CastleRAT is a Remote Access Trojan first observed in March 2025 that exists in two main builds (Python and compiled C), the latter being stealthier and capable of keystroke capture, screen/video capture, plugin loading, and UAC bypass. Splunk Threat Research Team analyzed the C variant, documenting RC4‑based C2 communication, system info and clipboard exfiltration, remote shell via anonymous IPC, and detection rules to identify and mitigate the threat. #CastleRAT #Splunk
Keypoints
- CastleRAT observed around March 2025, available as a lightweight Python build and a more feature-rich compiled C build.
- Both builds use a hardcoded RC4 key for encrypting C2 traffic; the C build supports additional capabilities like plugins, keylogging, and screen/video capture.
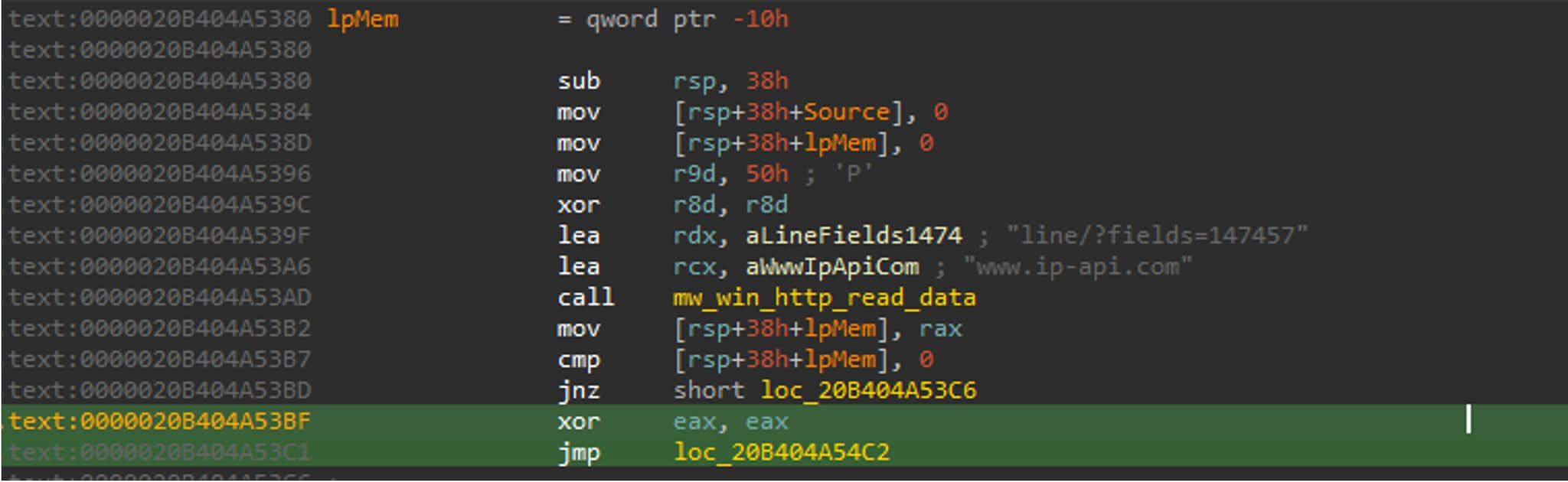
- The malware collects system information (computer name, username, machine GUID, public IP via www[.]ip-api[.]com) and beacons to a remote C2 to receive commands or additional payloads.
- Exfiltration techniques include clipboard scraping and hijacked paste actions, RC4‑encrypted exfil of keylogs, and use of dead‑drop resolvers (e.g., Steam Community pages) for evasive C2 resolution.
- Persistence and privilege escalation techniques include scheduled tasks, rundll32 DLL loading by ordinal, and a UAC bypass via handle duplication/ThreadDebugObject patterns.
- Splunk Threat Research Team produced 16 detections and example SPL queries targeting unusual browser flags, rundll32 ordinal loads, ComputerDefaults.exe spawning, and handle duplication to detect CastleRAT activity.
MITRE Techniques
- [T1082 ] System Information Discovery – CastleRAT gathers host details (computer name, username, machine GUID, product/version) and queries an external IP service for the public IP (‘This CastleRAT client gathers basic system details from a compromised host, including the computer name, username, machine GUID, Product name, and uses the free web service www[.]ip-api[.]com to obtain the public IP.’)
- [T1115 ] Clipboard Data – The RAT collects clipboard contents and exfiltrates them to the attacker, including hijacking paste actions to stealthily transfer data (‘CastleRAT launches multiple threads … one of those techniques is the collection of Clipboard data.’).
- [T1105 ] Ingress Tool Transfer – CastleRAT downloads DLL plugins from C2, decrypts them with RC4, and launches them using rundll32.exe (‘handles the decryption of CastleRAT DLL plugins downloaded from its C2 server and then launches those plugins using the Windows utility rundll32.exe.’)
- [T1036 ] Masquerading – The malware sets an environment variable and drops files to appear like legitimate Python/Java components to hide monitored data (‘reads and sets an environment variable that is disguised to appear like a legitimate Python or Java component’).
- [T1056.001 ] Keylogging – CastleRAT installs keyboard hooks (SetWindowsHookEx), captures keystrokes to a keylog file, RC4‑encrypts it, and exfiltrates the data (‘intercepts keyboard input, writes it to a keylog.txt file, encrypts that file with RC4, and then exfiltrates the encrypted data’).
- [T1559 ] Inter-Process Communication – The RAT spawns shells with redirected anonymous pipes to provide an interactive remote shell without visible console windows (‘creates a pair of anonymous pipes and starts the chosen shell with its standard input, output and error handles redirected to those pipes’).
- [T1185 ] Browser Session Hijacking – CastleRAT kills running browsers and relaunches Chromium‑based processes with audio flags to enable muted monitoring/control (‘killing a running browser … and launching a new Chromium‑based process with audio‑related command‑line flags’).
- [T1125 ] Video Capture – The malware enumerates media capture devices via Media Foundation APIs (MFEnumDeviceSources) to discover and initialize webcams/microphones (‘calls MFEnumDeviceSources() API for accessing and enumerating media capture devices’).
- [T1218.011 ] Rundll32 – CastleRAT uses rundll32.exe to load DLL exports by ordinal and to execute plugin code or shell32.dll exports (e.g., opening the Run dialog) (‘execute an interesting shell32.dll export function to open the “run” dialog box.’ )
- [T1053 ] Scheduled Task/Job – The RAT registers a Scheduled Task via PowerShell to run a local copy at system startup for persistence (‘register a Scheduled Task that runs a local copy of the malware at system startup’).
- [T1113 ] Screen Capture – A background thread periodically captures screenshots of the active desktop to harvest displayed sensitive information (‘periodically captures screenshots of the active desktop on the compromised host’).
- [T1102.001 ] Dead Drop Resolver – CastleRAT uses legitimate sites like Steam Community pages as dead‑drop resolvers to host or reference configuration or C2 metadata (‘leverages legitimate external websites such as Steam Community pages as benign-looking dead-drop resolvers’).
- [T1548.002 ] Bypass User Account Control – The malware abuses Appinfo and handle duplication via debug event monitoring and NtDuplicateObject to inherit handles from privileged processes and escalate privileges (‘abuses the Appinfo service UUID … monitors a specific debug event … duplicate via NtDuplicateObject () API’).
Indicators of Compromise
- [File Hash – SHA256] CastleRAT compiled samples – 963c012d56c62093d105ab5044517fdcce4ab826f7782b3e377932da1df6896d, f2ff4cbcd6d015af20e4e858b0f216c077ec6d146d3b2e0cbe68b56b3db7a0be, and 2 more hashes
- [File Hash – SHA256] CastleRAT Python samples – 4ef63fa536134ad296e83e37f9d323beb45087f7d306debdc3e096fed8357395, 282fa3476294e2b57aa9a8ab4bc1cc00f334197298e4afb2aae812b77e755207
- [Domain] External IP lookup used by malware – www[.]ip-api[.]com (used to obtain the host’s public IP for beaconing)
- [File/Process Names] Suspicious or abused system binaries and dropped files – ComputerDefaults.exe, rundll32.exe, keylog.txt, %appdata%/PythonFilee
- [Process Names] Browser targets and relaunch artifacts – chrome.exe, msedge.exe (examples of browsers killed and relaunched with unusual flags like –mute-audio)
Read more: https://www.splunk.com/en_us/blog/security/castlerat-malware-detection-splunk-mitre-attck.html