Socket Threat Research Team discovered 175 malicious npm packages used as hosting infrastructure for a coordinated phishing campaign that targeted 135+ industrial, technology, and energy organizations and delivered credential-harvesting redirects via unpkg.com CDN. The campaign identifier nb830r6x and the beamglea artifacts (beamglea.js, beamglea_template.js) link the infrastructure and automation to a single operation. #beamglea #nb830r6x
Keypoints
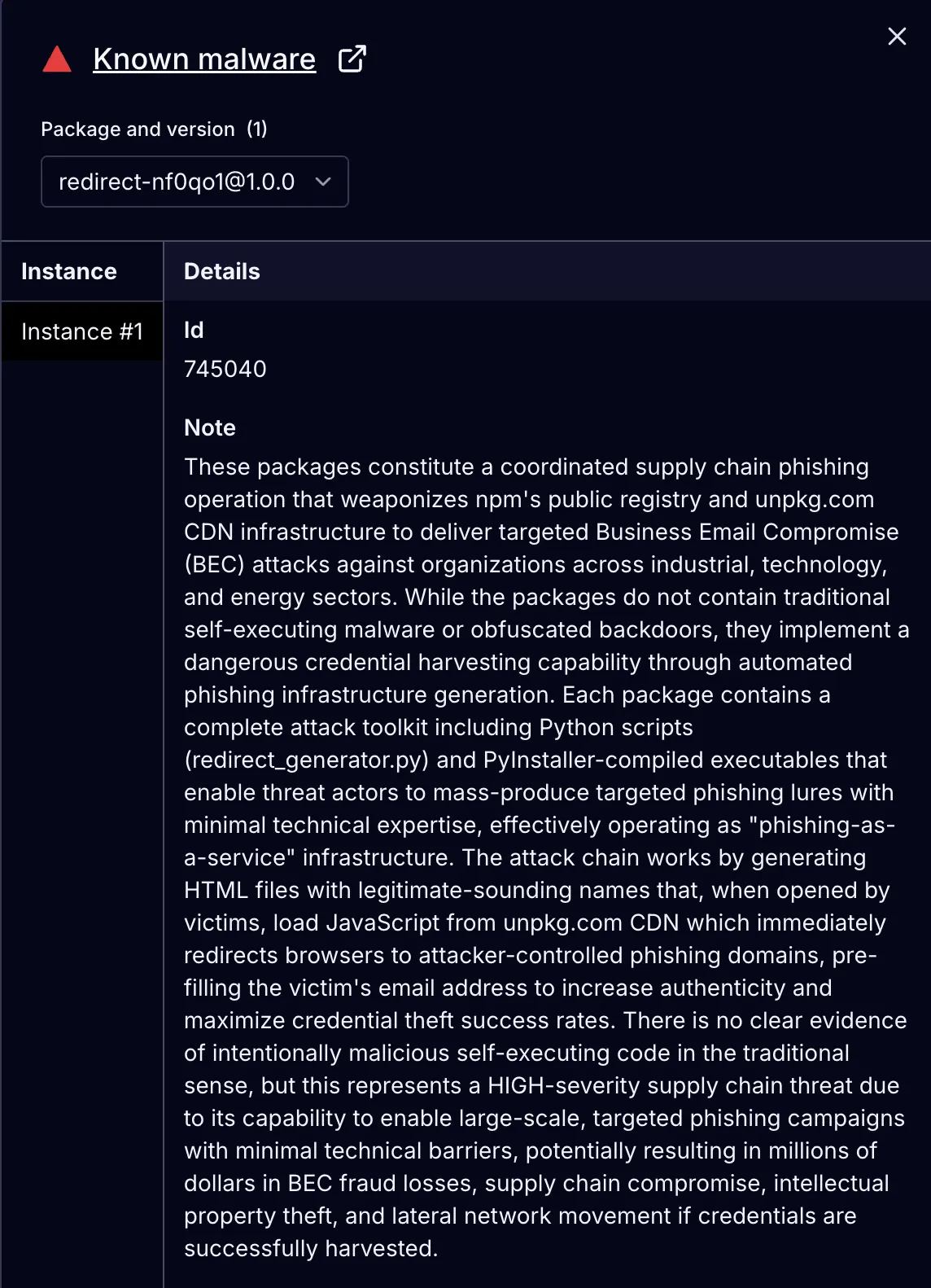
- Threat actors published 175 npm packages (pattern redirect-[a-z0-9]{6}) that are served via unpkg.com and used solely as CDN-hosted redirect scripts.
- Packages contained a simple beamglea.js redirect script that appends the victim email as a URL fragment to phishing pages, enabling pre-filled credential prompts.
- Automation (redirect_generator.py, PyInstaller executables) generated randomized package names, created package.json, published to npm, and produced 630+ HTML lures tailored per victim.
- Campaign targeted 135+ organizations across industrial manufacturing, technology/electronics, and energy/chemical sectors, with heavy focus on Western Europe and no major US targeting.
- Seven phishing domains acted as C2/credential collection endpoints (primary: cfn.jackpotmastersdanske[.]com), some using base64 parameters revealing Office 365 no-MFA targeting (o365_1_nom).
- Operational metadata includes campaign identifier nb830r6x in HTML meta tags, multiple npm author accounts (9), and indicators like redirect-* package names and cdn_setup_guide.txt for long-term infrastructure planning.
- Defensive recommendations: treat IOC detection as active breach, force password resets (prioritizing Office 365), enable MFA, quarantine/strip HTML attachments, monitor unpkg.com redirect-*/beamglea.js requests, and audit email/gateway logs from Sept–Oct 2025.
MITRE Techniques
- [T1195.002] Supply Chain Compromise – Use of npm public registry and unpkg.com CDN as hosting infrastructure for phishing redirects, abusing legitimate package publication flow (“The npm packages themselves don’t execute malicious code when installed via npm. Instead, they exploit npm as free, global hosting infrastructure for phishing attacks.”).
- [T1583.001] Acquire Infrastructure: Domains – Registration and use of seven phishing domains to host credential harvesting pages (e.g., “The campaign uses seven phishing domains: cfn.jackpotmastersdanske[.]com …”).
- [T1584.004] Compromise Infrastructure: Server – Leveraging unpkg.com’s automatic serving of public npm packages over HTTPS to host malicious JavaScript without owning servers (“unpkg.com immediately makes these packages available via HTTPS CDN URLs …”).
- [T1566.001] Phishing: Spearphishing Attachment – Distribution of HTML files themed as purchase orders and project documents that load CDN-hosted scripts to redirect victims (“Possible Phishing Lure Distribution: Threat actors may distribute HTML files themed as purchase orders and project documents to targeted victims.”).
- [T1566.002] Phishing: Spearphishing Link – Use of crafted URLs and HTML attachments that directly navigate victims to phishing pages via unpkg-hosted scripts (“When victims open the HTML file, it loads JavaScript from the unpkg.com CDN … the script redirects victims to phishing pages”).
- [T1056.003] Input Capture: Web Portal Capture – Phishing pages capture credentials and use pre-filled email values via URL fragment to increase believability (“The phishing page reads the email from JavaScript context and pre-fills login forms …”).
Indicators of Compromise
- [npm package names] Malicious npm packages used as CDN hosts – redirect-xs13nr, redirect-nf0qo1, and many others (175 packages total, e.g., redirect-04g1my, redirect-1akzwg, and dozens more).
- [JavaScript file name] Redirect payload file – beamglea.js (served from unpkg.com like https://unpkg.com/[email protected]/beamglea.js) used to append victim email and redirect.
- [HTML lures] Local HTML bait files with campaign meta tag nb830r6x – redirect.html and 630+ lures in package output folders (contain and script references to unpkg URLs).
- [Phishing domains] Credential collection domains – cfn.jackpotmastersdanske[.]com, musicboxcr[.]com, and villasmbuva[.]co[.]mz (total 7 domains used for phishing endpoints and session tracking).
- [Targeted emails] Victim addresses and organizations – sraka@hust[.]hr (appeared in 19 packages) and 135+ other targeted organization emails across industrial, tech, and energy sectors.
Read more: https://socket.dev/blog/175-malicious-npm-packages-host-phishing-infrastructure