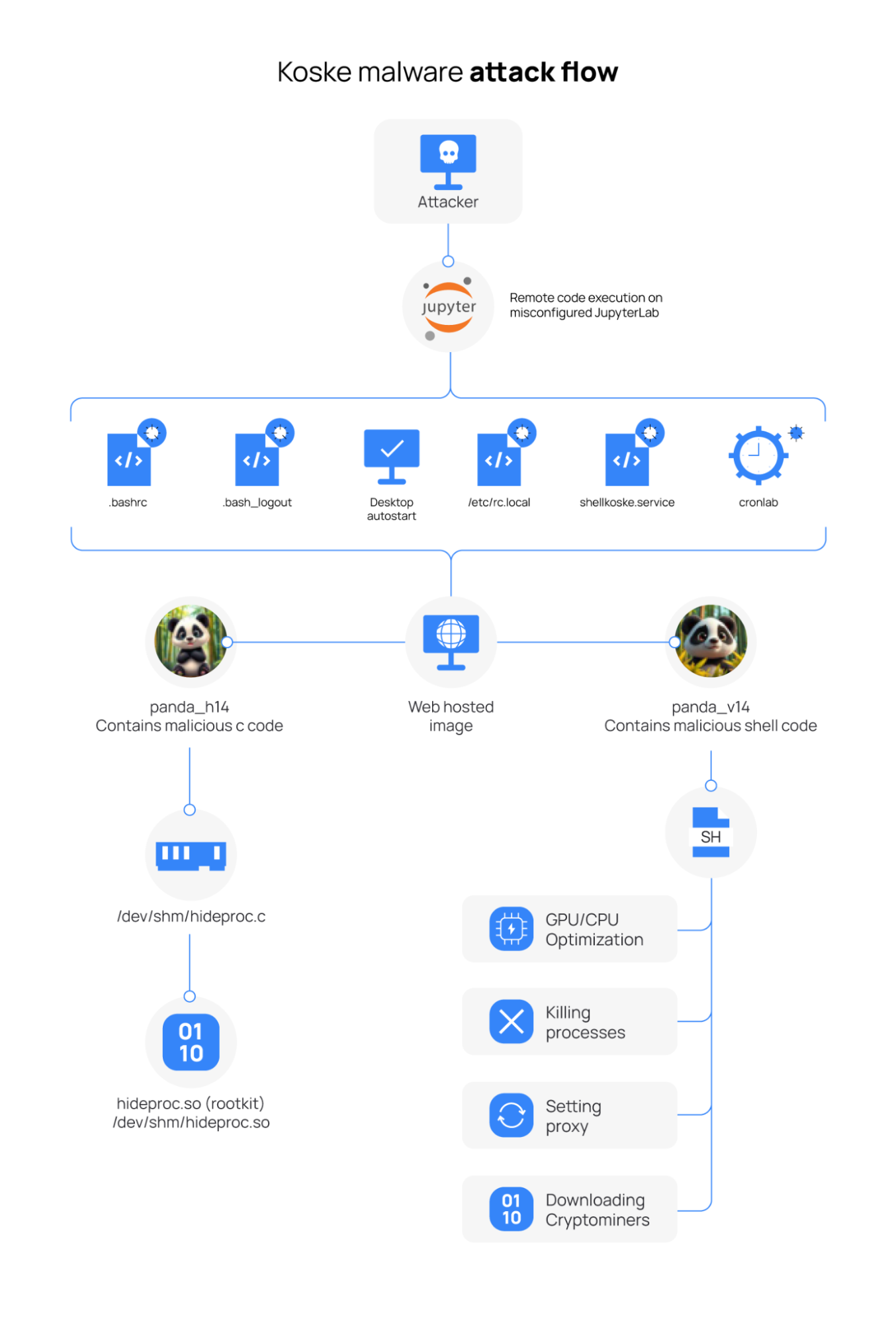
Koske is an AI-generated cryptocurrency-mining malware targeting Linux endpoints that was first identified by Aqua Nautilus in July 2025 and delivered via improperly configured JupyterLab instances using polyglot JPEGs with appended shellcode. It deploys rootkits, establishes persistence via .bashrc and systemd changes, downloads and runs multiple miners (.koske files) against mining pools, and evades detection; detection guidance uses SysmonForLinux and Wazuh rules and CDB hash lists. #Koske #AquaNautilus
Keypoints
- Koske was first identified in July 2025 by Aqua Nautilus and appears to be AI-assisted malware tailored for cryptocurrency mining on Linux.
- Delivery vector: improperly configured JupyterLab (potential CVE-2025-30370) using polyglot JPEGs that contain hidden shellcode and C code appended to image data.
- Malware extracts and executes code in-memory, installs rootkits (often via LD_PRELOAD), and creates persistence via modified bash configuration files (.bashrc.koske) and systemd services.
- Koske downloads miner components using curl and saves them with a .koske extension (examples: nanominer.koske, SRBMiner-Multi.koske, cpuMinerTermux.koske) and launches optimized miners (cpuminer-sse2, nanominer) for multiple coins.
- It hides miner processes using hidden files (e.g., /dev/shm/.hiddenpid), checks for existing miners with pgrep, and connects to external mining pools over TCP (example pool IP 79.137.70.48).
- Detection guidance uses SysmonForLinux to collect enriched logs, Wazuh decoders and custom rules (rule IDs 100801–100806), Rootcheck signatures, and a CDB list of known hashes to trigger alerts.
- Recommended monitoring includes real-time FIM on user Downloads, adding Koske hashes to CDB lists, and configuring Wazuh Rootcheck to detect hidden files and LD_PRELOAD tampering.
MITRE Techniques
- [T1059] Command and Scripting Interpreter – Used to extract and execute shell scripts from JPEGs: “Possible Koske malware activity: Extraction of shellcode from JPEG $(eventdata.CommandLine) into a shell script for execution.”
- [T1027] Obfuscated Files or Information – Polyglot JPEGs contain appended shellcode/C code to evade detection: “skip=[0-9]+ bs=1 if=.*.jpeg of=.*.(sh|c)$”
- [T1105] Ingress Tool Transfer – Malware downloads miner payloads via curl saving files with .koske extension: “Koske malware activity: Download of miner payload via curl $(eventdata.TargetFilename).”
- [T1546.004] Modify Existing Service: Systemd – Persistence via modifications to bash config and creation of .bashrc.koske to maintain access: “Koske malware persistence: creation of modified bashrc file $(eventdata.TargetFilename) to maintain access.”
- [T1562] Impair Defenses / Disable or Modify Tools – Rootkit and LD_PRELOAD usage to hide processes and manipulate system behavior: “Koske malware activity: Creation of rootkit persistence file $(eventdata.TargetFilename) for process hiding.”
- [T1014] Rootkits – Use of LD_PRELOAD and hidden files like /dev/shm/.hiddenpid to conceal miner processes: “Koske rootkit: Hidden PID file for process concealment ::”
- [T1496] Resource Hijacking – Execution of cryptominers and connections to mining pools to hijack CPU/GPU resources: “Koske malware activity: Execution of cryptominer $(eventdata.Image) with mining command $(eventdata.CommandLine).”
- [T1485] Data Destruction (or Covering Tracks) – Deleting bash/wget history and other traces to remove evidence: “Sysmon – Event 23: FileDelete (A file delete was detected) by $(eventdata.image)”.
- [T1204] User Execution – Process creation events and user-executed commands (e.g., running extracted scripts) trigger Sysmon event detections: “Sysmon – Event 1: Process creation $(eventdata.image)”.
- [T1204.002] Malicious or Risky Scripts – Detection of known Koske hashes associated with executed files via CDB list: “A known Koske malware hash detected: $(file)”.
Indicators of Compromise
- [File Hash ] Known Koske payload SHA256 hashes – f8c6c873e8289ebbd52d3fc5b6552129d7e20f8a3466aca2d6f1dd2cdd578780, cf9000db6b026ce350982a7dac67152d1649b0021d4b3f0b2cc7315b254e7161 (and 2 more hashes)
- [File Name ] Miner and artifact filenames observed – nanominer.koske, SRBMiner-Multi.koske (used to store downloaded miner components)
- [File Path ] Rootkit/persistence artifacts – /dev/shm/.hiddenpid (hidden PID file), /root/.bashrc.koske (modified bash config)
- [IP Address ] Mining pool infrastructure – 79.137.70.48 (observed TCP connection from nanominer to mining pool)
- [Vulnerable Service ] Delivery vector context – JupyterLab (improperly configured instance, potential CVE-2025-30370) used to host or allow retrieval of polyglot JPEG lures
Read more: https://wazuh.com/blog/detecting-koske-malware-with-wazuh/