Researchers disclosed CVE-2025-55182 (React4Shell), a critical deserialization flaw in React Server Components that permits remote command execution and arbitrary file read/write with CVSS 10.0. A public PoC and rapid exploit attempts observed in Kaspersky honeypots have led to broad weaponization delivering XMRig, Mirai/Gafgyt variants and the RondoDox botnet, prompting immediate patching and mitigation recommendations. #React4Shell #RondoDox
Keypoints
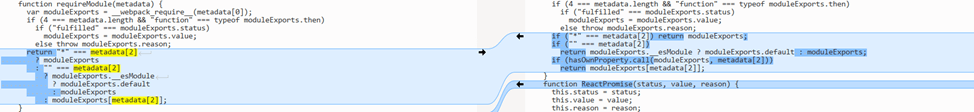
- CVE-2025-55182 is a critical (CVSS 10.0) deserialization vulnerability in React Server Components (Server Actions) enabling remote command execution and file read/write under the server process privileges.
- The flaw is categorized as CWE-502 (Deserialization of Untrusted Data) and is exploitable via a POST request containing a serialized payload to the vulnerable handler.
- Kaspersky honeypots observed exploitation attempts beginning December 5, 2025, with rapid growth in activity by December 8 and ongoing increases.
- Attackers probe targets using simple commands (whoami, bash arithmetic, MD5/Base64 checks) before downloading payloads with wget/curl; many deployments install XMRig miners or botnets like Mirai/Gafgyt and RondoDox.
- RondoDox loader scripts remove competitors, disable AppArmor/SELinux, hide ELF files, and try multiple download methods and 18 architecture-specific builds to infect IoT and x86_64 systems.
- Some campaigns focus on stealing Git and cloud credentials, raising risks of cloud compromise and supply-chain attacks.
- Mitigations: apply vendor patches for affected react-server-dom packages and bundles, block suspicious POST parameters/keywords, scan hosts for indicators of compromise, and rotate credentials.
MITRE Techniques
- [T1059 ] Command and Scripting Interpreter – Used to run probes and verify code execution on targets: ‘they run whoami, perform multiplication in bash, or compute MD5 or Base64 hashes of random strings to verify their code can execute on the targeted machine.’
- [T1059.001 ] PowerShell – PowerShell-based payloads were used on Windows to install crypto miners: ‘some attackers deliver a PowerShell-based Windows payload that installs XMRig, a popular Monero crypto miner.’
- [T1105 ] Ingress Tool Transfer – Attackers download malicious loaders and payloads using command-line clients and BusyBox: ‘they then attempt to download malicious files using command-line web clients like wget or curl’ and ‘sequentially trying three different loaders: wget, curl, and wget from BusyBox.’
- [T1562 ] Impair Defenses – RondoDox neutralizes system security modules and removes ELF traces to evade and eliminate competitors: ‘RondoDox also neutralizes AppArmor and SELinux security modules and employs more sophisticated methods to find and terminate processes with ELF files removed for disguise.’
- [T1078 ] Valid Accounts – Adversaries attempted to steal credentials for repository and cloud access to facilitate further compromise: ‘instead of deploying malware, the adversary attempted to steal credentials for Git and cloud environments.’
Indicators of Compromise
- [URL ] Malware distribution and loader URLs observed in attacks – hxxp://172.237.55.180/b, hxxp://41.231.37.153/rondo[.]x86_64, and 20+ other URLs listed in the report.
- [IP Address ] Hosts serving malicious payloads – 172.237.55.180, 41.231.37.153, and several other IPs (e.g., 51.81.104.115, 23.132.164.54) observed in the sample list.
- [Domain ] C2 / hosting domains used for scripts and payloads – api.hellknight[.]xyz, gist.githubusercontent[.]com/raw/39e943f4de855e2aef12f34324cbf150/setup_c3pool_miner[.]sh, and other domains noted in the indicators.
- [File Name ] Installer and miner scripts referenced in campaigns – 4thepool_miner.sh, setup_c3pool_miner.sh (used to install crypto miners and other payloads).
- [MD5 Hash ] Sample file hashes for detected payloads – 0450fe19cfb91660e9874c0ce7a121e0 (first listed hash), and other hash entries reported.
Read more: https://securelist.com/cve-2025-55182-exploitation/118331/