CERT-AGID identified a fraudulent domain mimicking Italy’s newly launched Entry/Exit System (EES) that solicits surname and document number from non-EU/non-Schengen travelers; the phishing page, registered on 13 October 2025, validates inputs locally via JavaScript against a predefined set and currently does not transmit data to a remote server. The page appears incomplete but may later be used to commit fraud or identity-related forgeries, and CERT-AGID notified the Ministry of Foreign Affairs and requested domain takedown. #EES #CERT-AGID
Keypoints
- CERT-AGID discovered a phishing domain impersonating the Italian Entry/Exit System (EES) shortly after the system went live on 12 October 2025.
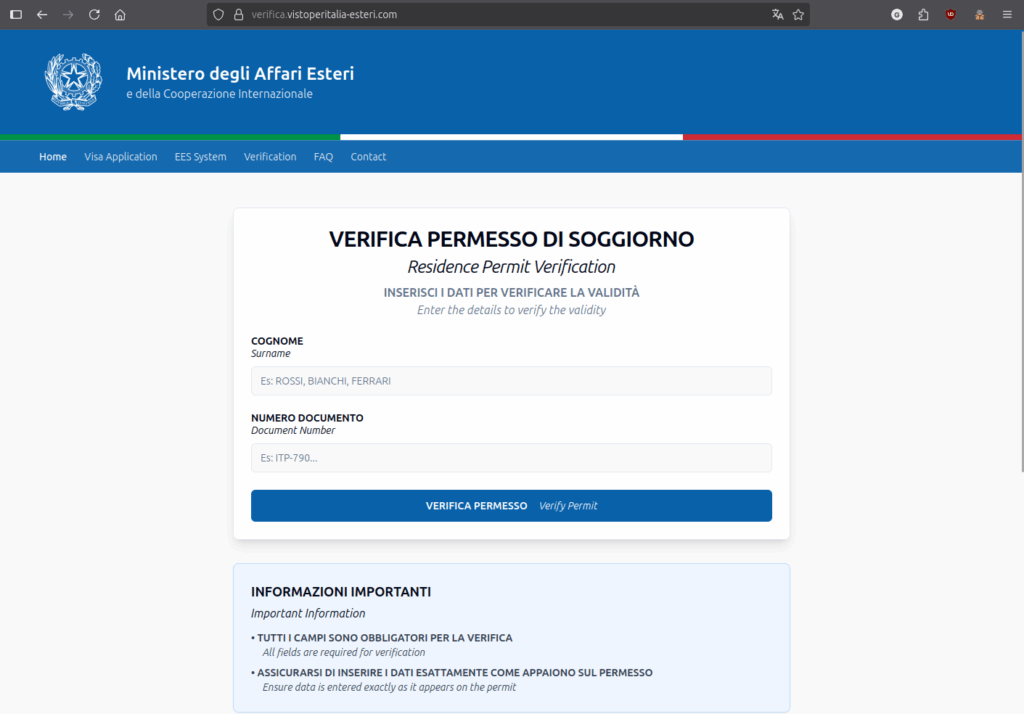
- The fraudulent domain was registered on 13 October 2025 and reproduces misleading official graphics to trick users into entering personal data.
- The phishing page requests surname and document number from users, targeting non-EU/non-Schengen citizens traveling to Italy.
- Analysis showed the page currently validates inputs locally with JavaScript against a predefined object set and does not send data to a remote server.
- The intent of the page is unclear and likely incomplete, but collected data could later be used for frauds such as fake embassy/questura communications or payment extortion to “accelerate” procedures.
- Victims are likely foreigners with limited familiarity with Italian language and public administration online services, increasing their vulnerability.
- CERT-AGID informed the Ministry of Foreign Affairs’ security team, requested domain removal, and distributed IoCs to accredited organizations.
MITRE Techniques
- [T1598] Phishing for Information – The fraudulent site solicits surname and document number by imitating the EES portal (“…invita l’utente a inserire il proprio cognome e numero di documento…” translated: “invites the user to enter their surname and document number”).
- [T1608] Data from Information Repositories (local validation) – The page validates inputs locally via JavaScript against a predefined set of objects rather than transmitting them (“…la verifica delle informazioni avviene localmente tramite uno script JavaScript che confronta i valori inseriti con un set predefinito di oggetti.” translated: “the verification of information takes place locally via a JavaScript script that compares the entered values with a predefined set of objects”).
- [T1593] Spearphishing Link (Impersonation) – The domain impersonates an official public administration service (EES) using deceptive graphics to lure users (“…riproduce una grafica ingannevole…” translated: “reproduces misleading graphics”).
- [T1204] User Execution (Social Engineering) – The attack relies on users entering personal data due to unfamiliarity with the Italian language and services (“…vittime siano cittadini stranieri, che spesso hanno scarsa dimestichezza con la lingua italiana e con i servizi online…” translated: “victims are foreign citizens, who often have little familiarity with the Italian language and online services”).
Indicators of Compromise
- [Domain ] phishing domain impersonating EES – domain registered 13 October 2025 (specific domain withheld in source) and requested for takedown by CERT-AGID.
- [File/Script ] malicious webpage JavaScript – local validation script that compares entered surname/document number with a predefined object set (page observed during analysis).
- [Timestamps ] registration and timeline context – EES went live 12 October 2025; fraudulent domain registered 13 October 2025.