Zscaler ThreatLabz identified BlackForce, a commercially marketed phishing kit first seen in August 2025 that steals credentials and performs Man‑in‑the‑Browser attacks to capture one‑time tokens and bypass MFA. The kit employs evasion techniques (user‑agent/ISP blocklists, mobile‑only filtering, and obfuscated client code in later versions), persistent sessionStorage state, and a dual C2/Telegram exfiltration architecture while impersonating brands like Netflix and Disney. #BlackForce #Telegram
Category: Threat Research
CastleRAT is a Remote Access Trojan first observed in March 2025 that exists in two main builds (Python and compiled C), the latter being stealthier and capable of keystroke capture, screen/video capture, plugin loading, and UAC bypass. Splunk Threat Research Team analyzed the C variant, documenting RC4‑based C2 communication, system info…
Banshee is a macOS-native stealer offered as a MaaS that phishes the user’s login password via a fake System Preferences dialog to decrypt the Keychain and harvest browser credentials, cookies, notes, and targeted files before quickly exfiltrating them. It validates passwords with dscl in real-time, collects Keychain plus browser profiles, stages…
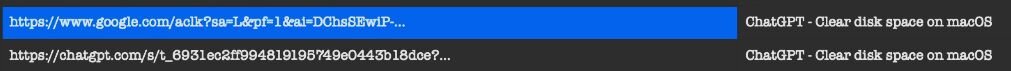
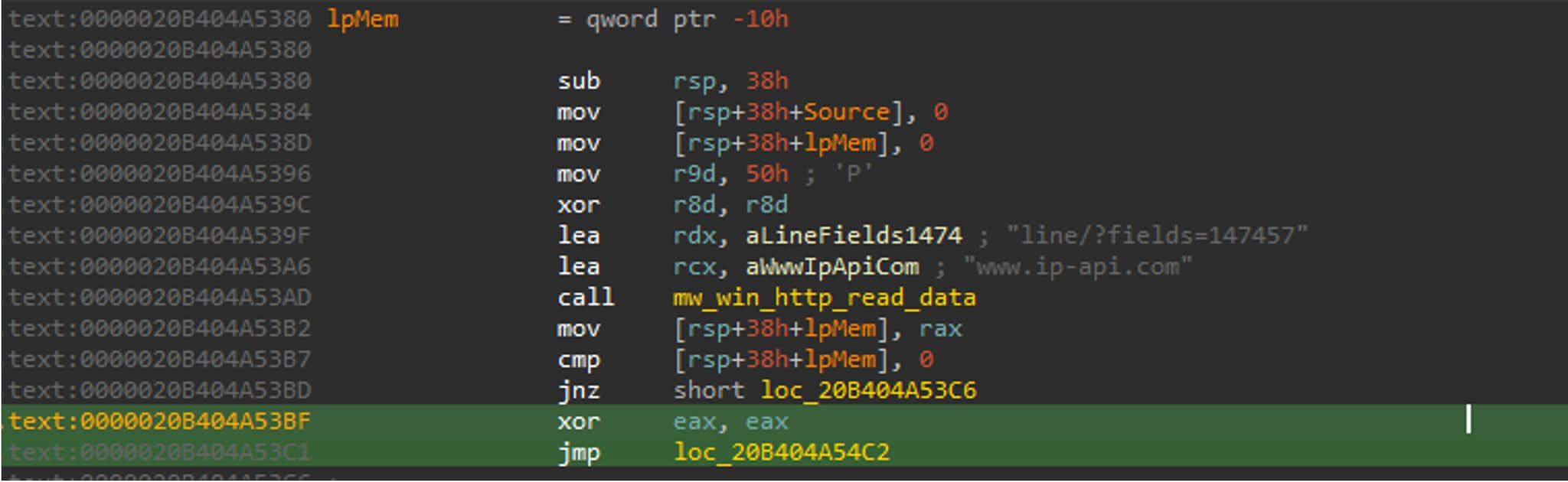
Attackers poisoned search results to surface malicious ChatGPT and Grok conversations that instruct macOS users to copy-paste a Terminal one-liner which downloads and deploys an AMOS stealer. The campaign abuses platform and format trust to harvest credentials, escalate to root, persist via a LaunchDaemon, and exfiltrate wallet, browser, and keychain data. #AMOS #macOS
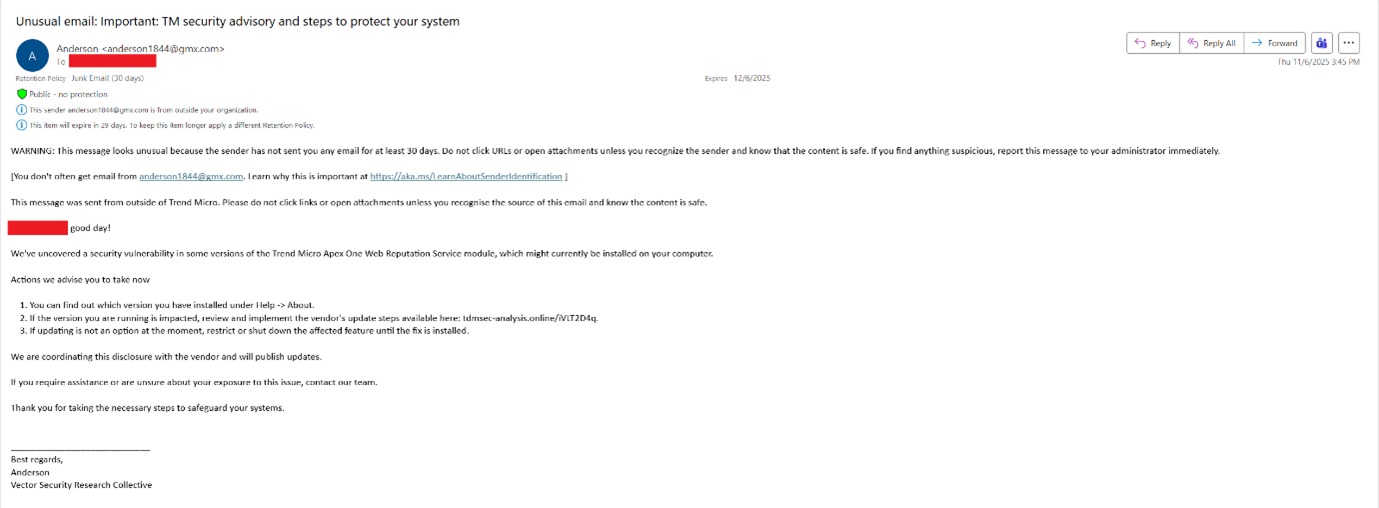
In November 2025 a targeted spear-phishing campaign used Trend Micro–themed lures and malicious redirects to deliver browser exploits and a multi-stage payload chain against executives across defense, energy, chemical, cybersecurity, and ICT sectors. Trend Vision One detected and stopped the activity early in the kill chain, preventing final payload delivery; the…

CISA, the FBI, the NSA, and partner agencies released a joint Cybersecurity Advisory on December 9, 2025, warning that pro‑Russia hacktivist groups are exploiting minimally secured, internet‑facing VNC connections to access OT/ICS devices in critical infrastructure sectors including Water and Wastewater, Food and Agriculture, and Energy. The advisory names groups such…
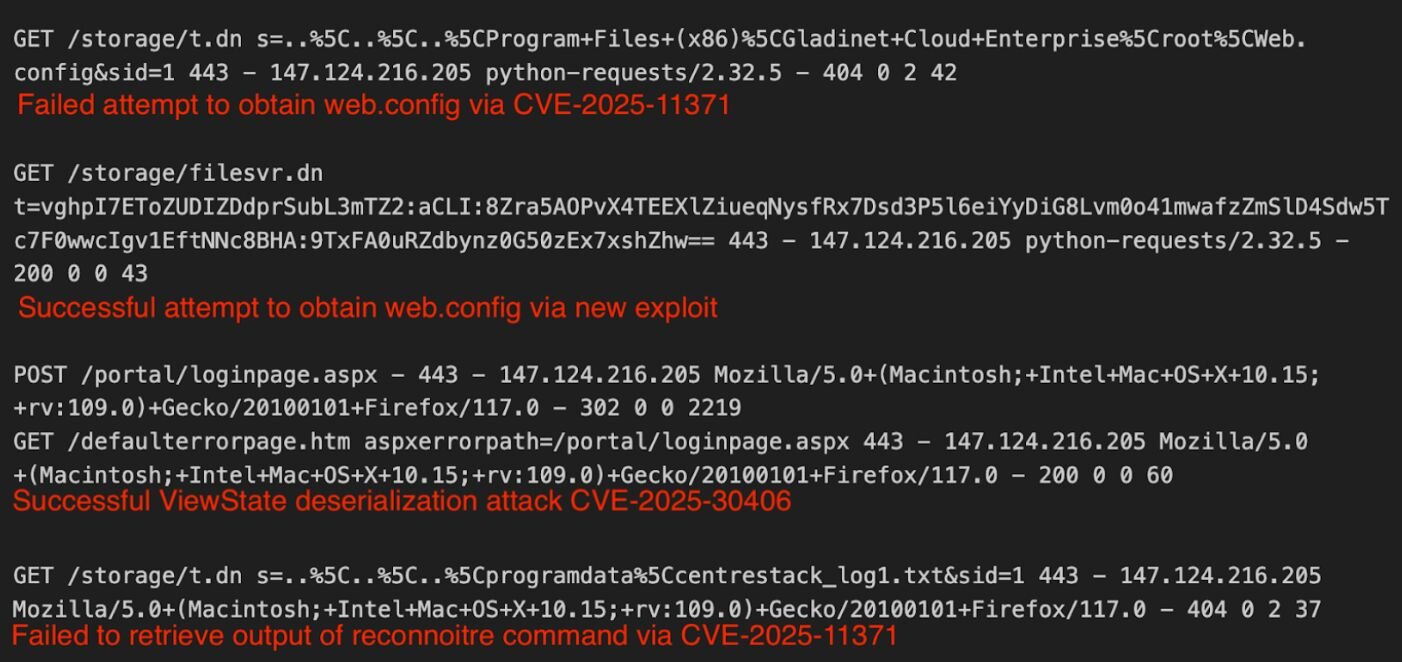
The article describes a critical CentreStack/Triofox vulnerability where a static, predictable machine key allowed attackers to decrypt and forge encrypted access tickets to retrieve sensitive files like web.config. Huntress observed exploitation attempts (CVE-2025-11371) from IP 147.124.216[.]205 and recommends immediate patching to version 16.12.10420.56791 and rotation of the machineKey. #Gladinet #CentreStack

CYFRIMA uncovered a WhatsApp-distributed fraud campaign using a malicious “RTO Challan / e-Challan” Android app that employs a two-stage dropper, heavy obfuscation, and a custom VPN to persistently control devices and exfiltrate data. The malware harvests Aadhaar/PAN, SMS/OTP, telephony and banking credentials via a fake payment interface and communicates with obfuscated C2 domains to enable real-time financial fraud and identity theft. #RTOChallan #jsonserv_xyz

FortiGuard IR discovered historical evidence of deleted malware and attacker activity inside the AutoLogger-Diagtrack-Listener.etl ETW file on a compromised Windows Server, revealing that KernelProcess → ProcessStarted events can retain command-line and execution details for binaries that were later removed. The AutoLogger-Diagtrack-Listener.etl file’s population appears controlled by undocumented DiagTrack triggers and is inconsistently populated across Windows builds, limiting its immediate reliability as a forensic source. #AutoLogger-Diagtrack-Listener.etl #GMER
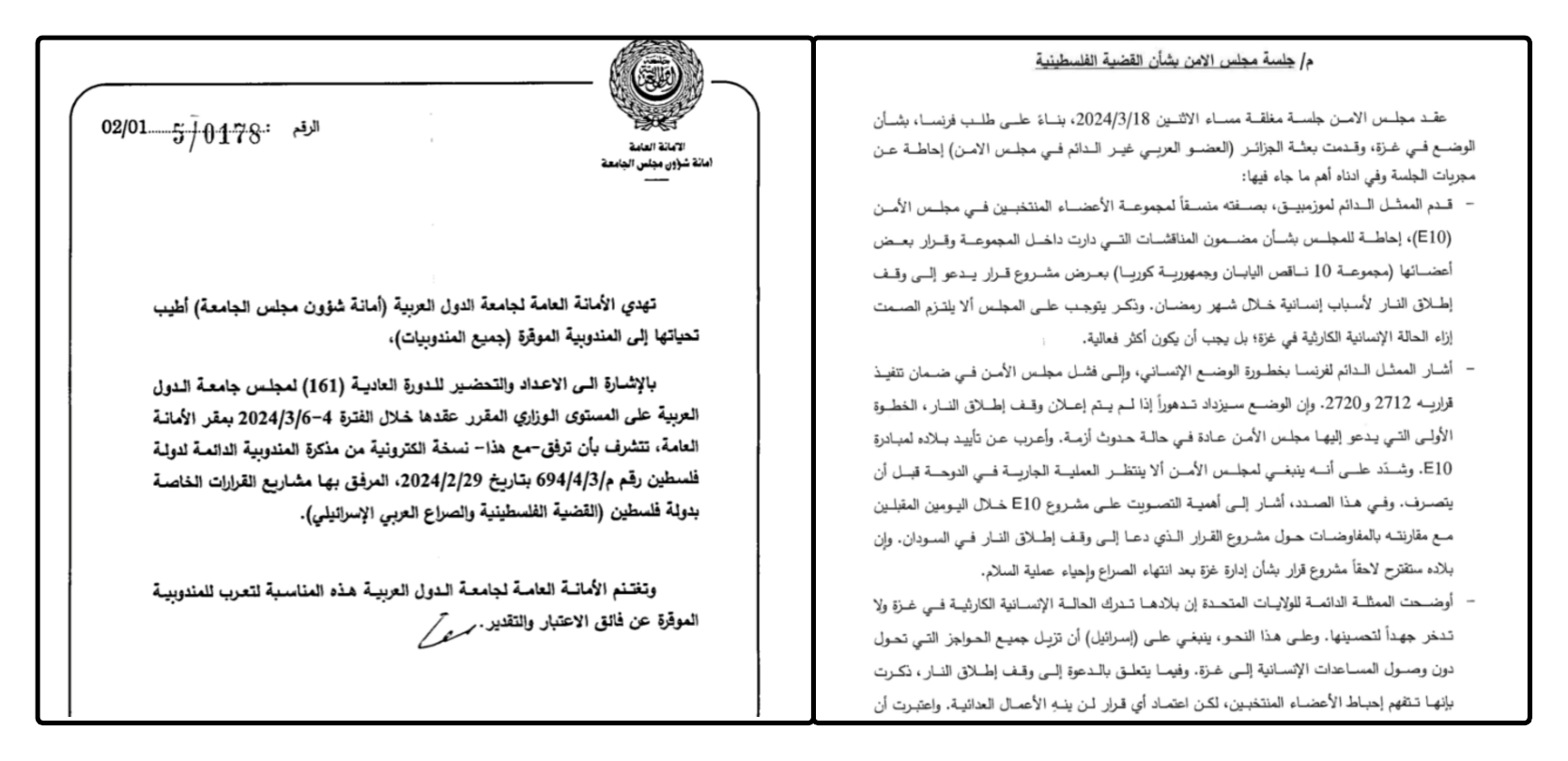
Ashen Lepus conducted a long-running espionage campaign across Middle Eastern government and diplomatic targets, evolving its tooling and OpSec to deliver a new modular .NET malware suite named AshTag that uses DLL side-loading, in-memory execution, and encrypted payloads embedded in benign webpages. The group shifted C2 infrastructure to legitimate-looking subdomains, staged…

GOLD SALEM used SharePoint exploits (including the ToolShell zero-day chain) and attacker-hosted Cloudflare Workers subdomains to stage tools and gain access to networks, later deploying Velociraptor as a precursor to ransomware activity. These intrusions led to Warlock, LockBit, and Babuk encryptions, with tool-staging domains such as files[.]qaubctgg[.]workers[.]dev and C2 infrastructure like velo[.]qaubctgg[.]workers[.]dev observed in the activity. #Warlock #GOLDSALEM

The article analyzes three distinct browser-hijacking techniques—modifying browser preference files, remotely controlling browsers by simulating key presses (a BRAT), and abusing Chromium command-line switches combined with registry tweaks and scheduled scripts—to illustrate detection and mitigation gaps. It provides sample file names, file paths, and hashes tied to AppSuite and other hijackers to help analysts create detections. #TamperedChef #BRAT

Datadog analyzed an active phishing campaign that impersonates Microsoft 365 and Okta pages to hijack SSO flows, capture credentials and session cookies, and bypass non-phishing-resistant MFA. The campaign uses lookalike Okta domains, two-stage phishing pages, on-page JavaScript that hooks fetch/XHR to rewrite federation redirects and exfiltrate cookies, and a variety of phishing infrastructure and lures such as benefits-themed emails and PDFs #Okta #Microsoft365
Researchers disclosed CVE-2025-55182 (React4Shell), a critical deserialization flaw in React Server Components that permits remote command execution and arbitrary file read/write with CVSS 10.0. A public PoC and rapid exploit attempts observed in Kaspersky honeypots have led to broad weaponization delivering XMRig, Mirai/Gafgyt variants and the RondoDox botnet, prompting immediate patching and mitigation recommendations. #React4Shell #RondoDox
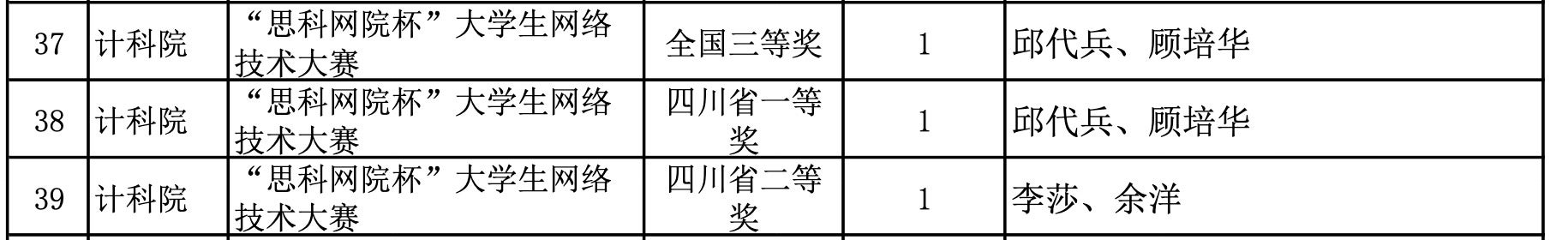
Salt Typhoon, linked to Yuyang (余洋) and Qiu Daibing (邱代兵), compromised more than 80 telecommunications companies worldwide to collect unencrypted calls and texts and to breach CALEA lawful-intercept systems. The report traces the operators to participation in the Cisco Networking Academy and a 2012 Cisco Network Academy Cup, highlighting how vendor training programs can inadvertently enable offensive capabilities against those vendors’ products. #SaltTyphoon #Cisco
