phishing redirect and DGA-like domain – xjrsel.ywnhwmard[.]es (fake Microsoft login hosting) and telecom-containing domains used in phishing clusters.
- [File Hash] malicious PDF sample – sha256:689cdb319d8cae155516d9f8ddfbd0c99de048252e84f529e0ccc538523a5eba (UK submissions), and other related PDF hashes found in ~40 sandbox analyses.
- [Email Addresses / Sender Patterns] automated sender pattern – addresses formatted like “._*” and display names starting with “._” followed by capitalized words, seen across multiple mass phishing emails.
- [Network / Detection Alerts] Suricata alerts and telemetry – Suricata rules triggered on network activity associated with Tycoon2FA, providing domain and connection metadata (e.g., DGA-like domain detections).
- [Campaign Counts] cluster indicators – searches returned ~86 analysis sessions and ~70 related domains when querying for “telecom” + phishing, enabling enrichment of TI feeds.
Read more: https://any.run/cybersecurity-blog/cybersecurity-blog/fighting-telecom-attacks-with-anyrun/