State-sponsored APT activity originating in the Middle East focuses on long-term infiltration and intelligence collection using spear-phishing, malicious documents, and abuse of legitimate RMM tools. Defensive emphasis is placed on endpoint behavior-based EDR to detect post-execution activity and persistent misuse of legitimate administration platforms. #MuddyWater #Atera
Tag: INITIAL ACCESS

Thieves stole over $20 million from compromised ATMs last year using ATM jackpotting, a malware-assisted technique that forces machines to dispense cash without bank authorization. The FBI warns of more than 1,900 incidents since 2020 (700+ in 2025), noting Ploutus exploits the XFS API and listing digital and physical indicators for…

A 45-year-old Romanian national, Catalin Dragomir, pleaded guilty to hacking Oregon’s Office of Emergency Management in June 2021, selling administrative access on cybercriminal platforms and exposing an employee’s personal data. He admitted to breaching 10 other U.S. companies causing at least $250,000 in losses and faces up to seven years in…
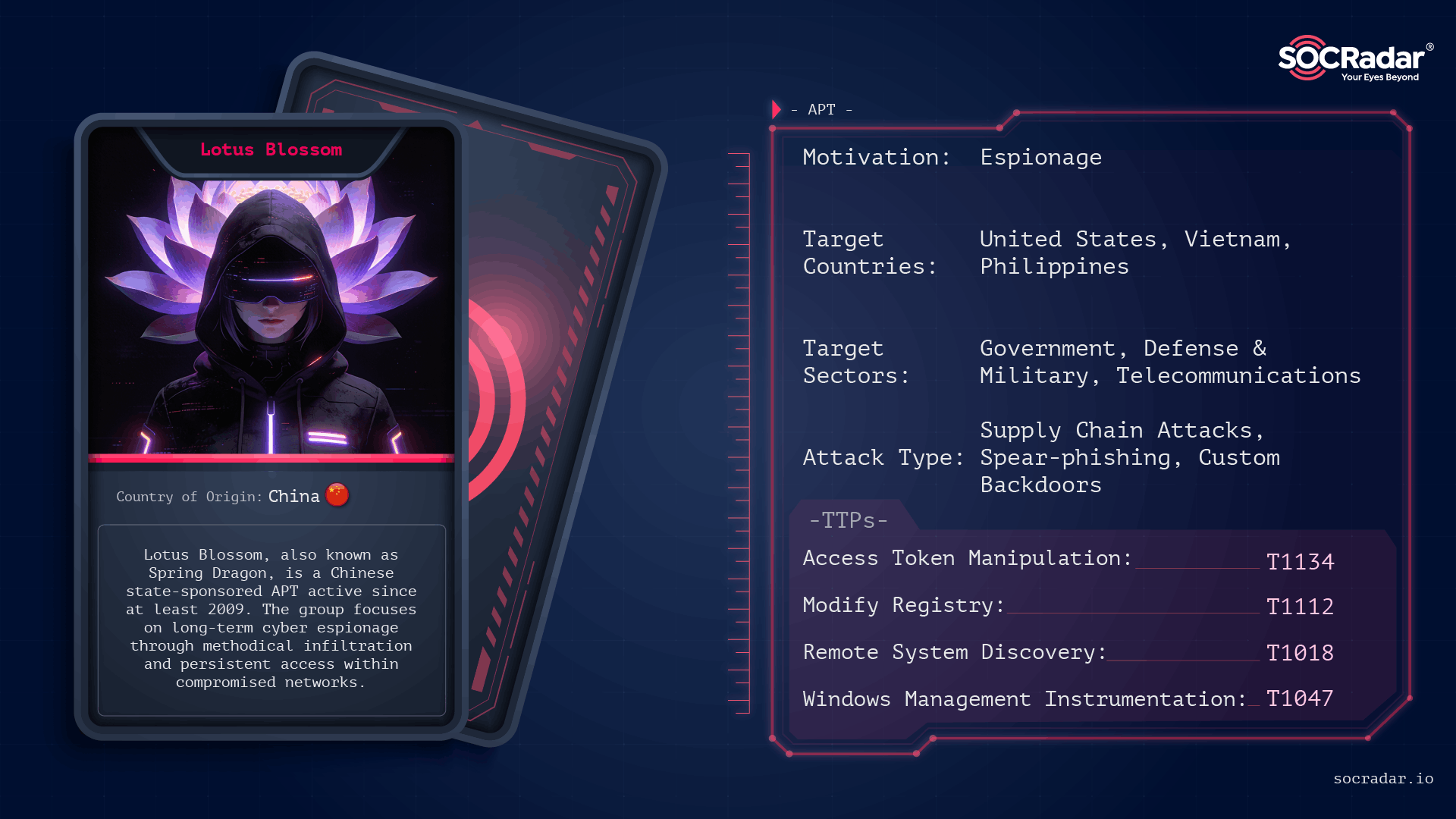
Lotus Blossom is a long-running, China-attributed APT that evolved from spear-phishing and watering-hole campaigns into sophisticated supply-chain compromises and targeted espionage using custom implants like Elise, Sagerunex, Hannotog, and Chrysalis. The group’s Notepad++ update-channel compromise and prior attacks against diplomatic, military, and maritime infrastructure demonstrate a “low-and-slow” intelligence collection approach emphasizing DLL sideloading, living-off-the-land techniques, and clandestine persistence. #LotusBlossom #Chrysalis
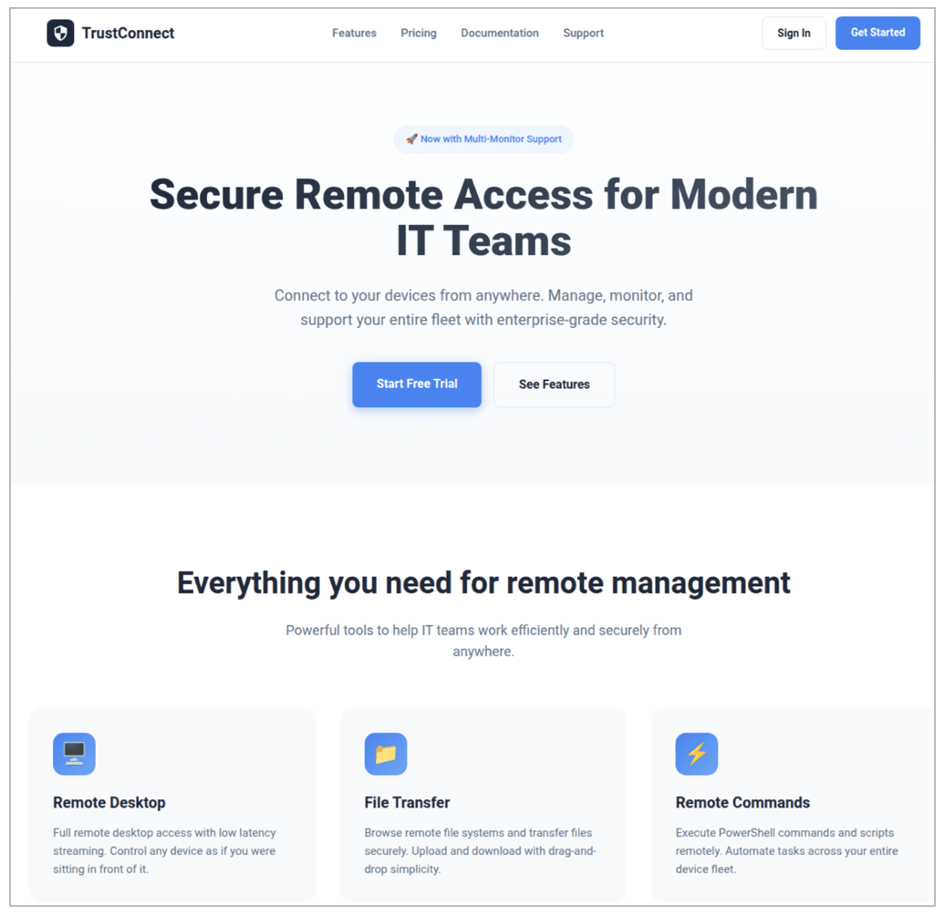
Proofpoint identified a new malware-as-a-service (MaaS) called TrustConnect that masqueraded as a legitimate remote monitoring and management (RMM) tool, used an EV code signing certificate to sign branded installers, and provided a web-based C2/dashboard with automated payload generation and a $300/month subscription model. Proofpoint disrupted the TrustConnect infrastructure (C2 domain trustconnectsoftware[.]com…
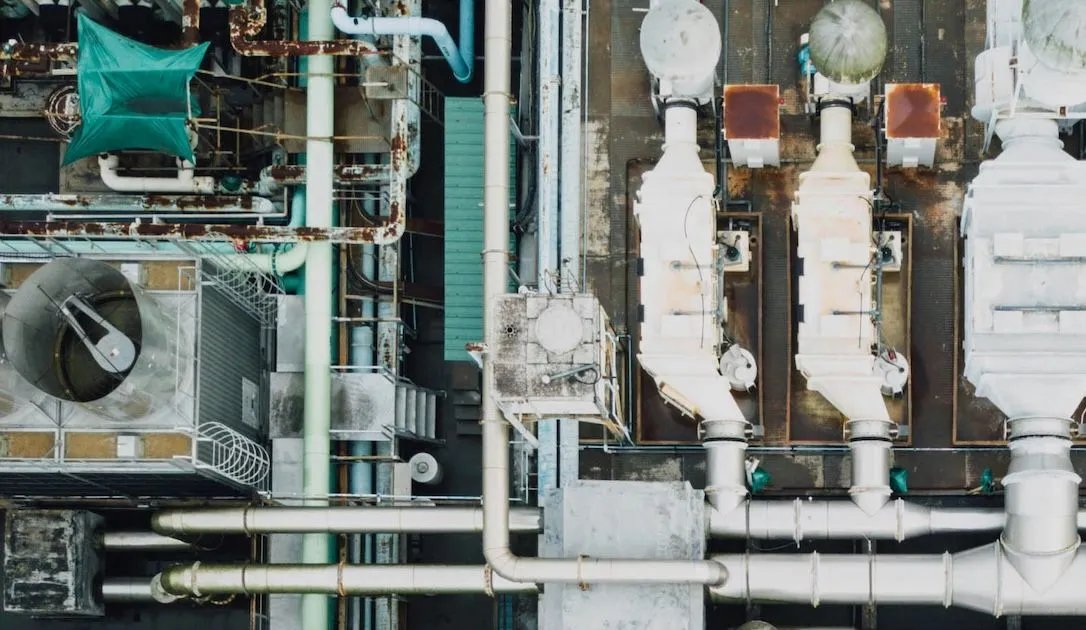
Dragos reports that Chinese-linked threat actor Volt Typhoon continued compromising U.S. utilities through 2025, embedding in operational technology networks to pre-position for disruptive attacks. Researchers warn many compromises—especially in smaller water-sector utilities—may never be found, with initial access groups like SYLVANITE handing breaches to Volt Typhoon. #VoltTyphoon #SYLVANITE…
CVE-2026-1731 is a critical pre-authentication remote code execution vulnerability in BeyondTrust Remote Support’s thin-scc-wrapper WebSocket handler that Unit 42 has observed being actively exploited to deploy web shells, backdoors (including SparkRAT and VShell), create accounts, move laterally, and exfiltrate data across multiple sectors and countries. CISA added the vulnerability to its…

Modern infostealers harvest credentials along with browser cookies, browsing history, and system files, enabling attackers to tie technical data back to real people and organizations. Specops research of 90,000+ infostealer dumps (800M+ rows) shows credential reuse and session data let attackers escalate personal compromises into enterprise breaches, and continuous Active Directory scanning with Specops Password Policy can block known-compromised credentials to reduce that risk. #SpecopsPasswordPolicy #LinkedIn

Dragos’ 2025 report warns that three new OT-focused threat groups emerged while a Beijing-linked crew continued compromising cellular gateways, routers, and US electric, oil, and gas networks. The report details Voltzite’s long-term embedding in utility control systems, use of Sierra Wireless AirLink devices and the JDY botnet, and the roles of…

An initial access broker using the handle Big-Bro listed an auction claiming to sell domain administrator access to an unidentified Peruvian logistics and business services company with estimated revenue of about $10 million. The listing identifies a compromised Fortinet VPN appliance as the access vector and shows an auction starting at…

Attack Discovery, Workflows, and Agent Builder were combined to automatically detect, confirm, and triage a Chrysalis backdoor campaign delivered via a Notepad++ update supply-chain compromise, collapsing dozens of alerts into a single verified incident and creating a case and Slack channel with on-call responders already added. The automation verified C2, performed VirusTotal checks, ran ES|QL hunts, and executed incident actions (isolation, user suspension, IOC sweeps) in under four minutes instead of hours. #Chrysalis #LotusBlossom

The article describes how a mature underground access economy commoditizes remote credentials, infostealer logs, breach databases, and web shells, letting specialists trade and monetize each part of the attack chain. This industrialized market features products like Fortinet VPN credentials, infostealer families (e.g., Redline), and operators such as DAISY CLOUD that sell…

GrayCharlie, active since mid-2023 and overlapping with SmartApeSG, compromises WordPress sites to inject externally hosted JavaScript that redirects visitors to NetSupport RAT payloads delivered via fake browser update pages or ClickFix lures, often resulting in Stealc and SectopRAT follow-on deployments. Insikt Group mapped extensive infrastructure tied to MivoCloud and HZ Hosting Ltd, identified multiple NetSupport RAT C2 clusters and staging domains, and observed a likely supply‑chain compromise impacting numerous US law firm websites. #GrayCharlie #NetSupportRAT

Flare researchers observed threat actors rapidly sharing proof-of-concept exploits, offensive tools, and stolen administrator credentials for SmarterMail vulnerabilities CVE-2026-24423 and CVE-2026-23760, leading to automated mass exploitation and confirmed ransomware activity. Incidents including a SmarterTools breach and ties to the Warlock cluster highlight that email servers are identity-critical and require urgent patching, segmentation, and enhanced monitoring. #SmarterMail #CVE-2026-24423

Acronis TRU uncovered a targeted espionage campaign named CRESCENTHARVEST that uses Farsi-language protest lures to trick victims into opening malicious .LNK shortcuts and install a multi-module stealer/RAT. The implant chain relies on DLL sideloading via a signed Google binary, extracts browser app‑bound keys, logs keystrokes and exfiltrates data to a C2 in Riga. #CRESCENTHARVEST #AcronisTRU