A Morocco-based financially motivated group tracked as CL-CRI-1032 (overlapping with Atlas Lion/STORM-0539) runs the Jingle Thief campaign, using phishing and smishing to steal Microsoft 365 credentials and carry out large-scale gift card fraud by abusing cloud services. Their tactics include tailored phishing, inbox rules for silent exfiltration, device/Authenticator registration in Entra ID for persistent MFA-resistant access, and operations often originating from Moroccan IP infrastructure. #JingleThief #CL-CRI-1032
Keypoints
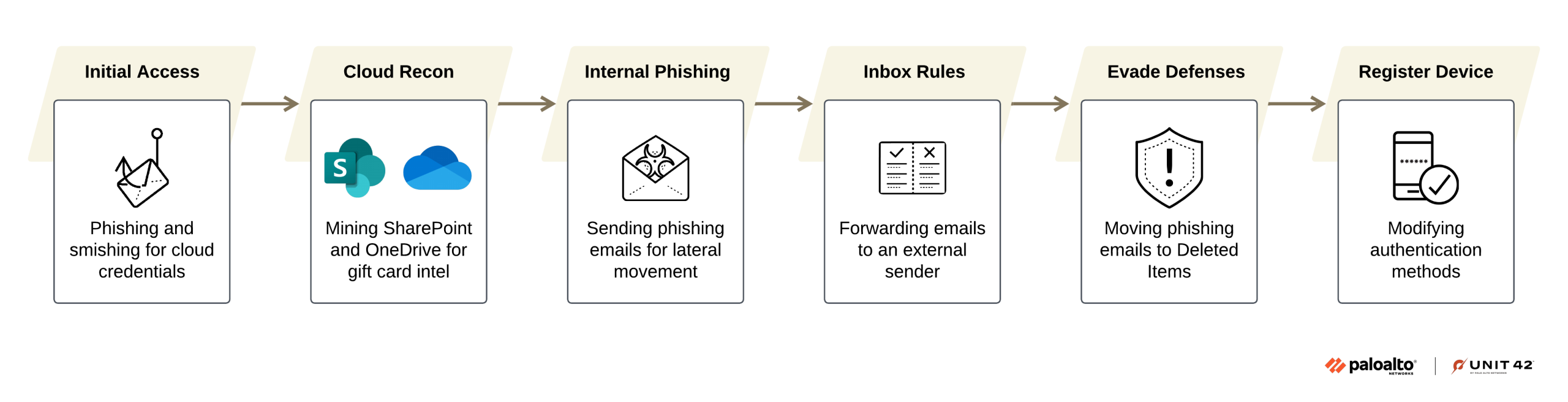
- Jingle Thief is a credential-based campaign attributed to Morocco-based financially motivated actors tracked as CL-CRI-1032 who target retail and consumer services organizations to issue unauthorized gift cards.
- Initial access is achieved via highly tailored phishing and smishing that mimic Microsoft 365 or trusted third-party login portals, often using deceptive URL formats and self-hosted PHP mailers from compromised WordPress servers.
- Post-compromise activity focuses on cloud reconnaissance in Microsoft 365 (SharePoint, OneDrive, Exchange, Entra ID) to find gift-card issuance workflows and related documentation for monetization.
- Attackers expand laterally through internal phishing from compromised accounts and create mailbox rules to forward or hide emails, enabling silent monitoring of approvals and financial workflows.
- Persistence is achieved by abusing Microsoft Entra ID features: registering rogue authenticator apps, enrolling attacker-controlled devices, and using self-service password reset flows to maintain access after remediation attempts.
- Campaign activity frequently aligns with holiday periods to maximize gift card monetization and often originates from IPs and ASNs geolocated to Morocco, with recurring domain naming patterns.
- Palo Alto Networks detections (Cortex UEBA, ITDR, Advanced Email Security) can surface behavioral anomalies like inbox forwarding, mailbox item moves, impossible travel, and massive cloud downloads tied to this activity.
MITRE Techniques
- [T1566] Phishing – Used to harvest Microsoft 365 credentials via tailored email and smishing lures and counterfeit login portals: “…lure victims to counterfeit Microsoft 365 login portals that mimic legitimate sign-in pages.”
- [T1193] Spearphishing via Service – Internal phishing from compromised accounts to move laterally and harvest credentials: “…after compromising a user’s Microsoft 365 account, the attackers sent phishing emails from the legitimate account to personnel inside the same organization.”
- [T1530] Data from Cloud Storage – Mining SharePoint and OneDrive for gift-card workflows and internal documentation: “…perform extensive reconnaissance within the Microsoft 365 environment, particularly focusing on SharePoint and OneDrive.”
- [T1078.002] Valid Accounts: Domain Accounts – Direct authentication to Microsoft 365 using stolen credentials and SSO access from new ASNs/devices: “After harvesting credentials… the attackers authenticated to Microsoft 365 directly and began navigating the environment”
- [T1586] Compromise Accounts – Account compromise detected via impossible travel, first SSO from ASN, or new-country logins: “First connection from a country in organization… Impossible Traveler – SSO”
- [T1564.008] Hide Artifacts: Email Hiding Rules – Creation of inbox forwarding and folder moves to hide phishing activity and responses: “…create inbox rules to automatically forward emails… Moving sent phishing emails immediately from Sent Items to Deleted Items”
- [T1070.008] Indicator Removal: Clear Mailbox Data – Moving or deleting mailbox items to reduce forensic traces: “The Exchange audit logs… show the attackers moving phishing email replies from the Inbox folder to the Deleted Items folder.”
- [T1136.001] Create Account: Local Account – Registering rogue authenticator apps and enrolling attacker-controlled devices in Entra ID to maintain persistence (abuse of identity/device registration): “Registering rogue authenticator apps to bypass MFA… Enrolling attacker-controlled devices in Entra ID”
Indicators of Compromise
- [IP Addresses] Moroccan infrastructure used for operations – 105.156.109[.]227, 196.65.139[.]51, and many other Morocco-hosted IPs (see additional list).
- [IP Addresses] Potential US proxies/compromised hosts – 70.187.192[.]236, 72.49.91[.]23.
- [ASN / Org] Associated Moroccan ISPs/ASNs – MT-MPLS, ASMedi, MAROCCONNECT used as attribution signals.
- [URL Patterns] Phishing URL formats used to spoof organizations – examples: hxxps://[brand-name].com@*.*/portal/, hxxps://*.[brand-name].servicenow.*/*access (used to disguise true destination and mimic legit portals).
- [Email Artefacts] Malicious mailbox rules and moved mail – examples: automatic forwarding rules to attacker-controlled addresses, moved Sent Items to Deleted Items to hide phishing traces.
Read more: https://unit42.paloaltonetworks.com/cloud-based-gift-card-fraud-campaign/