Unit 42 tracked phishing campaigns using PhantomVAI Loader (previously Katz Stealer Loader) that employ obfuscated scripts, PowerShell-based steganography, VM detection, persistence mechanisms, and process hollowing to deliver infostealers including Katz Stealer, AsyncRAT, XWorm, FormBook and DCRat. The loader targets diverse industries worldwide and Katz Stealer specifically exfiltrates browser data, wallets, messaging apps and more while avoiding CIS-region systems via language checks. #PhantomVAI #KatzStealer
Keypoints
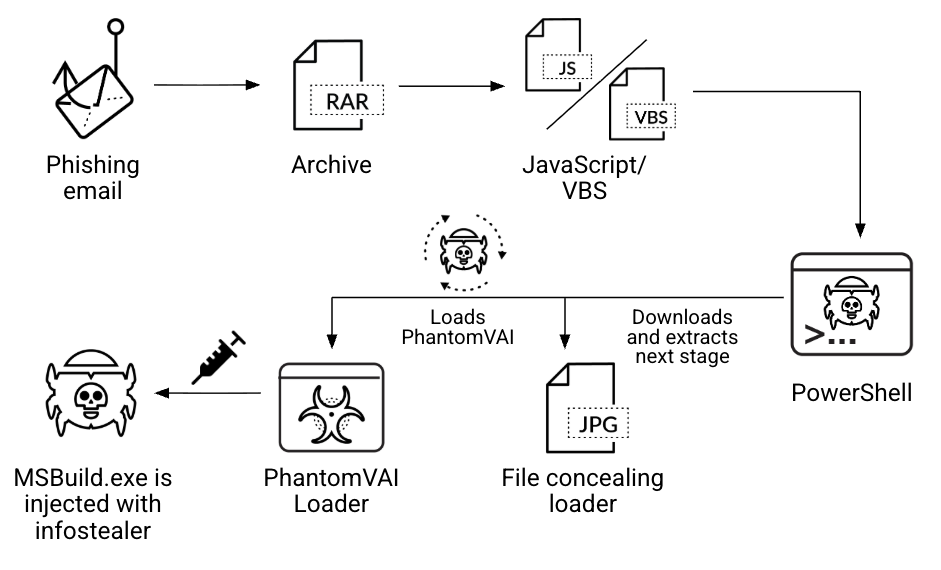
- Phishing emails with obfuscated JavaScript/VBS attachments and homograph techniques initiate the multi-stage infection chain.
- Stage 1 scripts decode and execute embedded Base64 PowerShell that downloads an image/GIF containing a Base64-encoded DLL via steganography.
- The extracted DLL is a .NET loader named PhantomVAI Loader that runs VM-detection checks and exits if a virtual machine is detected.
- PhantomVAI establishes persistence using scheduled tasks, wscript.exe-started scripts, or Run registry keys.
- The loader retrieves a final payload from a C2 URL and injects it into processes (commonly MSBuild.exe) using process hollowing.
- PhantomVAI initially delivered Katz Stealer but now also distributes AsyncRAT, XWorm, FormBook and DCRat as part of MaaS activity.
- Katz Stealer exfiltrates browser credentials, wallets, messaging app data, system info and performs language checks against CIS country codes to avoid execution in those locales.
MITRE Techniques
- [T1566 ] Phishing – Initial delivery via phishing emails containing malicious archived JavaScript or VBS attachments that entice users with themes like sales, payments, and legal actions. Quote: ‘The infection chain starts with a phishing email that contains a malicious attachment.’
- [T1553 ] Steganography – PowerShell downloads a GIF/image that conceals a Base64-encoded DLL; the script extracts text between markers like ‘<>’ and ‘<>’ to retrieve the payload. Quote: ‘The PowerShell script downloads a GIF or other image file that conceals the loader payload.’
- [T1059.001 ] Command and Scripting Interpreter: PowerShell – Obfuscated JavaScript/VBS embed Base64 PowerShell which decodes and executes to download and load next stages. Quote: ‘The script embeds a Base64-encoded PowerShell script and executes it to download and deliver the next stage of the infection.’
- [T1218 ] Signed Binary Proxy Execution (msbuild.exe) – Final payload is injected into legitimate processes, commonly MSBuild.exe, to evade detection. Quote: ‘In most of the cases observed… PhantomVAI Loader injected the payload into the Microsoft Build Engine executable, MSBuild.exe.’
- [T1105 ] Ingress Tool Transfer – PhantomVAI Loader downloads the final payload from a command-and-control URL provided as a parameter. Quote: ‘PhantomVAI Loader downloads the payload from the URL specified as a command-line parameter.’
- [T1543 ] Create or Modify System Process: Scheduled Task / Registry Run Keys – Persistence is established via scheduled tasks executing PowerShell or scripts and Run registry keys. Quote: ‘PhantomVAI Loader uses one or all of the following methods to create persistence: A scheduled task… A Run registry key…’
- [T1055 ] Process Injection (Process Hollowing) – Loader injects decoded payload into a target process using process hollowing. Quote: ‘It then injects this payload into a target process… using the process hollowing technique.’
- [T1518.001 ] System Network Configuration Discovery / System Information Discovery – Katz Stealer collects operating system information and checks system language via GetKeyboardLayout, GetLocaleInfoA, GetSystemDefaultLangID to avoid CIS locales. Quote: ‘Katz Stealer also checks the machine’s language and compares it to a hardcoded list of country codes…’
Indicators of Compromise
- [SHA256 Hash – archive] Example archive hash for phishing attachment – 02aa167e4bb41e3e40a75954f5a0bd5915f9a16fd6c21b544a557f2a7df3c89b
- [SHA256 Hash – JavaScript] Obfuscated JavaScript samples – e663916cc91b4285a1ee762716ff7ce4537153c7893e2d88c13c7e57bbb646a9, 45fddf55acb50df5b027701073dee604b4135f750c585b29d6dcac824f26ae00
- [SHA256 Hash – PhantomVAI Loader] Example loader hashes – 4ab4a37db01eba53ee47b31cba60c7a3771b759633717e2c7b9c75310f57f429, 9ae50e74303cb3392a5f5221815cd210af6f4ebf9632ed8c4007a12defdfa50d (and many more hashes)
- [SHA256 Hash – Katz Stealer] Example Katz Stealer hashes – a6b736988246610da83ce17c2c15af189d3a3a4f82233e4fedfabdcbbde0cff0, 74052cf53b45399b31743a6c4d3a1643e125a277e4ddcfcad4f2903b32bc7dc4
- [File Type – filenames/paths] Common injection target paths – MSBuild.exe under C:WindowsMicrosoft.NETFrameworkv4.0.30319 (used as process hollowing target)
Read more: https://unit42.paloaltonetworks.com/phantomvai-loader-delivers-infostealers/