Phantom Taurus is a newly designated Chinese nation-state threat actor that conducts long-term espionage against government and telecommunications organizations across Africa, the Middle East, and Asia, using distinctive TTPs and custom tools. Researchers documented a new .NET IIS-targeting malware suite called NET-STAR (IIServerCore, AssemblyExecuter v1/v2) and a shift from email theft to direct database collection via scripts like mssq.bat. #PhantomTaurus #NET-STAR
Keypoints
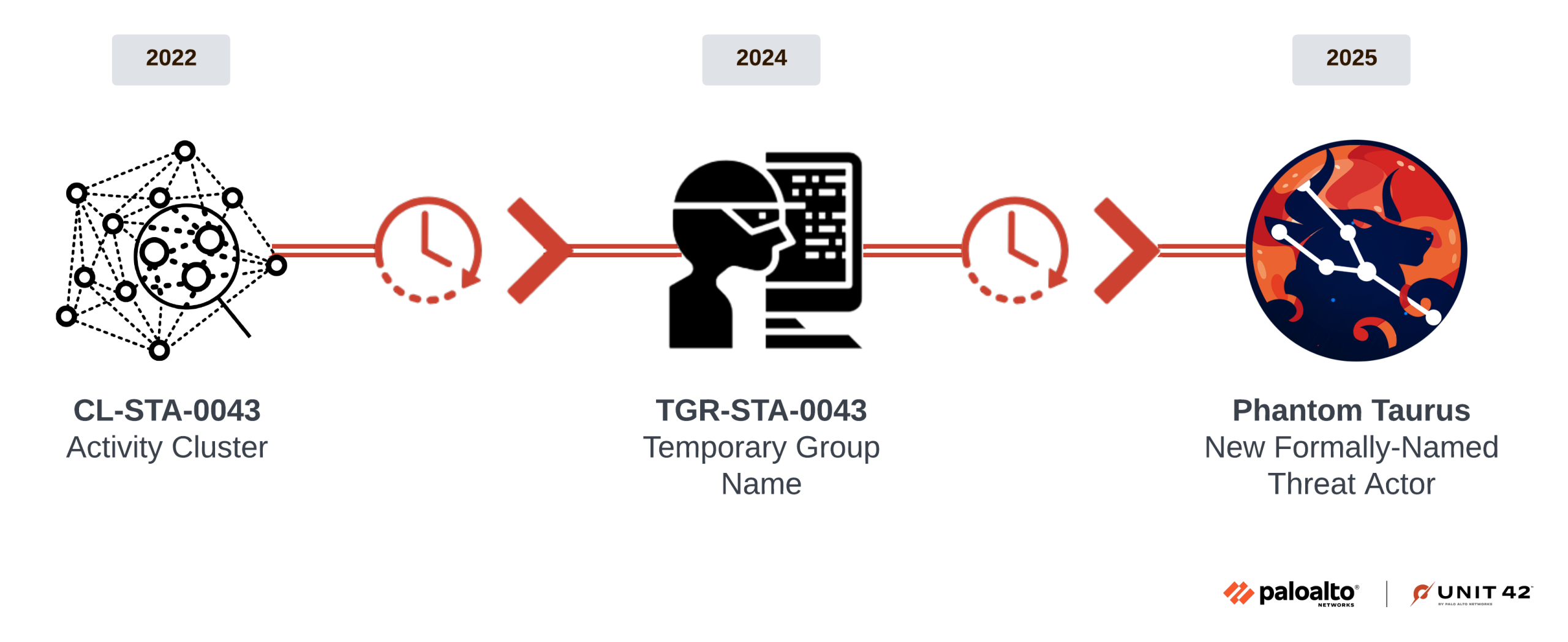
- Phantom Taurus is a newly classified Chinese APT formed from long-term tracking of cluster CL-STA-0043 / TGR-STA-0043 (Operation Diplomatic Specter).
- The group targets ministries of foreign affairs, embassies, telecoms and other high-value government targets across the Middle East, Africa and Asia to collect sensitive non-public intelligence.
- Researchers observed an operational shift from stealing emails to directly querying and exfiltrating database contents using a script named mssq.bat executed via WMI.
- Phantom Taurus developed and deployed a previously undocumented .NET malware suite named NET-STAR that targets IIS web servers and operates largely filelessly in memory.
- NET-STAR consists of three components: IIServerCore (fileless modular backdoor), AssemblyExecuter v1 (in-memory .NET loader), and AssemblyExecuter v2 (adds AMSI and ETW bypasses).
- The group uses timestomping and modified compilation timestamps to hinder forensic analysis and employs encrypted AES-based C2 communications and session management via cookies.
- Unit 42 provided IoCs (multiple SHA256 hashes) and advised Palo Alto Networks protections (WildFire, Advanced Threat Prevention, Cortex XDR/XSIAM) and Unit 42 IR contact information.
MITRE Techniques
- [T1059] Command and Scripting Interpreter – Used to run scripts like mssq.bat to query SQL Server databases and export results to CSV via WMI execution (“the threat actor used this method to search for documents of interest…”).
- [T1041] Exfiltration Over C2 Channel – NET-STAR sends results via an encrypted C2 channel using AES encryption and multi-layer encoding (“sends the results in an encrypted command and control (C2) communication channel”).
- [T1055] Process Injection (in-memory execution) – NET-STAR loads backdoors and assemblies directly into the memory of w3wp.exe and executes payloads in-memory (“loads the backdoor into the memory of the w3wp.exe process” and “loads .NET code from Base64-encoded assemblies”).
- [T1218] Signed Binary Proxy Execution (using WMI) – The actor leveraged Windows Management Instrumentation to execute the mssq.bat script on remote SQL servers (“leveraged Windows Management Instrumentation (WMI) to execute the mssq.bat script on the remote SQL Server”).
- [T1070] Indicator Removal on Host (Timestomping) – The actor timestomped ASPX files and changed compilation times to hide real timestamps (“timestomped the ASPX file… changed the compilation time to a random future date”).
- [T1496] Resource Hijacking (web shells) – Use of ASPX web shells (OutlookEN.aspx) as initial loaders to implant IIServerCore into w3wp.exe (“initial component… an ASPX web shell named OutlookEN.aspx… loads the backdoor into the memory of the w3wp.exe process”).
- [T1110] Brute Force (use of credentials) – Use of acquired SQL credentials (user ID sa) to connect to SQL Server for data collection (“connects to an SQL Server database with a given server name, a user ID named sa… and a password that the attackers previously obtained”).
- [T1140] Deobfuscate/Decode Files or Information – The backdoor uses Base64 encoding/decoding and gzip compression as part of payload handling (“embedded Base64-compressed binary” and methods like Compress/Decompress and EncryptBase64/DecryptBase64″).
- [T1560] Archive Collected Data – The malware compresses data with Gzip before transmission to reduce size and obfuscate traffic (“Compress… compresses it using Gzip… to reduce the size of data it transmits”).
- [T1574] Hijack Execution Flow (web shell to backdoor) – Web shell acts as loader to invoke and run in-memory backdoor code within the IIS worker process (“web shell… loads the backdoor into the memory… and invokes the Run method”).
Indicators of Compromise
- [File Hash] NET-STAR component hashes – IIServerCore (ServerCore.dll) eeed5530fa1cdeb69398dc058aaa01160eab15d4dcdcd6cb841240987db284dc; AssemblyExecuter v1 (ExecuteAssembly.dll) 3e55bf8ecaeec65871e6fca4cb2d4ff2586f83a20c12977858348492d2d0dec4.
- [File Hash] AssemblyExecuter v2 hashes – ExecuteAssembly.dll afcb6289a4ef48bf23bab16c0266f765fab8353d5e1b673bd6e39b315f83676e and b76e243cf1886bd0e2357cbc7e1d2812c2c0ecc5068e61d681e0d5cff5b8e038.
- [File Name] Web shell name – OutlookEN.aspx used as ASPX web shell loader embedding Base64-compressed backdoor.
- [Script] Database access script – mssq.bat used to connect to SQL Server with sa account, execute queries, and export CSVs (used via WMI execution).
- [Tool/Technique] IIS process execution context – w3wp.exe (IIS worker process) used for in-memory execution of NET-STAR components and persistence.
Read more: https://unit42.paloaltonetworks.com/phantom-taurus/