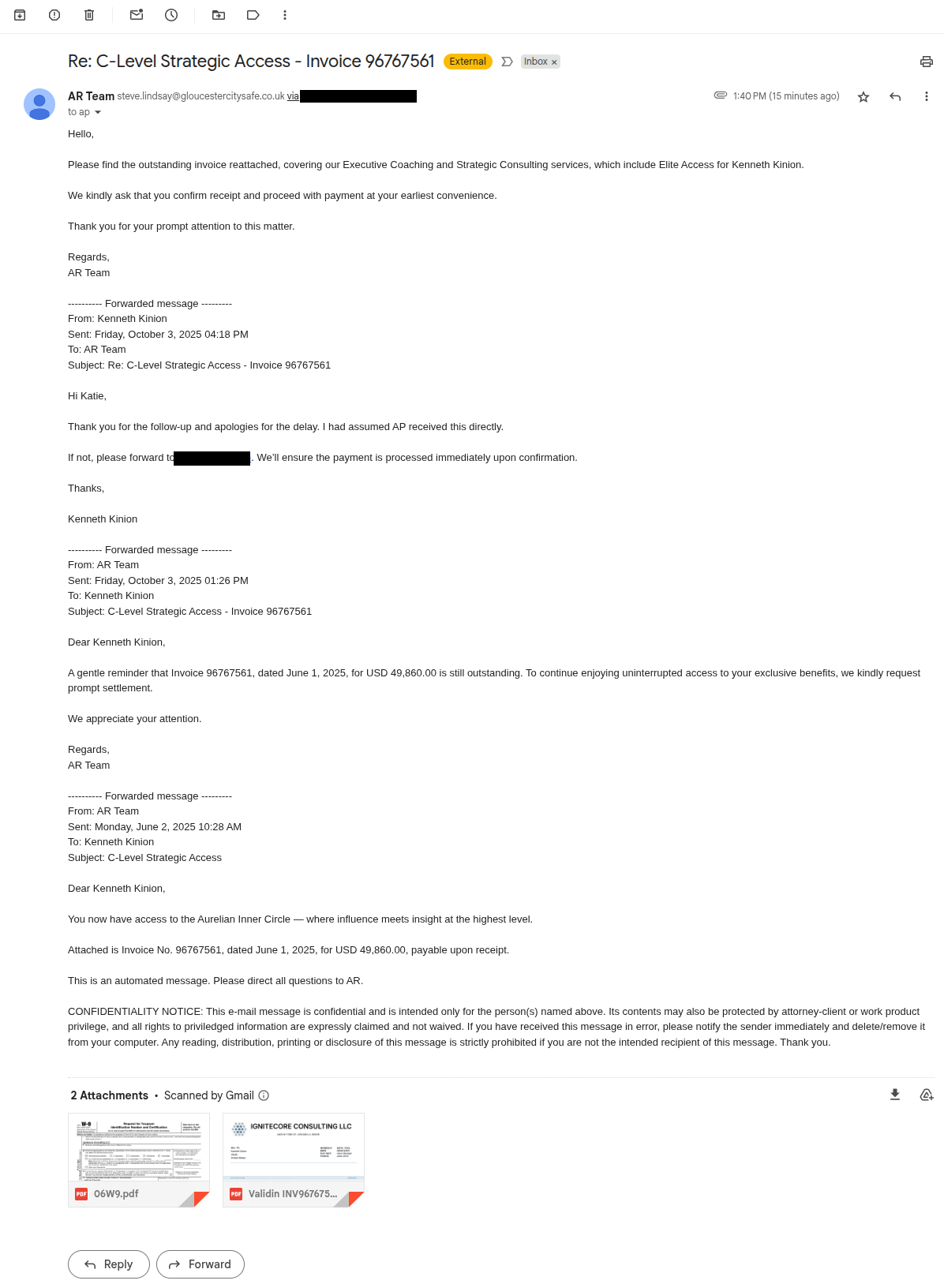
A highly convincing invoice-and-W9 phishing email targeted a Validin employee and used a realistic company identity (Ignitecore Consulting LLC) and reply-to domain to try to collect payments. Investigators pivoted on HTML/CSS template hashes, registration and hosting patterns, self-signed certificates, and Cloudflare origin IPs to identify ~40 related domains and multiple origin IP addresses to block. #ignitecoreconsulting #Cloudflare
Keypoints
- The phishing email included realistic artifacts (invoice, W9 with EIN, matching company name and remittance details) and used a reply-to address to steer responses.
- Ignitecore Consulting LLC” appeared registered in Illinois on Aug 17, 2025, and the reply-to domain ignitecoreconsulting[.]com hosted a single-page landing site mimicking a consulting firm.
- Investigators used Validin pivots on CSS class hashes and HTML title tags to discover a cluster of ~40 related domains sharing templates and naming conventions (consult/llc themes).
- Pivot analysis revealed template reuse and an earlier template variant (CSS hash a5b6e03734433ff58dbe3c80f00bcda2) that expanded the candidate domain list to over 100 names before validation.
- Many domains moved from Hostinger to Cloudflare; researchers identified dangling Cloudflare proxies and recovered origin IP addresses serving the fraudulent content.
- Origin servers used self‑signed certificates sharing identical issuer fields and consistent server headers (specific Apache/OpenSSL/PHP versions), which were pivotable attributes for discovery.
- The investigation produced actionable IOCs (17 origin IPs and ~40 domain names) that were blocked to protect other potential targets.
MITRE Techniques
- [T1598] Phishing for Information – The campaign delivered a convincing fraudulent invoice email with attachments (invoice, W9) and a forged reply-to to collect payment information (“Fraud email requesting payment to invoices, complete with an invoice and a W9 attachment.”).
- [T1588] Obtain Infrastructure – Adversary registered and configured multiple domains and hosting (Hostinger then Cloudflare) to host fraudulent landing pages (“The domain ignitecoreconsulting[.]com hosts a single-page landing page…”).
- [T1592] Gather Victim Identity Information – The attacker leveraged public data and likely data brokers/AI to map employees and craft targeted “boss/CEO” style scams (“it is now incredibly easy and low-cost to map employee-employer relationships, find working contact details, and craft convincing fraud emails”).
- [T1078] Valid Accounts (implication of abusing legitimate registration) – The campaign used legitimately registered LLC and domain registrations (IGNITECORE CONSULTING LLC registered Aug 17, 2025) to appear authentic (“The registration for ‘IGNITECORE CONSULTING LLC’ was less than two months old”).
- [T1566] Phishing – The use of a tailored email with legitimate-seeming documents and reply-to manipulation to induce the recipient to send payment (“the reply-to header in the email ensures that most mail clients will direct replies to a different email address than the one used to send the email.”).
- [T1590] Gather Victim Network Information – The investigation identified origin IP addresses behind Cloudflare and hosting infrastructure to map the campaign’s network (“I uncover the following Cloudflare origin IP addresses: 107.172.232[.]108 …”).
- [T1583] Acquire Infrastructure – Use of multiple domain registrations, hosting providers, and self-signed certificates as part of the campaign’s infrastructure (“most domains are briefly hosted on Hostinger before switching to Cloudflare… self-signed certificate with the same placeholder values in the Issuer field”).
Indicators of Compromise
- [IP Address ] Cloudflare origin/origin-hosting IPs used to serve fraudulent landing pages – 107.172.232[.]108, 78.142.229[.]127, and 15 more IPs (see list in article).
- [Domain ] Fraudulent/related landing page domains used in the campaign – ignitecoreconsulting[.]com, elitemindmgmtllc[.]com, and ~38 other domains (e.g., gsterlingllc[.]com, shamrockconsults[.]com).
- [Certificate Hash ] Self-signed certificate tied to origin content – SHA1 92d8c45fd06cdd0e23ab07b072a47d65e046c7ab (SHA256: 2aef3c5058…), used for elitemindmgmtllc[.]com and other origins.
- [Server Header ] Unique server version strings observed on origin servers – examples include “Apache/2.4.63 (Win64) OpenSSL/3.4.0 PHP/8.2.28” and “Apache/2.4.65 (Win64) OpenSSL/3.5.1 PHP/8.2.29”.
- [DNS/NS Pattern ] Hosting and name server change pattern indicating Hostinger -> Cloudflare transitions – observed Cloudflare names paloma[.]ns[.]cloudflare[.]com and rob[.]ns[.]cloudflare[.]com (context: domains often moved from Hostinger to Cloudflare).
Read more: https://www.validin.com/blog/consulting_invoice_scam/