ThreatFabric discovered a Device-Takeover Android Trojan named Datzbro used in social-engineering campaigns that targeted seniors via fake Facebook groups promoting “active senior trips,” enabling remote control, audio/video capture, keylogging, and banking-focused accessibility logging. The malware’s C2 application and builder were leaked, making Datzbro freely available to global threat actors and expanding its use for financial fraud. #Datzbro #Zombinder
Keypoints
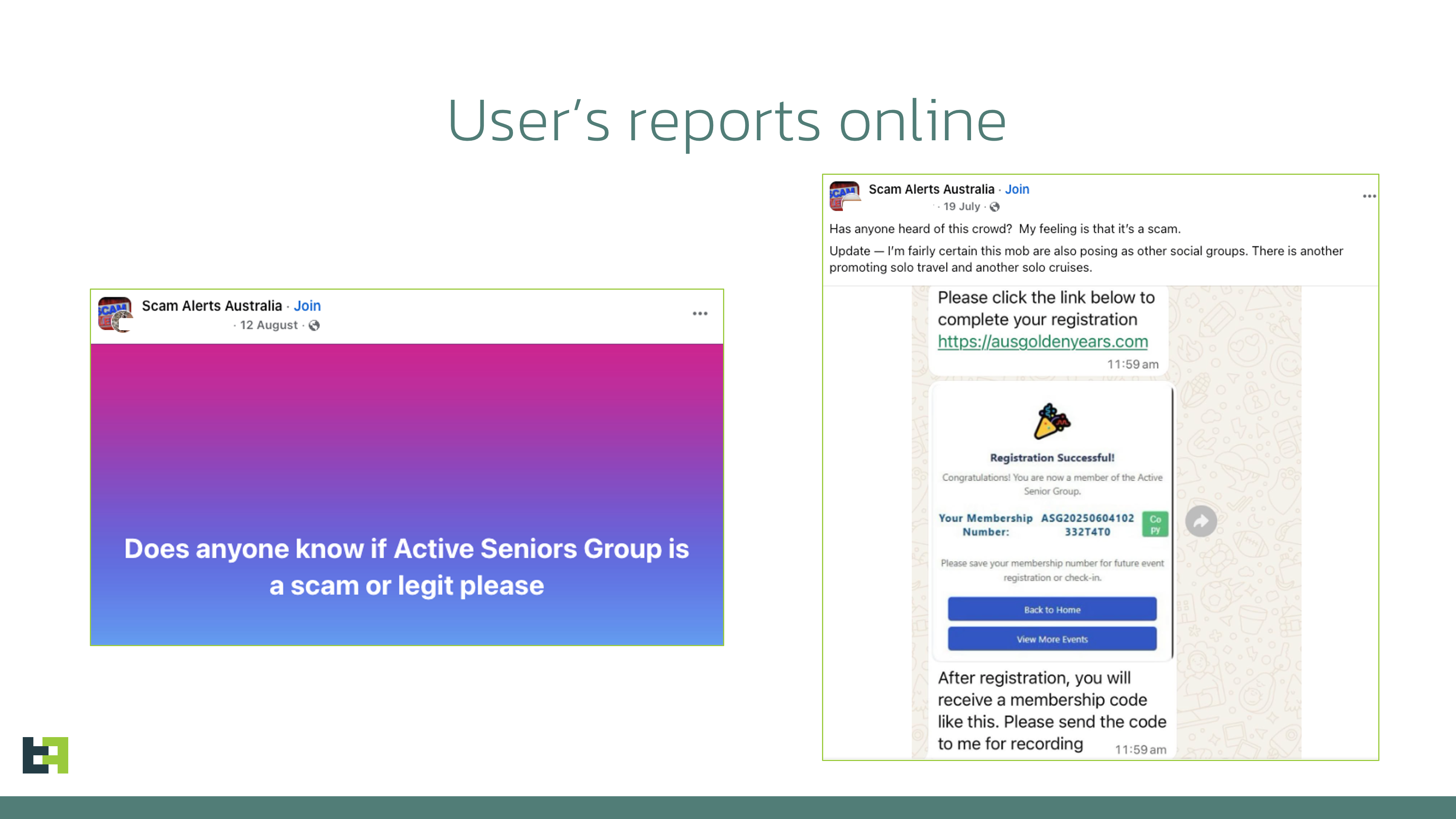
- Threat actors created AI-generated Facebook groups targeting seniors across Australia, Singapore, Malaysia, Canada, South Africa, and the UK to recruit victims for fake events.
- Scammers contacted interested users via Messenger or WhatsApp and directed them to websites offering “community applications,” with Google Play links delivering a malicious APK (Datzbro) or a Zombinder dropper.
- Datzbro is a Device-Takeover Android Trojan with spyware and remote-control capabilities: screen sharing, remote control, file/photo management, audio/video capture, and locking/unlocking devices.
- The malware supports “schematic” remote-control mode and customizable semi-transparent black overlays to hide operator actions from victims while enabling precise interactions.
- Datzbro contains banking-focused features, including hardcoded targets (Alipay, WeChat, device PIN/pattern/password), filters for banking/crypto accessibility events, and password-stealing activities prompting users to enter credentials.
- Analysis of code and C2 interface shows Chinese-language strings and naming, and a compiled C2 desktop application and builder were leaked publicly, suggesting wider distribution among criminals.
- IOCs include multiple SHA-256 hashes and package names tied to malicious APKs (see appendix), underscoring an active global threat exploiting social engineering against vulnerable communities.
MITRE Techniques
- [T1406] Accessibility Features – Datzbro abuses Android Accessibility Services to perform remote actions and interact with UI elements on behalf of operators: ‘Each action corresponds to a single gesture or global function (such as simulating Home or Back button clicks).’
- [T1204] User Execution – Victims are lured to install malicious APKs via social-engineered Facebook groups and messaging: ‘fraudsters then contacted victims via Messenger or WhatsApp and shared links to download an application to register for the activities.’
- [T1525] Data from Local System – Datzbro exfiltrates files, photos, and other local data via file and photo management commands: ‘Photo Stealer (list albums, upload photos, delete photos)’
- [T1436] Screen Capture – The malware supports screen streaming and “schematic” remote control sending UI element data to operators: ‘Start / stop remote screen sharing’ and ‘schematic mode… Sending information about all the elements displayed on the screen, its position and content.’
- [T1056] Input Capture (Keylogging) – Datzbro records keystrokes and accessibility events for credential theft and banking targets: ‘With the help of keylogging capabilities Datzbro can successfully capture login credentials for mobile banking applications entered by unsuspecting victims.’
- [T1496] Overlay – Uses semi-transparent black overlays to hide fraudulent activity and prompt fake credential activities: ‘Black overlay… helps operator to hide their activity from a victim’ and ‘activities will request user to enter their PIN codes.’
- [T1112] Modify Registry/Service (C2 Application) – C2 is implemented as a leaked desktop application allowing operator control and configuration updates: ‘Datzbro command and control panel is a desktop application… a compiled version of the C2 app leaked to public virus share.’
Indicators of Compromise
- [SHA-256] Malicious APK samples – a57d70b2873d9a3672eda76733c5b2fb96dca502958064fab742cfc074bf0feb, 453b0a62e414e9b40185c63842546fc96e8e1ab3f77d3230b02988dd8834c555 (and 2 more hashes)
- [Package name] Infected package identifiers observed on Android – twzlibwr.rlrkvsdw.bcfwgozi, orgLivelyYears.browses646 (and com.forest481.security, inedpnok.kfxuvnie.mggfqzhl)
- [Application name] Reported app labels used by samples – Senior Group, Lively Years, ActiveSenior, DanceWave (used to masquerade as community/event apps)
- [Infrastructure / Tool] Dropper/tool used to bypass Android 13+ restrictions – Zombinder (observed delivering Datzbro in some cases)
Read more: https://www.threatfabric.com/blogs/datzbro-rat-hiding-behind-senior-travel-scams