CharlieKirk Grabber is a Python-based Windows infostealer that performs rapid “smash-and-grab” credential harvesting, system reconnaissance, and immediate exfiltration using legitimate Windows utilities and multithreading to minimize runtime. It stages browser credentials, Discord tokens, Wi‑Fi and game session artifacts, compresses them, uploads the archive to GoFile, and sends the download link via Discord or Telegram for attacker retrieval. #CharlieKirk #GoFile
Tag: DEFENSE EVASION

Elastic Security Labs discovered a multi-stage ClickFix campaign that compromises legitimate websites to deliver a five-stage chain culminating in a custom native RAT called MIMICRAT. The attack uses an obfuscated PowerShell downloader with ETW and AMSI bypass, a Lua-based in-memory loader and Meterpreter-like shellcode, and a C++ implant with token impersonation and SOCKS5 tunneling. #MIMICRAT #ClickFix
CVE-2026-1731 is a critical pre-authentication remote code execution vulnerability in BeyondTrust Remote Support’s thin-scc-wrapper WebSocket handler that Unit 42 has observed being actively exploited to deploy web shells, backdoors (including SparkRAT and VShell), create accounts, move laterally, and exfiltrate data across multiple sectors and countries. CISA added the vulnerability to its…

Attack Discovery, Workflows, and Agent Builder were combined to automatically detect, confirm, and triage a Chrysalis backdoor campaign delivered via a Notepad++ update supply-chain compromise, collapsing dozens of alerts into a single verified incident and creating a case and Slack channel with on-call responders already added. The automation verified C2, performed VirusTotal checks, ran ES|QL hunts, and executed incident actions (isolation, user suspension, IOC sweeps) in under four minutes instead of hours. #Chrysalis #LotusBlossom

Sinobi is a Ransomware-as-a-Service operation that emerged in mid-2025 and appears to be a rebrand or successor to the Lynx and INC Ransom families based on significant code overlap. The group uses a closed affiliate model and double-extortion tactics—gaining access via compromised credentials and CVE exploits, exfiltrating data with Rclone, and encrypting files with Curve-25519/AES-128-CTR to demand payment. #Sinobi #Lynx
In July 2025 a SEO-poisoning campaign redirected users searching for ManageEngine OpManager to a malicious site (opmanager.pro) that delivered a trojanized MSI installer, which installed Bumblebee and established HTTPS C2 via DGA domains. The actor dumped domain credentials, created privileged accounts, used remote access tools and SSH tunneling for persistence and exfiltration, and ultimately deployed Akira ransomware across parent and child domains. #Bumblebee #Akira
The intrusion began with a valid RDP login using pre-compromised credentials and progressed through rapid discovery, lateral movement, and persistent account creation before data exfiltration and a final ransomware deployment. The actor exfiltrated archives to temp.sh and deployed Lynx ransomware, leveraging infrastructure tied to Railnet LLC/Virtualine. #Lynx #RailnetLLC
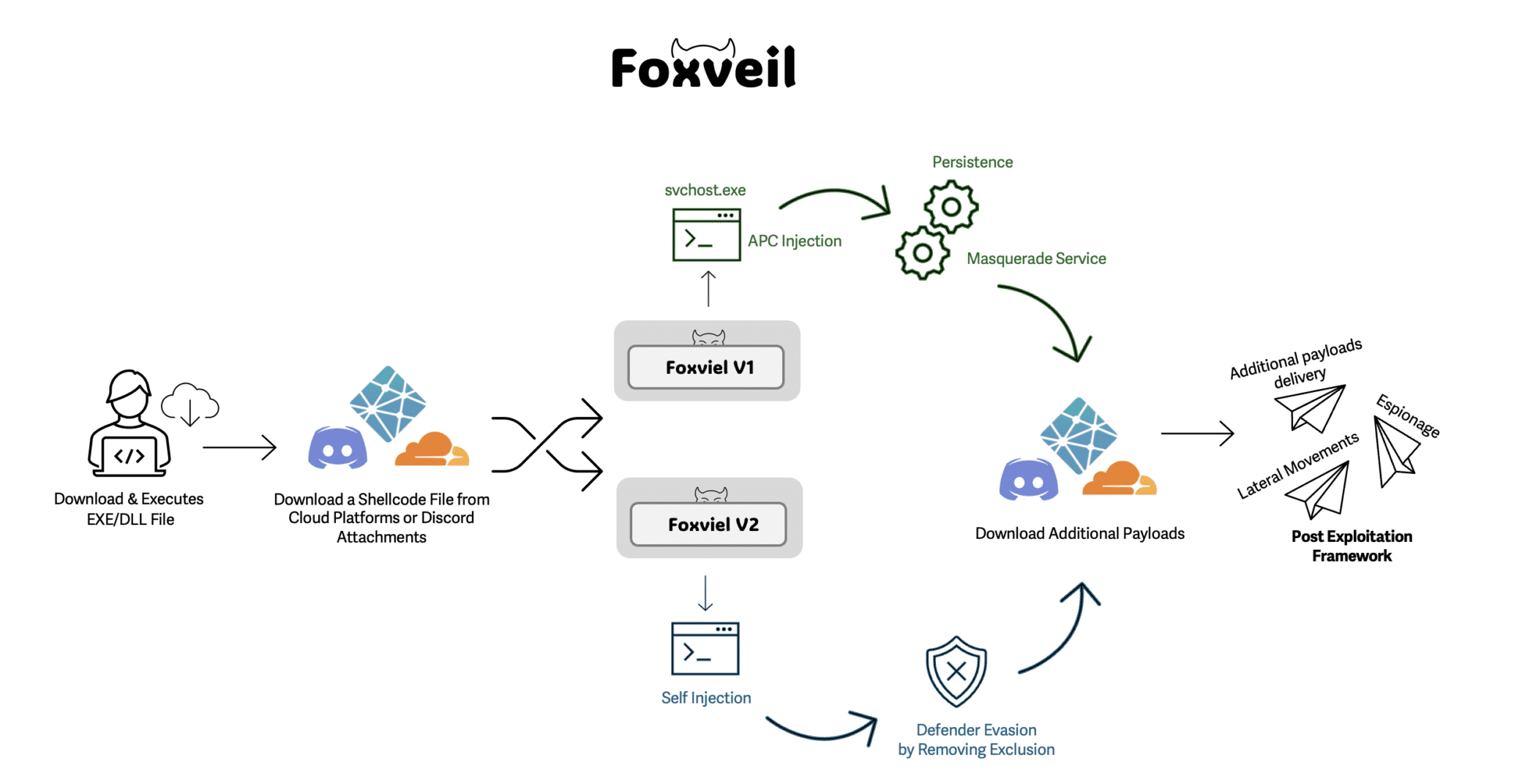
Foxveil is a newly identified initial-stage loader active since August 2025 that retrieves Donut-generated shellcode from trusted hosting platforms (Cloudflare Pages, Netlify) and occasionally Discord attachments, operating in two variants with different injection and persistence techniques. It uses in-memory injection (Early Bird APC in v1, self-injection in v2), service/SysWOW64-based persistence, and a runtime string-mutation routine to frustrate analysis; Cato’s SASE platform blocks the loader before staged payloads execute. #Foxveil #Cloudflare

OpenClaw is an agentic AI platform that runs locally with deep system access and an extensible third‑party “skill” ecosystem, enabling file management, workflow automation, and direct shell command execution. Security researchers have identified widespread malicious skills (notably the ClawHavoc campaign) and critical vulnerabilities such as CVE-2026-25253 that enable credential theft, data exfiltration, and remote code execution, prompting mitigations like VirusTotal scanning, Clawdex detection, and blocking via Iru. #OpenClaw #ClawHavoc

Acronis TRU analyzed LockBit 5.0, a cross‑platform ransomware family (Windows, Linux, ESXi) that uses XChaCha20 and Curve25519 encryption, random per‑file extensions, and shared execution/encryption logic while applying extensive defense‑evasion techniques on Windows. The report also links LockBit infrastructure to a SmokeLoader‑associated IP and documents double‑extortion exfiltration and enterprise/virtualization targeting (including Proxmox and ESXi). #LockBit #SmokeLoader
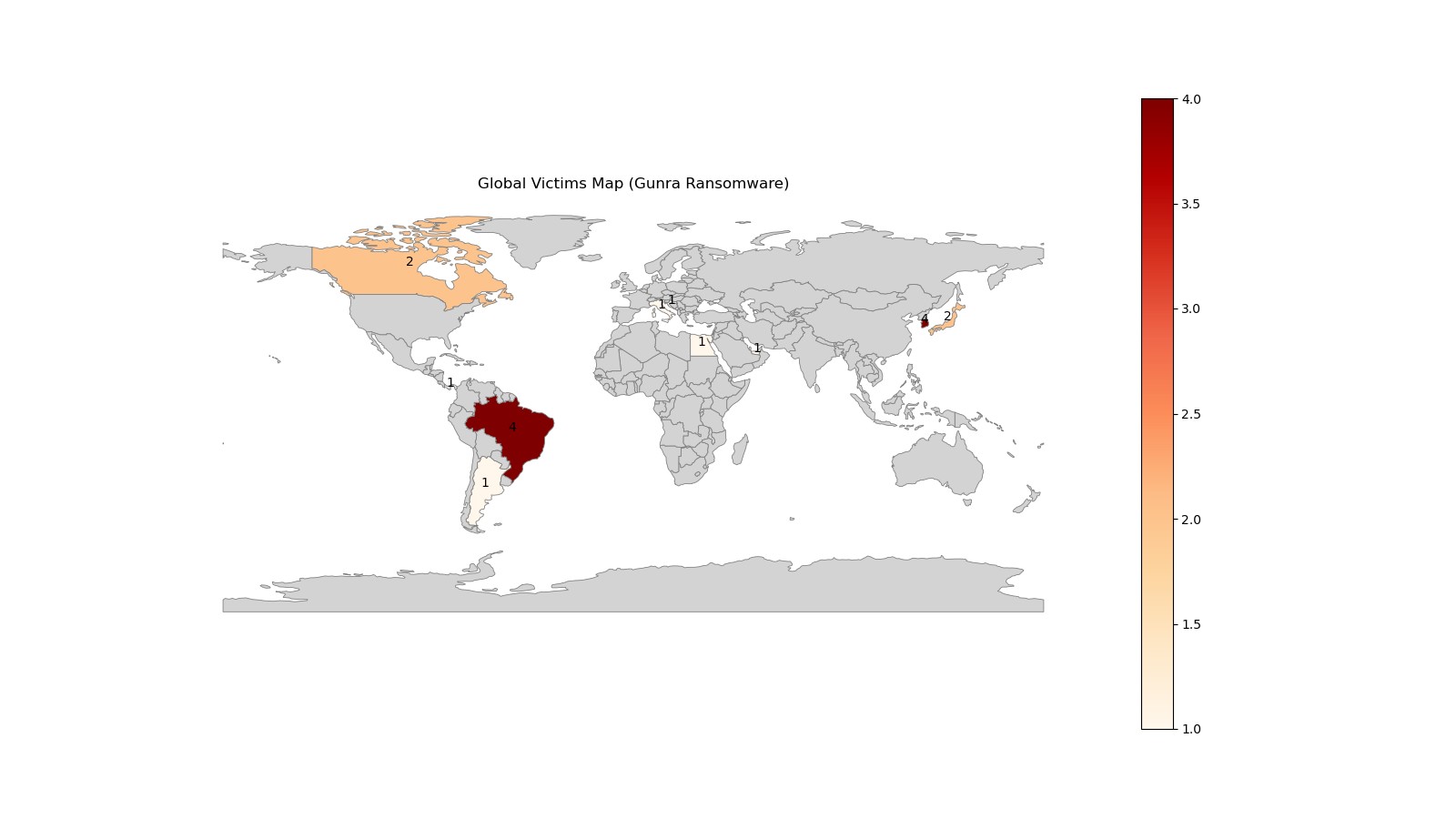
CloudSEK researchers infiltrated a newly launched Gunra affiliate program in January 2026, obtaining RaaS management panel credentials and a live ransomware sample for detailed technical analysis. The Gunra locker is an offline-capable, multi-threaded encryptor that uses per-file ChaCha20 keys protected with RSA-4096, selective system exclusions, .ENCRT renaming, and a Tor-based payment portal. #Gunra #CloudSEK

Fancy Bear (APT28) remains an active Russian state‑aligned espionage actor that quickly adopts newly disclosed vulnerabilities and uses spear‑phishing and credential harvesting to maintain long‑term access to government, defense, energy, and communications targets. The group recently weaponized a Microsoft Office vulnerability to compromise organizations in Eastern Europe and the EU, demonstrating a shift toward lightweight, high‑ROI tradecraft. #FancyBear #CVE-2026-21509
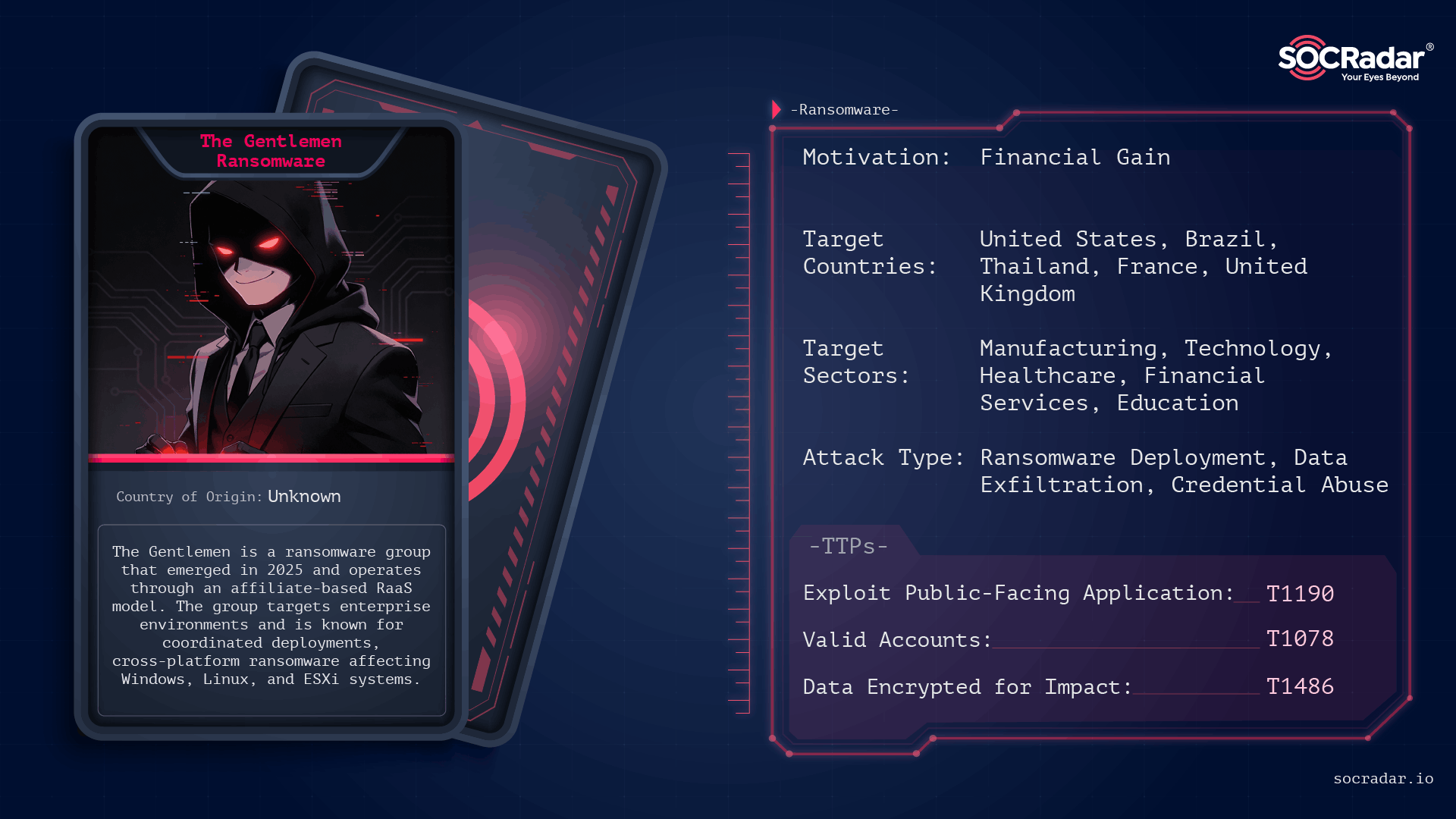
The Gentlemen is an operationally disciplined ransomware group first observed in mid-to-late 2025 that conducts double‑extortion attacks across Windows, Linux, NAS, BSD, and ESXi environments using password‑protected, operator-driven builds. Their campaigns leverage exposed internet-facing services and compromised administrative credentials, and victims have been publicly listed on a Dark Web leak site. #TheGentlemen #ESXi
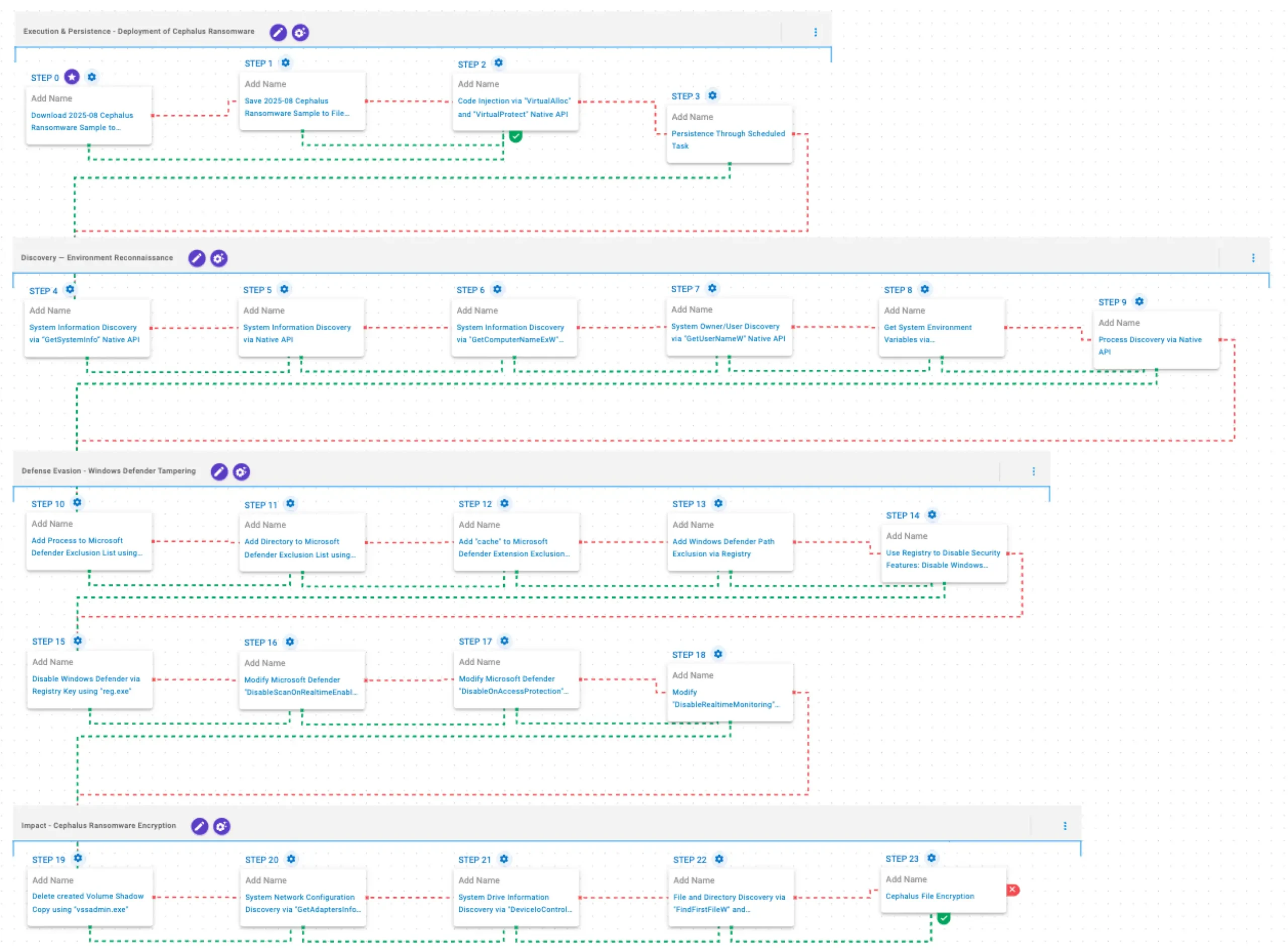
Cephalus is a Go-developed ransomware family observed from June 2025 that gains initial access mainly through exposed RDP without MFA, often using stolen credentials, and follows a double-extortion model by exfiltrating sensitive data prior to encryption. AttackIQ published an emulation of Cephalus TTPs to help organizations validate controls and test detection/prevention…
![Threat Research | Weekly Recap [08 Feb 2026] Threat Research | Weekly Recap [08 Feb 2026]](https://www.hendryadrian.com/tweet/image/WeeklyRecap.png)
Cybersecurity Threat Research ‘Weekly’ Recap: the report surveys supply-chain compromises, ransomware/defense evasion, infostealers, targeted espionage, cloud and identity threats, phishing, vulnerabilities and detection, labs automation and resilience guidance. It highlights notable campaigns and families such as the Notepad++ supply-chain attack, GlassWorm on Open VSX, dYdX npm/PyPI abuse, DYNOWIPER in Polish energy, Black Basta kernel-driver evasion, SonicWall SSLVPN intrusion, APT28 and Shadow Campaigns, Amaranth-Dragon, Transparent Tribe, Stan Ghouls, Prometei, ShinyHunters, NGOSS and ZHGUI breaches, plus attempts at web-infra abuse (Quest KACE, NGINX hijacking, CrashFix/ClickFix) and AI-assisted cloud intrusion via Amazon Bedrock. #NotepadPlusPlus #GlassWorm #OpenVSX #dYdX #DYNOWIPER #BlackBasta #SonicWall #APT28 #ShadowCampaigns #AmaranthDragon #TransparentTribe #StanGhouls #Prometei #ShinyHunters #NGOSS #ZHGUI #QuestKACE #CrashFix #ClickFix #GOAD #NGINX #Baota #AmazonBedrock #DetectionsAsCode